Numerous HP business laptops and desktops vulnerable to publicly disclosed security bugs
Researchers revealed the details of the six vulnerabilities at Black Hat in August but many laptops, desktops, and workstations remain vulnerable

Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
You are now subscribed
Your newsletter sign-up was successful
A package of six security vulnerabilities impacting the firmware of HP’s business-focused laptops and desktops and some have been left unfixed for months, security researchers said.
Experts at Binarly presented the package of vulnerabilities at the most recent Black Hat conference in August. More than a month after the public disclosure, the vulnerabilities remain unfixed for several HP devices.
The company has submitted 22 vulnerabilities to HP this year, including a package of 16 high-severity flaws in March that also impacted the firmware of enterprise-focused HP products including laptops, desktops, point-of-sale (PoS) systems, and edge computing nodes.
Binarly began notifying HP of the vulnerabilities included in the package of six that were publicly disclosed at Black Hat 2022 as far back as July 2021.
A wide range of HP devices is affected by the flaws, including HP Elite 2-in-1 PCs, HP EliteBook, HP ProBook laptops, HP ZBook workstations, and HP ZHAN notebooks. Some desktops, PoS systems, workstations, and thin clients are also vulnerable.
The patching status for the affected devices varies by each vulnerability, but a significant number of devices remain unpatched across each of the six publicly disclosed flaws.
HP has published three security advisories (1, 2, 3) that cover each of the six flaws found by Binarly, and the patching status for each device can be found in the dropdown menus.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
Firmware vulnerabilities are particularly concerning, for businesses especially, because of the potential significance of the attacks they can facilitate.
If a cyber criminal was able to exploit a UEFI-level vulnerability and install malware at the root of the system, it has the potential to allow a high degree of persistence on the machine and can be difficult to both detect and remove.
Installing UEFI malware or a rootkit would afford an attacker a range of capabilities including the ability to implant a backdoor to the victim’s machine, create new users, remotely control the computer, exfiltrate data, and execute financially-driven campaigns like ransomware, for example.
Binary highlights the devices in its report that have still not received security updates following the public disclosure of the vulnerabilities more than a month ago.
When a vulnerability is publicly disclosed, it means cyber criminals have all the information they need to develop exploits for the flaws. If a device is not patched when a vulnerability is publicly disclosed, a user is then limited in what they can do to prevent an attack.
IT Pro has contacted HP for comment and will update the article if it responds.
Firmware bugs
RELATED RESOURCE
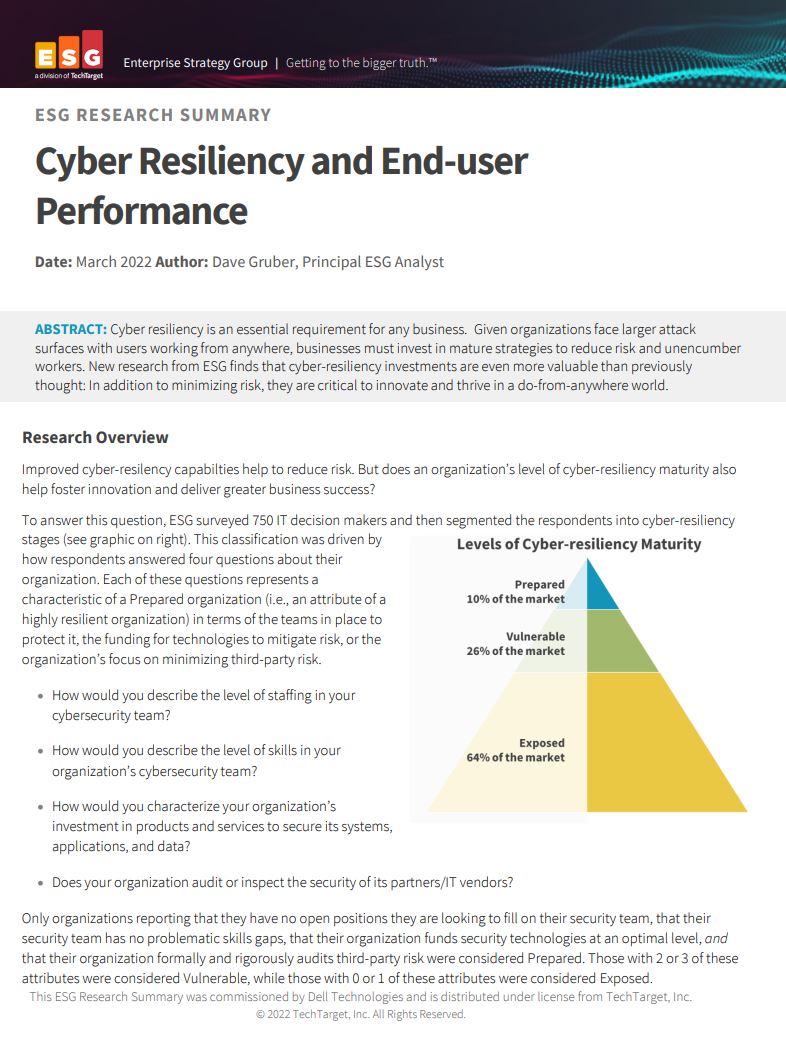
Cyber resiliency and end-user performance
Reduce risk and deliver greater business success with cyber-resilience capabilities
All of the six vulnerabilities are privilege escalation flaws that can allow for arbitrary code execution in System Management Mode (SMM) which runs at a higher level of privileges that the operating system (OS) and the hypervisor.
“Running arbitrary code in SMM additionally bypasses SMM-based SPI flash protections against modifications, which can help an attacker to install a firmware backdoor/implant into BIOS,” said Binarly.
“Such a malicious firmware code in BIOS could persist across operating system re-installs. Additionally, this vulnerability potentially could be used by malicious actors to bypass security mechanisms provided by UEFI firmware (for example, Secure Boot and some types of memory isolation for hypervisors).”
Each of the individual vulnerabilities can lead to the same outcome but affect different components. They are tracked as:
- CVE-2022-23930 – rated 8.2 on the CVSS v3 severity scale - ‘high’
- CVE-2022-31644 – rated 7.5 on the CVSS v3 severity scale - ‘high’
- CVE-2022-31645 – rated 8.2 on the CVSS v3 severity scale - ‘high’
- CVE-2022-31646 – rated 8.2 on the CVSS v3 severity scale - ‘high’
- CVE-2022-31640 – rated 7.5 on the CVSS v3 severity scale - ‘high’
- CVE-2022-31641 – rated 7.5 on the CVSS v3 severity scale - ‘high’

Connor Jones has been at the forefront of global cyber security news coverage for the past few years, breaking developments on major stories such as LockBit’s ransomware attack on Royal Mail International, and many others. He has also made sporadic appearances on the ITPro Podcast discussing topics from home desk setups all the way to hacking systems using prosthetic limbs. He has a master’s degree in Magazine Journalism from the University of Sheffield, and has previously written for the likes of Red Bull Esports and UNILAD tech during his career that started in 2015.
-
 Cohere's Aleph Alpha merger could create a transatlantic sovereign AI powerhouse
Cohere's Aleph Alpha merger could create a transatlantic sovereign AI powerhouseAnalysis The merger between Cohere and Aleph Alpha aims to capitalize on the burgeoning sovereign AI market
-
 Everything you need to know about OpenAI's new workspace agents
Everything you need to know about OpenAI's new workspace agentsNews New ‘workspace agents’ from OpenAI will automate tasks for workers and can be customized for specific roles
-
 Brace yourselves for a vulnerability explosion, Forescout warns
Brace yourselves for a vulnerability explosion, Forescout warnsNews AI advances are helping identify software flaws at record pace and scale, but that's not the good news some would think
-
 ‘It’s not a good look for the PC ecosystem as a whole.” HP to make fix for TPM vulnerability an industry standard
‘It’s not a good look for the PC ecosystem as a whole.” HP to make fix for TPM vulnerability an industry standardJust announced TPM Guard offers important protection against device data theft when attackers gain physical access
-
 Ubuntu vulnerability exposes enterprises to root escalation, complete system compromise
Ubuntu vulnerability exposes enterprises to root escalation, complete system compromiseNews The high-severity Ubuntu vulnerability allows an unprivileged local attacker to escalate privileges through the interaction of two standard system components
-
 DIY hackers are turning to ‘flat-pack’ malware components to speed up attacks and cut costs
DIY hackers are turning to ‘flat-pack’ malware components to speed up attacks and cut costsNews While these malware campaigns are very basic, researchers noted “they still work”
-
 Security agencies issue warning over critical Cisco Catalyst SD-WAN vulnerability
Security agencies issue warning over critical Cisco Catalyst SD-WAN vulnerabilityNews Threat actors have been exploiting the vulnerability to achieve root access since 2023
-
 Millions of developers could be impacted by flaws in Visual Studio Code extensions – here's what you need to know and how to protect yourself
Millions of developers could be impacted by flaws in Visual Studio Code extensions – here's what you need to know and how to protect yourselfNews The VS Code vulnerabilities highlight broader IDE security risks, said OX Security
-
 CVEs are set to top 50,000 this year, marking a record high – here’s how CISOs and security teams can prepare for a looming onslaught
CVEs are set to top 50,000 this year, marking a record high – here’s how CISOs and security teams can prepare for a looming onslaughtNews While the CVE figures might be daunting, they won't all be relevant to your organization
-
 Microsoft patches six zero-days targeting Windows, Word, and more – here’s what you need to know
Microsoft patches six zero-days targeting Windows, Word, and more – here’s what you need to knowNews Patch Tuesday update targets large number of vulnerabilities already being used by attackers