A month in the life of a social engineer – part one
With hackers finding more ingenious ways to exploit human flaws, we get inside the planning stages of a social engineering attack


Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
You are now subscribed
Your newsletter sign-up was successful
With social engineering set to plague 2022, understanding cyber criminals’ tactics, and the mistakes they make, might help us defend against their efforts. This is the first entry in a four-part series, published weekly, exploring how social engineers plan their attacks – from identifying targets to exploitation.
Human beings are hard-wired to trust, help, connect and impress. It's what makes us so valuable to your organisation. These traits, unfortunately, also make humans your fatal flaw.
Social engineering is the art of tricking people into doing something that's in your interests and not in your victims’, with a view to gathering information or achieving an action, such as letting you into their house. It's a criminal tactic as old as time, and a perfect fit for today's networked workplace.
Cyber criminals have utilised social engineering effectively through the years, turning the best employees into unwitting accomplices in security breaches. The consequence, warn experts, has been a surge in active threats to critical and sensitive systems.
Know thy enemy
"There's a tidal wave of it coming," former cyber criminal and We Fight Fraud founder, Tony Sales, tells IT Pro. "National infrastructure is at risk because of social engineering. I think the whole country is at risk without even realising it."
Figures bear out this alarming language, with Verizon finding 85% of data breaches involve attempts to prey on human weaknesses. Purplesec claims, meanwhile, 98% of attacks rely on some form of social engineering.

Tony Sales is a former fraudster and founder of We Fight Fraud
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
It's easy to see why cyber criminals find social engineering so effective; it takes much less effort and ingenuity to con an individual into giving you access to company computers than hacking through corporate code. The poor weaponised employee has no idea what's going on.
If you're to stand any chance of avoiding this threat, you must know your enemy and recognise their tactics. "Unless you teach your staff about the human element, you are going to become a victim," says Sales, whose 30-year criminal career included identity fraud and two stints in prison. "If you do train them, though, you'll force the attackers to look elsewhere, at your less secure competitors." You must try, therefore, to get inside a social engineer’s heads before they can get inside yours.
The attack plan
Social engineering is, by its nature, a stealthy, hard-to-spot, compromising tactic that plays a role in most multi-stage attacks that demand long-term infiltration and observation. Usually, the attacker will use a combination of steps to achieve their aims. These can be as simple as tricking someone into revealing their system password (not difficult, given how many of us still use our pets' names and football teams as passwords), or as sophisticated as securing a job with a particular organisation in order to infiltrate its global security networks. Edward Snowden, in a way, did both.
Long before an ambitious social engineer can get stuck into spoofing finance staff with AI deepfakes pretending to be the CFO, however, they must decide how their action fits into the attack plan. They must also determine which employee to target, how to gain their trust, and to what ends: To steal money? Seize data and intellectual property (IP), which can then be sold on the black market or used in further attacks? Or are they hoping to exploit a flaw and infiltrate the organisation's network, then set off a row of domino compromises in a supply-chain attack?
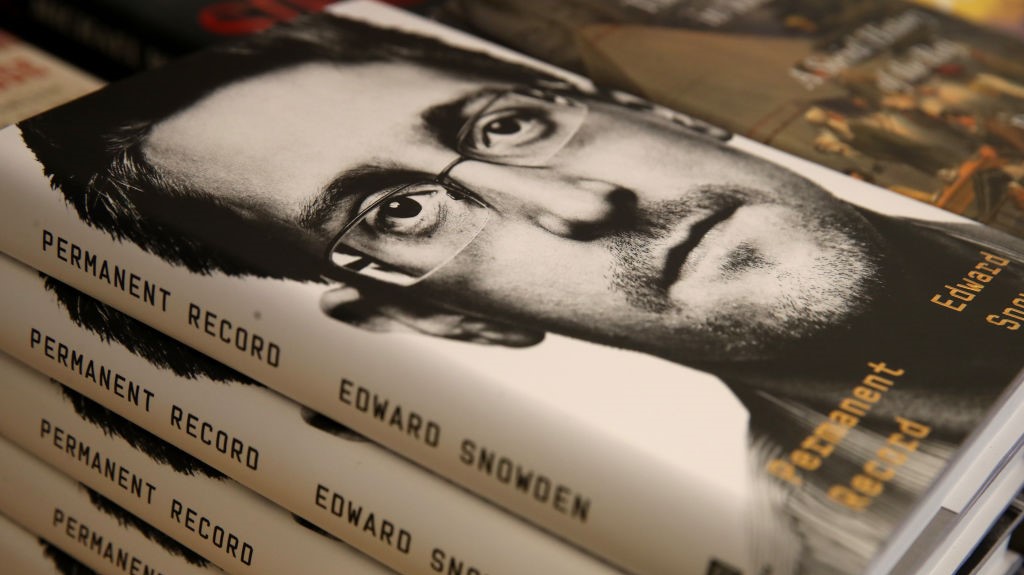
Edward Snowden was at the heart of a sensational whistleblowing scandal early last decade
"Sophisticated attackers have a very clear understanding of how they’ll profit from their activities, just like a successful business," says James Stanger, chief technology evangelist at IT education group CompTIA. "If they want to steal passwords, for instance, they'll decide exactly how they will monetise those passwords to increase their profit at the lowest possible risk."
Cover your tracks
The nature of social engineering helps threat actors stay hidden or disguised, right up to the final breach, and even after the wider effects are noticed. The technique's heavy reliance on research, however, risks leaving a large online footprint, so this has to be addressed in the attack plan.
"They'd probably use Tor and a VPN to be as obfuscated as possible," says Kevin Curran, senior IEEE member and professor of cyber security at Ulster University. "It takes incredible concentration to be successful, there's a lot of effort involved in staying under the radar."
To reduce the effort, the social engineer may hire accomplices with complementary skillsets. Sales, for example, teamed up with hacker Solomon Gilbert. "Sol was probably one of the best hackers on the planet," says Sales. "My criminal mind works out a plan, and Solomon attaches what he needs to it, and then you get the 'boom'. We were ten times deadlier together than we'd ever have been individually."
RELATED RESOURCE

An experienced social engineer, though, will exploit human flaws from the word go, and hire accomplices who have no idea what they're getting into. This reduces any risk for the criminal by limiting the number of people with knowledge of the conspiracy. "You could probably end up being a translator for a criminal gang and not know it," SE Labs founder Simon Edwards tells IT Pro. "If I was going to convince you to do something for me, I would pretend to be Apple, so you'd believe you were working for Apple to help them edit their messaging – and you wouldn't know any different."
In the next part of our series, we reveal how a social engineer smokes out the weakest links in an organisation and turns these people into attack vectors.
Jane Hoskyn has been a journalist for over 25 years, with bylines in Men's Health, the Mail on Sunday, BBC Radio and more. In between freelancing, her roles have included features editor for Computeractive and technology editor for Broadcast, and she was named IPC Media Commissioning Editor of the Year for her work at Web User. Today, she specialises in writing features about user experience (UX), security and accessibility in B2B and consumer tech. You can follow Jane's personal Twitter account at @janeskyn.
-
 Surging memory costs are scuppering digital transformation projects
Surging memory costs are scuppering digital transformation projectsNews Most organizations are already affected by memory cost increases, with no light at the end of the tunnel any time soon
-
 Brother UK taps Mike Brown to spearhead channel growth
Brother UK taps Mike Brown to spearhead channel growthNews The seasoned channel specialist will focus on expanding the vendor’s partner network and driving reseller revenue opportunities
-
 Microsoft and NCSC issue alerts over hacker campaigns targeting WhatsApp, Signal messaging apps
Microsoft and NCSC issue alerts over hacker campaigns targeting WhatsApp, Signal messaging appsNews Microsoft warns about a sophisticated attack that starts with WhatsApp messages, while the NCSC says such incidents are on the rise
-
 Is your new hire an AI clone? Microsoft says North Korean hackers are using AI to impersonate job seekers and steal company secrets
Is your new hire an AI clone? Microsoft says North Korean hackers are using AI to impersonate job seekers and steal company secretsNews The groups are increasingly using face-changing or voice-changing software to make their fake identities more plausible
-
 Google issues warning over ShinyHunters-branded vishing campaigns
Google issues warning over ShinyHunters-branded vishing campaignsNews Related groups are stealing data through voice phishing and fake credential harvesting websites
-
 Thousands of Microsoft Teams users are being targeted in a new phishing campaign
Thousands of Microsoft Teams users are being targeted in a new phishing campaignNews Microsoft Teams users should be on the alert, according to researchers at Check Point
-
 Microsoft warns of rising AitM phishing attacks on energy sector
Microsoft warns of rising AitM phishing attacks on energy sectorNews The campaign abused SharePoint file sharing services to deliver phishing payloads and altered inbox rules to maintain persistence
-
 Warning issued as surge in OAuth device code phishing leads to M365 account takeovers
Warning issued as surge in OAuth device code phishing leads to M365 account takeoversNews Successful attacks enable full M365 account access, opening the door to data theft, lateral movement, and persistent compromise
-
 Amazon CSO Stephen Schmidt says the company has rejected more than 1,800 fake North Korean job applicants in 18 months – but one managed to slip through the net
Amazon CSO Stephen Schmidt says the company has rejected more than 1,800 fake North Korean job applicants in 18 months – but one managed to slip through the netNews Analysis from Amazon highlights the growing scale of North Korean-backed "fake IT worker" campaigns
-
 Complacent Gen Z and Millennial workers are more likely to be duped by social engineering attacks
Complacent Gen Z and Millennial workers are more likely to be duped by social engineering attacksNews Overconfidence and a lack of security training are putting organizations at risk
