Software vulnerabilities are declining, but third-party risks still linger
More robust security practices are helping to reduce the total number of software vulnerabilities


Software vulnerabilities are on the decline according to new research from Synopsys.
Analysis from the firm’s security testing service shows that, from 2020 to 2022, there has been a significant decrease in software vulnerabilities.
Overall, 97% of tests on target applications identified serious vulnerabilities in 2020, according to Synopys. However, this decreased to 95% in 2021 and dropped again to 83% in 2022.
The software company sees this as a cause for optimism concerning organizations’ ability to produce error-free code with improved DevSecOps procedures.
This improvement could be down to the wider adoption of practices such as automated testing and code reviews, which are proving effective at reducing exploit opportunities for hackers.
Synopsys’ testing replicates attack vectors used by threat actors today that include penetration testing, dynamic security testing (DAST), mobile application security testing (MAST), and network security testing.
Overall, across the three year period from 2020 to 2022, 92% of tests found some form of vulnerability, yet only 27% were considered high-severity, and only 6.2% contained critical-severity vulnerabilities.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
Severity levels indicate the risk a vulnerability poses to network security as rated on the CVSS v3 scale.
Jason Schmitt, general manager of the Synopsys Software Integrity Group, said this decrease is an encouraging sign that businesses are adopting more robust measures to address an increasingly sophisticated threat landscape.
"For the first time in years, we’re seeing a decrease in the number of known vulnerabilities in software, which provides new hope that organizations are taking security seriously and prioritizing a strategic and holistic approach to software security in order to make a lasting impact”.
Third-party software still poses increased risk
Despite evidence showing certain procedures are paying dividends, the report does identify areas that still pose an increased risk to organizations.
In 2022, one-in-four tests found vulnerable third-party libraries to be a particular risk to application security.
Although useful for developers trying to build software more efficiently, Synopsys’ report notes security risks associated with open source code have been on the rise.
Synopsys’ 2023 report on open source security revealed high-risk vulnerabilities in open source code have increased by 557% in retail and eCommerce alone. This is compounded by a concerning lack of security patching with 91% of the codebases audited containing outdated open source components.
Leaked information has also remained a leading security risk throughout this period. On average, 19% of the total vulnerabilities were directly related to information leakage issues.
RELATED RESOURCES
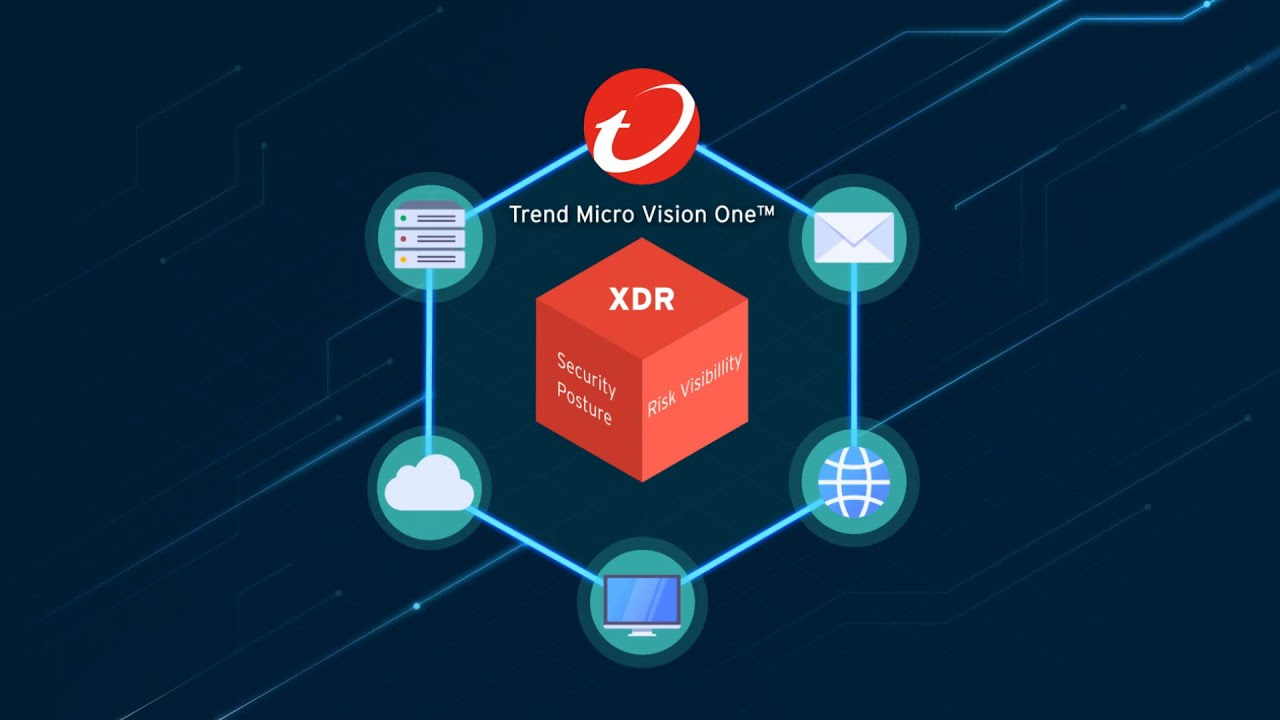
Analyzing the economic benefits of Trend Micro Vision One
Discover a security platform that will increase the effectiveness of your security analysts
Finally, the findings indicate cross-site scripting (XSS) also appears to be on the rise, with 19% of all vulnerabilities uncovered in 2022 being susceptible to cross-site scripting.
Andy Schneider, field CISO at Lacework, warned that the decreases in vulnerabilities observed year-to-year during this period may not be an accurate reflection of the long term security posture of organizations.
“From a short term perspective, there might be ups and downs in the amount of vulnerabilities,” he told ITPro.
“However, much like having a warm or cold summer doesn’t say anything about climate change, this doesn’t necessarily represent the whole picture. More and more organizations are transforming their business to a digital model that usually implies new lines of code and potentially new vulnerabilities.”
RELATED RESOURCES

Patch information security vulnerabilities
DOWNLOAD NOW
Michael Man, DevSecOps Evangelist at software security firm Veracode said its own research also revealed a "general downward trend in the number of flaws introduced over the years".
"It is safe to say that teams are getting better," he said.
"What leaves room for improvement is how thoroughly and quickly teams remediate, but curiously this varies by language."
Man added that a concerning trend observed by Veracode is that some organizations tend to become more lax over time as applications age and expand in scope.
"The attention in terms of writing secure code tends to fade for whatever reason, and as applications age and grow in size, a higher proportion of them are introducing new flaws than in the first 2 years. Flaws tend to accumulate year over year until 70% are carrying flaws.
"So, while we are getting better at new flaw introduction over the years, the attention to detail over the application lifecycle would be an area where teams could make some material improvements.”

Solomon Klappholz is a former staff writer for ITPro and ChannelPro. He has experience writing about the technologies that facilitate industrial manufacturing, which led to him developing a particular interest in cybersecurity, IT regulation, industrial infrastructure applications, and machine learning.
-
 Enterprises flock to AI PCs amid sharpened workforce productivity focus
Enterprises flock to AI PCs amid sharpened workforce productivity focusNews Leaders are adopting AI PCs to stay competitive and improve employee productivity
-
 Google Cloud is more confident than ever in its AI strength, from hardware to software
Google Cloud is more confident than ever in its AI strength, from hardware to softwareOpinion With a commitment to interoperability and open data connections, Google Cloud is daring its customers to find a more comprehensive AI suite on the market