Over two-thirds of companies still run software with WannaCry flaw
Four years have passed, and many systems still need patching

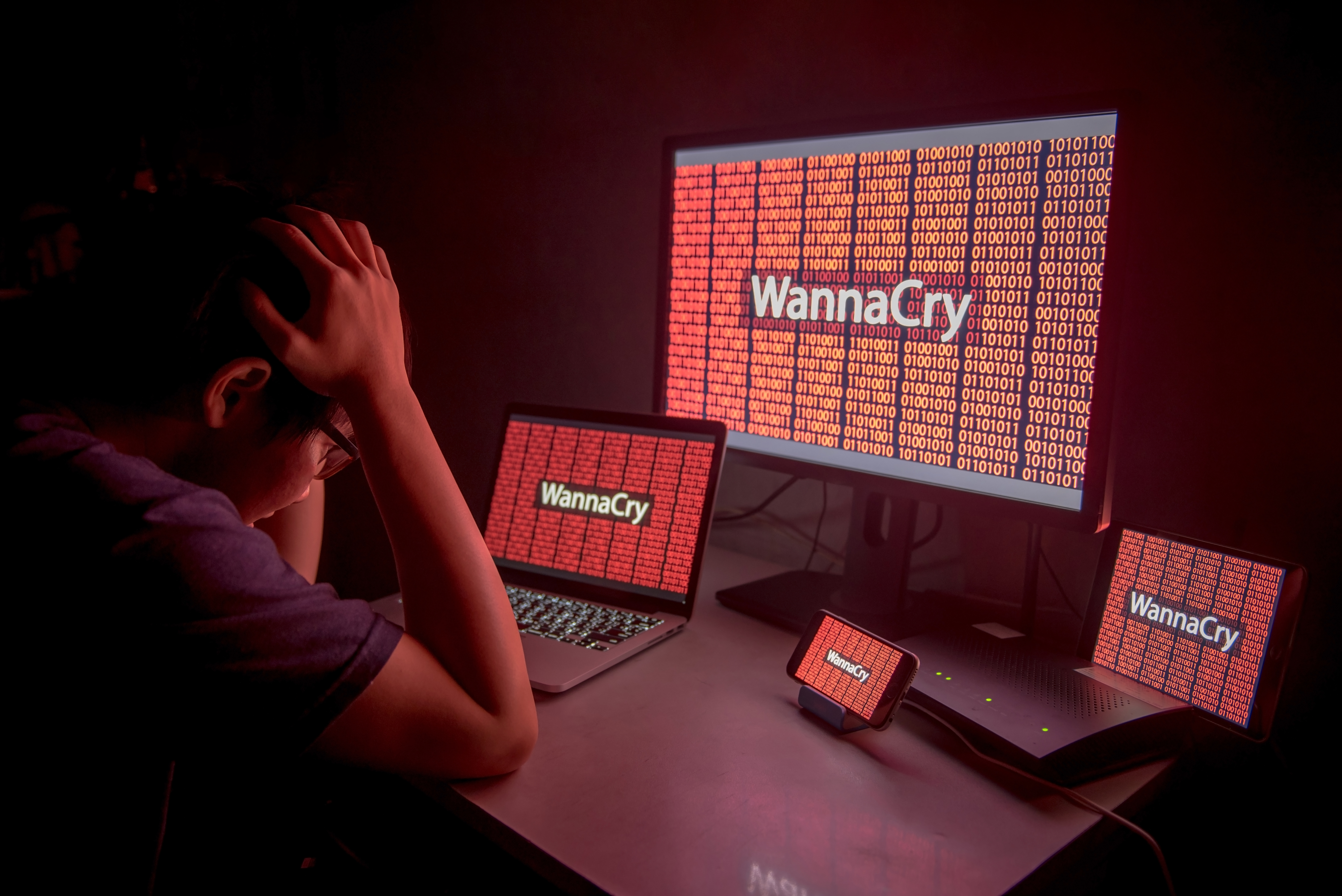
Four years after the global WannaCry and NotPetya ransomware attacks, two-thirds of companies still haven't patched the vulnerabilities that caused them, according to cloud network detection and response company ExtraHop.
The company investigated data from its Reveal(x) security platform in the first quarter of 2021 to determine which protocols its customers were running. It found that 88% of them were still running at least one device using SMBv1, which was a pivotal attack vector for the EternalBlue exploit used in the two ransomware attacks.
Although a single device could mean a company is maintaining it just for use by an attack team, a more worrying statistic was that 67% of companies are running over 10 SMBv1-enabled devices. Over two-thirds (37%) were running more than 50, and 31% of companies checked had over 100 SMBv1 devices on their networks.
The report also highlighted heavy use of two other protocols in Windows servers. The first, called Local Loop Multicast Name Resolution (LLMNR), is an alternative to DNS for resolving basic names within a private network. It has a similar problem to Windows' old NetBIOS naming service, in that it communicates with all clients on the network rather than a specific server.
That enables an attacker to listen for and reply to access requests, creating a race condition to harvest the client's hashed credentials if it establishes a conversation quickly enough. It can then decrypt those credentials, giving an attacker access to a client's network account, or use them in a pass-the-hash attack.
The other protocol, New Technology LAN Manager (NTLM) v1, is a decades-old network authentication mechanism that has long been obsolete. Nevertheless, over a third (34%) of companies have over 10 devices using it, ExtraHop said. Almost one in five (19%) had over 100 devices using the protocol, despite Microsoft advising people to stop using it altogether in favor of the more secure Kerberos system.
The report also found that few companies had embraced using TLS encryption over HTTP (HTTPS), which browser vendors have aggressively enforced. It found that 81% of enterprise environments were still using HTTP to send access credentials in plain text.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
ExtraHop said it analyzed over four petabytes of traffic each day in its investigation of online protocol usage.
Danny Bradbury has been a print journalist specialising in technology since 1989 and a freelance writer since 1994. He has written for national publications on both sides of the Atlantic and has won awards for his investigative cybersecurity journalism work and his arts and culture writing.
Danny writes about many different technology issues for audiences ranging from consumers through to software developers and CIOs. He also ghostwrites articles for many C-suite business executives in the technology sector and has worked as a presenter for multiple webinars and podcasts.
-
 Developers warned to avoid 'early-access' Google Gemini tools
Developers warned to avoid 'early-access' Google Gemini toolsNews Attackers are tempting would-be users into downloading reverse shell malware
-
 Researchers warn millions of RDP and VNC servers are wide open to exploitation
Researchers warn millions of RDP and VNC servers are wide open to exploitationNews Researchers at Forescout spotted millions of RDP and VNC servers exposed online
-
 Researchers warn millions of RDP and VNC servers are wide open to exploitation
Researchers warn millions of RDP and VNC servers are wide open to exploitationNews Researchers at Forescout spotted millions of RDP and VNC servers exposed online
-
 Brace yourselves for a vulnerability explosion, Forescout warns
Brace yourselves for a vulnerability explosion, Forescout warnsNews AI advances are helping identify software flaws at record pace and scale, but that's not the good news some would think
-
 Ubuntu vulnerability exposes enterprises to root escalation, complete system compromise
Ubuntu vulnerability exposes enterprises to root escalation, complete system compromiseNews The high-severity Ubuntu vulnerability allows an unprivileged local attacker to escalate privileges through the interaction of two standard system components
-
 Security agencies issue warning over critical Cisco Catalyst SD-WAN vulnerability
Security agencies issue warning over critical Cisco Catalyst SD-WAN vulnerabilityNews Threat actors have been exploiting the vulnerability to achieve root access since 2023
-
 Millions of developers could be impacted by flaws in Visual Studio Code extensions – here's what you need to know and how to protect yourself
Millions of developers could be impacted by flaws in Visual Studio Code extensions – here's what you need to know and how to protect yourselfNews The VS Code vulnerabilities highlight broader IDE security risks, said OX Security
-
 CVEs are set to top 50,000 this year, marking a record high – here’s how CISOs and security teams can prepare for a looming onslaught
CVEs are set to top 50,000 this year, marking a record high – here’s how CISOs and security teams can prepare for a looming onslaughtNews While the CVE figures might be daunting, they won't all be relevant to your organization
-
 Microsoft patches six zero-days targeting Windows, Word, and more – here’s what you need to know
Microsoft patches six zero-days targeting Windows, Word, and more – here’s what you need to knowNews Patch Tuesday update targets large number of vulnerabilities already being used by attackers
-
 Experts welcome EU-led alternative to MITRE's vulnerability tracking scheme
Experts welcome EU-led alternative to MITRE's vulnerability tracking schemeNews The EU-led framework will reduce reliance on US-based MITRE vulnerability reporting database
