Google exposes 'uniquely personal' access broker behind worst Conti, FIN12 ransomware attacks
Investigation unveils the inner workings of one access broker that helped two of the most-hated ransomware gangs in history

Google’s cyber security research division has unearthed details of initial access brokers (IABs) working on behalf of some of the biggest ransomware gangs in existence.
IABs are groups of cyber criminals that exploit vulnerabilities in organisations and sell that access to the highest bidder so they can launch meaningful cyber attacks without conducting the initial leg work.
The Threat Analysis Group (TAG) observed the EXOTIC LILY IAB operating from at least as far back as September 2021 and has provided access to companies for the likes of Conti and FIN12 so they can launch profitable ransomware attacks.
These types of IAB groups have been operating for some time but have gained popularity in recent years and are approaching the peak of their operational maturity, according to recent reports.
FIN12 and the now-shuttered Conti are among the most infamous ransomware operators of recent times. They have both indiscriminately targeted organisations for financial gain and, unlike other groups, display few ethical boundaries, both having targeted hospitals and healthcare organisations in the past.
The well-resourced EXOTIC LILY group, at the peak of its activity, is said to have targeted upwards of 5,000 emails a day across 650 global organisations, attempting to exploit a Microsoft zero-day vulnerability (CVE-2021-40444) to achieve initial access.
Uniquely personal approach
Google’s TAG said EXOTIC LILY displayed targeted attack techniques such as spoofing companies and employees as a means to gaining trust through email campaigns but “rather uniquely” devoted a considerable amount of time to each target in an attempt to build trust.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
Like the large-scale ransomware gangs it works for, EXOTIC LILY is comprised of many individuals so they can devote time to each target. TAG said the “level of human-interaction is rather unusual for cyber crime groups focused on mass-scale operations”.
TAG said EXOTIC LILY would customise business proposal templates when first contacting organisations rather than relying on just one, a technique requiring more effort than typically observed with such groups.
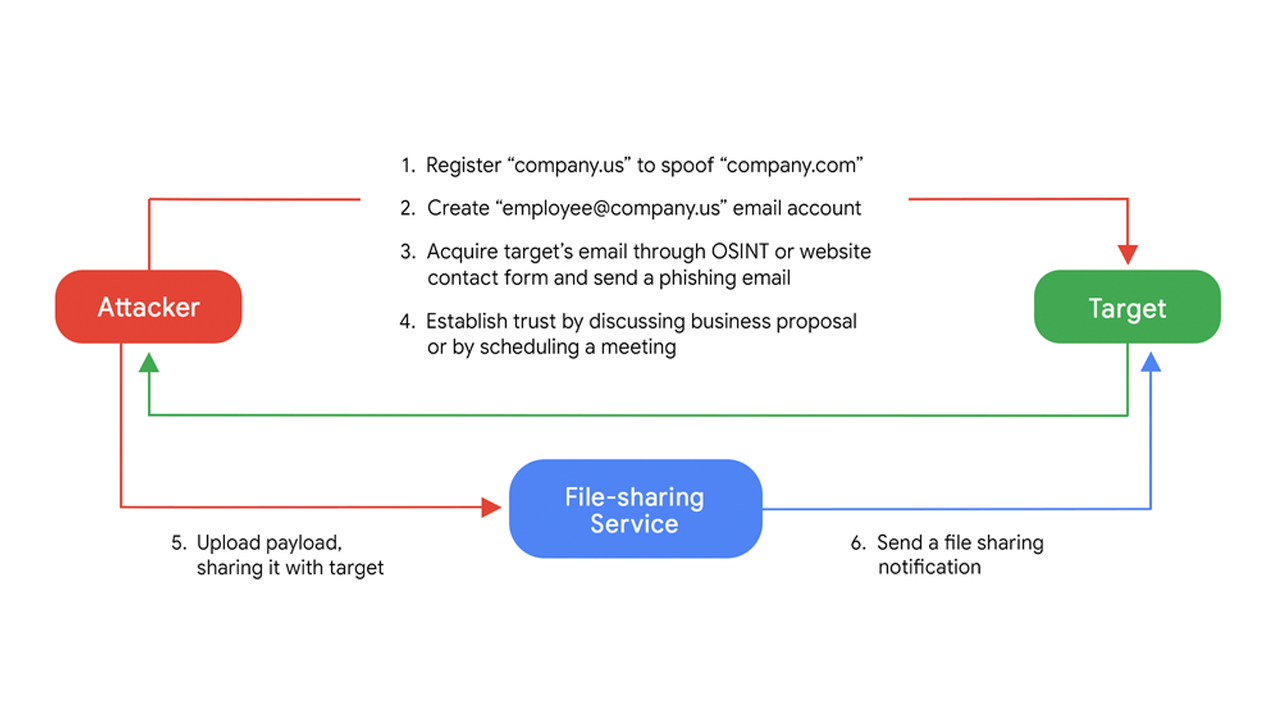
The IAB also handled additional communications with the victims in order to build trust sending a link to a malicious payload using legitimate file-sharing services.
The likes of WeTransfer, TransferNow, and OneDrive were used to deliver the payload that exploited the Microsoft zero-day, which was another technique the attackers used to evade detection mechanisms, TAG said.
EXOTIC LILY’s attack chain remained consistent throughout TAG’s analysis and can be broken down into just a few steps:
- Register [legitimate company name].us to imitate [legitimate company name].com
- Create “employee@[legitimate company name].us” email address
- Use OSINT or a website contact form to acquire target’s email address, send a phishing email
- Establish trust with further discussion or by scheduling a meeting
- Share payload with target
- Send a file-sharing notification
The group first used fake online profiles with AI-generated faces to impersonate employees at a spoofed company, but later resorted to stealing genuine employees’ data and harvesting more from databases like CrunchBase and RocketReach.
RELATED RESOURCE
How a platform approach to security monitoring initiatives adds value
Integration, orchestration, analytics, automation, and the need for speed
The use of a legitimate file-sharing service became a powerful method of avoiding detection, as not only are they familiar companies, but the target also receives a genuine file-sharing notification from that provider to increase the perceived authenticity.
EXOTIC LILY first used documents containing an exploit for a Microsoft zero-day but later changed strategy to delivering ISO files with hidden BazarLoader DLLs – a fileless attack method also common with ransomware groups.
Microsoft shortcut files, known as LNK shortcuts, were also delivered in these ISO files, with samples indicating they were custom-made by EXOTIC LILY rather than off-the-shelf exploit kits, TAG said.

Connor Jones has been at the forefront of global cyber security news coverage for the past few years, breaking developments on major stories such as LockBit’s ransomware attack on Royal Mail International, and many others. He has also made sporadic appearances on the ITPro Podcast discussing topics from home desk setups all the way to hacking systems using prosthetic limbs. He has a master’s degree in Magazine Journalism from the University of Sheffield, and has previously written for the likes of Red Bull Esports and UNILAD tech during his career that started in 2015.
-
 Everything you need to know about the GitHub Copilot pricing changes
Everything you need to know about the GitHub Copilot pricing changesNews GitHub Copilot pricing changes mean users will be charged based on consumption, rather than a set number of credits
-
 Integris makes first international move with Australian MSP acquisition
Integris makes first international move with Australian MSP acquisitionNews The provider’s first international acquisition will extend its reach across APAC.
-
 Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitation
Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitationNews A dip in ransomware volumes points to a more targeted approach focused on vulnerability exploitation
-
 Security leaders overconfident about ransomware recovery
Security leaders overconfident about ransomware recoveryNews Few manage to recover all their data, and many experience business disruption
-
 German authorities want your help finding the hackers behind GandCrab and REvil
German authorities want your help finding the hackers behind GandCrab and REvilNews Daniil Maksimovich Shchukin and Anatoly Sergeevitsch Kravchuk are believed to have made millions from ransomware as a service schemes
-
 The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in life
The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in lifeNews With family responsibilities and mortgages to pay, it's not teenagers dishing out malware or carrying out cyber extortion
-
 Organizations hit by 90 zero-day vulnerabilities last year
Organizations hit by 90 zero-day vulnerabilities last yearNews Google Threat Intelligence researchers warn that edge devices and security appliances are prime entry points
-
 Ransomware gangs are using employee monitoring software as a springboard for cyber attacks
Ransomware gangs are using employee monitoring software as a springboard for cyber attacksNews Two attempted attacks aimed to exploit Net Monitor for Employees Professional and SimpleHelp
-
 Ransomware gangs are sharing virtual machines to wage cyber attacks on the cheap – but it could be their undoing
Ransomware gangs are sharing virtual machines to wage cyber attacks on the cheap – but it could be their undoingNews Thousands of attacker servers all had the same autogenerated Windows hostnames, according to Sophos
-
 Google issues warning over ShinyHunters-branded vishing campaigns
Google issues warning over ShinyHunters-branded vishing campaignsNews Related groups are stealing data through voice phishing and fake credential harvesting websites