Microsoft just took down notorious cyber crime marketplace RedVDS – and found hackers were using ChatGPT and its own Copilot tool to wage attacks
Authorities across Europe, the UK, and US worked with Microsoft to take down RedVDS infrastructure


Notorious cyber crime marketplace RedVDS is no more after a Microsoft strike knocked the Cybercrime as a Service community offline.
While the name of the site may not be familiar, its impact has been felt widely across the globe in recent years. Microsoft said activity linked to RedVDS infrastructure had compromised more than 191,000 organizations globally since September, enabling $40 million in fraud in the US alone since March 2025.
RedVDS was an online subscription service that let hackers launch attacks using virtual computers – often running unlicensed versions of Windows.
Steven Masada, assistant general counsel for Microsoft’s Digital Crimes Unit, said the online community made fraud “cheap, scalable, and difficult to trace”.
Make Password Security Your New Year's Resolution
Get 50% off Keeper Personal and Family plans, and 30% off Keeper Business Starter today!
"Services like these have quietly become a driving force behind today’s surge in cyber‑enabled crime, powering attacks that harm individuals, businesses, and communities worldwide,” Masada said in a blog post confirming the takedown.
What was RedVDS?
RedVDS started operations in 2019, offering hackers low-cost virtual services on a marketplace via a subscription service, with prices as low as $40 dollars in some instances.
"RedVDS is an infrastructure service that facilitated malicious activity, but unlike malware, it did not perform harmful actions itself; the threat came from how criminals used the servers after provisioning," Microsoft said.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
Criminals used tools available via RedVDS for spam and phishing emails to route traffic to evade detection or access criminal forums, and to run scripting or automation tools.
"In these schemes, attackers gain unauthorized access to email accounts, quietly monitor ongoing conversations, and wait for the right moment, such as an upcoming payment or wire transfer," Masada explained.
"At that point, they impersonate a trusted party and redirect funds, often moving the money within seconds."
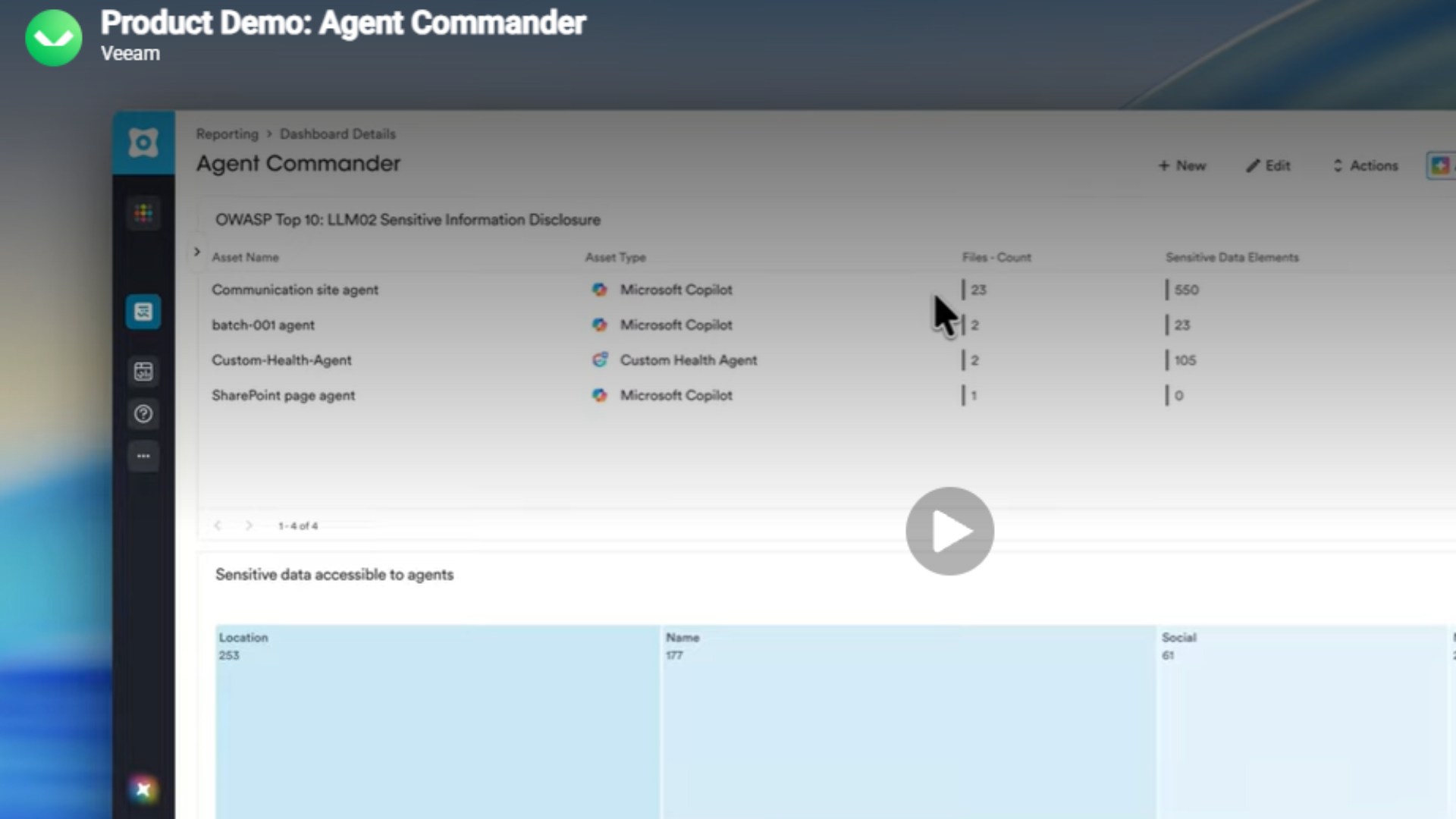
Microsoft said it spotted plenty of legitimate tools being used on RedVDS hosts by criminals to build their malicious campaigns, including VPNs, remote admin tool AnyDesk, and AI tools such as ChatGPT and even its own Copilot.
"RedVDS is frequently paired with generative AI tools that help identify high‑value targets faster and generate more realistic, multimedia message email threads that mimic legitimate correspondences," Masada said.
"In hundreds of cases, Microsoft observed attackers further augment their deception by leveraging face-swapping, video manipulation, and voice cloning AI tools to impersonate individuals and deceive victims."
RedVDS victims consider legal action
A host of major companies worldwide have been impacted by RedVDS in its seven-year history. Victims include H2-Pharma, an American pharmaceutical company that lost $7.3m.
Meanwhile, the Gatehouse Dock Condominium Association in Florida lost $500,000 in a scam. Both are plaintiffs in the civil action against RedVDS, Microsoft noted.
The takedown is the result of a far-reaching operation which saw coordinated legal action in the US and UK. The tech giant said it worked closely with law enforcement agencies such as Europol in the effort.
Microsoft and its partners have taken over "key malicious infrastructure", including two domains that host the marketplace.
How Microsoft cracked the case
RedVDS operated similarly to various other Cybercrime as a Service schemes. According to Microsoft, the site offered unlicensed Windows-based Remote Desktop Protocol (RDP) servers with full administrator control and no usage limits.
Hackers behind the service boasted that its system could set up a fresh host within minutes — offering scalability to its clients.
Notably, the scheme was blown open after Microsoft investigators found a “single, cloned Windows host image” that was being reused across the service. This, researchers explained, left “unique technical fingerprints that defenders could leverage for detection."
Microsoft noted that RedVDS provided virtual Windows cloud servers, but all were generated from a single Windows Server 2022 image via RDP – another mistake that gave researchers vital clues.
"All RedVDS instances identified by Microsoft used the same computer name, WIN-BUNS25TD77J, an anomaly that stood out because legitimate cloud providers randomize hostnames," Microsoft added.
RedVDS didn't own any data centers for its operations, instead renting servers from five hosting companies in the US, Canada, UK, France and Netherlands. That allowed RedVDS to offer services in different regions, helping to evade security filters, and more easily blend attacks with normal data centre traffic, Microsoft noted.
Microsoft said efforts were underway to identify the individuals who ran the site, but said it tracks the threat actor as Storm-2470.
How can enterprises protect themselves?
What can businesses do to avoid being subject to such attacks? Microsoft noted that most of RedVDS-related attacks involved social engineering, phishing operations, and business email compromise (BEC).
To defend against phishing and BEC attacks, Microsoft said to focus on primary gateways such as email and authentication by hardening credentials and cloud identities, and to invest in user awareness training such as phishing simulations.
"Simple steps can significantly reduce risk, including slowing down and questioning urgency, calling points of contact back using numbers that are already known to you, verifying payment requests using additional contact information, enabling multifactor authentication, watching carefully for subtle changes in email addresses, keeping software up to date, and reporting suspicious activity to law enforcement," Masada added.
FOLLOW US ON SOCIAL MEDIA
Make sure to follow ITPro on Google News to keep tabs on all our latest news, analysis, and reviews.
You can also follow ITPro on LinkedIn, X, Facebook, and BlueSky.
Freelance journalist Nicole Kobie first started writing for ITPro in 2007, with bylines in New Scientist, Wired, PC Pro and many more.
Nicole the author of a book about the history of technology, The Long History of the Future.
-
 Hackers are turning up at law firms to gain physical access to machines
Hackers are turning up at law firms to gain physical access to machinesNews The FBI is warning companies to look out for fake IT staff
-
 Beware of emails threatening a code of conduct review
Beware of emails threatening a code of conduct reviewNews A widespread phishing campaign has targeted tens of thousands of employees
-
 Tycoon 2FA is down, but not out – researchers warn the phishing as a service operation is still a huge threat to businesses
Tycoon 2FA is down, but not out – researchers warn the phishing as a service operation is still a huge threat to businessesNews Millions of Tycoon 2FA attacks are still hitting businesses, according to research from Barracuda
-
 German authorities want your help finding the hackers behind GandCrab and REvil
German authorities want your help finding the hackers behind GandCrab and REvilNews Daniil Maksimovich Shchukin and Anatoly Sergeevitsch Kravchuk are believed to have made millions from ransomware as a service schemes
-
 Interpol teams up with tech firms to seize 45,000 malicious IPs, servers in global cyber crime crackdown
Interpol teams up with tech firms to seize 45,000 malicious IPs, servers in global cyber crime crackdownNews Operation Synergia III saw 94 arrests - and counting - with malicious IP addresses used in phishing and fraud schemes seized
-
 The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in life
The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in lifeNews With family responsibilities and mortgages to pay, it's not teenagers dishing out malware or carrying out cyber extortion
-
 Is your new hire an AI clone? Microsoft says North Korean hackers are using AI to impersonate job seekers and steal company secrets
Is your new hire an AI clone? Microsoft says North Korean hackers are using AI to impersonate job seekers and steal company secretsNews The groups are increasingly using face-changing or voice-changing software to make their fake identities more plausible
-
 Cloudflare warns state-backed hackers are ‘weaponizing legitimate enterprise ecosystems’ as ‘living off the land’ attacks surge
Cloudflare warns state-backed hackers are ‘weaponizing legitimate enterprise ecosystems’ as ‘living off the land’ attacks surgeNews Chinese, North Korean, and Russian-backed threat groups now favor longer-term compromises over brute force attacks