Dell SonicWALL NSA 2600 review
Offering a big boost in security features and performance, Dell SonicWALL NAS 2600 remains affordable for SMBs.

The NSA 2600 is miles than its predecessor and packs more into its 1U chassis. Some features cost extra but this appliance is easy to install and its zone based security makes light work of policy deployment.
-
+
Performance improvements; Easy installation; Extensive features; Zone based policies
-
-
Optional reporting and anti-spam

Replacing the elderly NSA 2400, Dell SonicWALL NSA 2600 delivers a near three-fold performance improvement. Along with a big hike in firewall throughput from 775Mbps to 1.9Gbps, it also doubles full DPI (deep packet inspection) speeds to 300Mbps.
This has been achieved by replacing the 500MHz dual-core MIPS CPU of the NSA 2400 with an 800MHz quad-core MIPS64 Octeon chip and beefing up memory from a miserly 512MB to a healthy 2GB. The port count is increased as well with eight Gigabit data ports plus a dedicated Gigabit management port.
The NSA 2600 can be upgraded to 10GbE speeds using the front expansion slot. A good selection of modules is available and includes dual-port 10Gbase-SR and 10Gbase-LR fibre or dual 10Gbase-T copper.
Prices for the NSA 2600 are reasonable with SonicTek charging 1,468 ex VAT for the base unit. A 1-year TotalSecurity subscription activates gateway anti-virus and anti-spyware, IPS, application controls and URL filtering and pushes the price up to around 2,330 ex VAT.
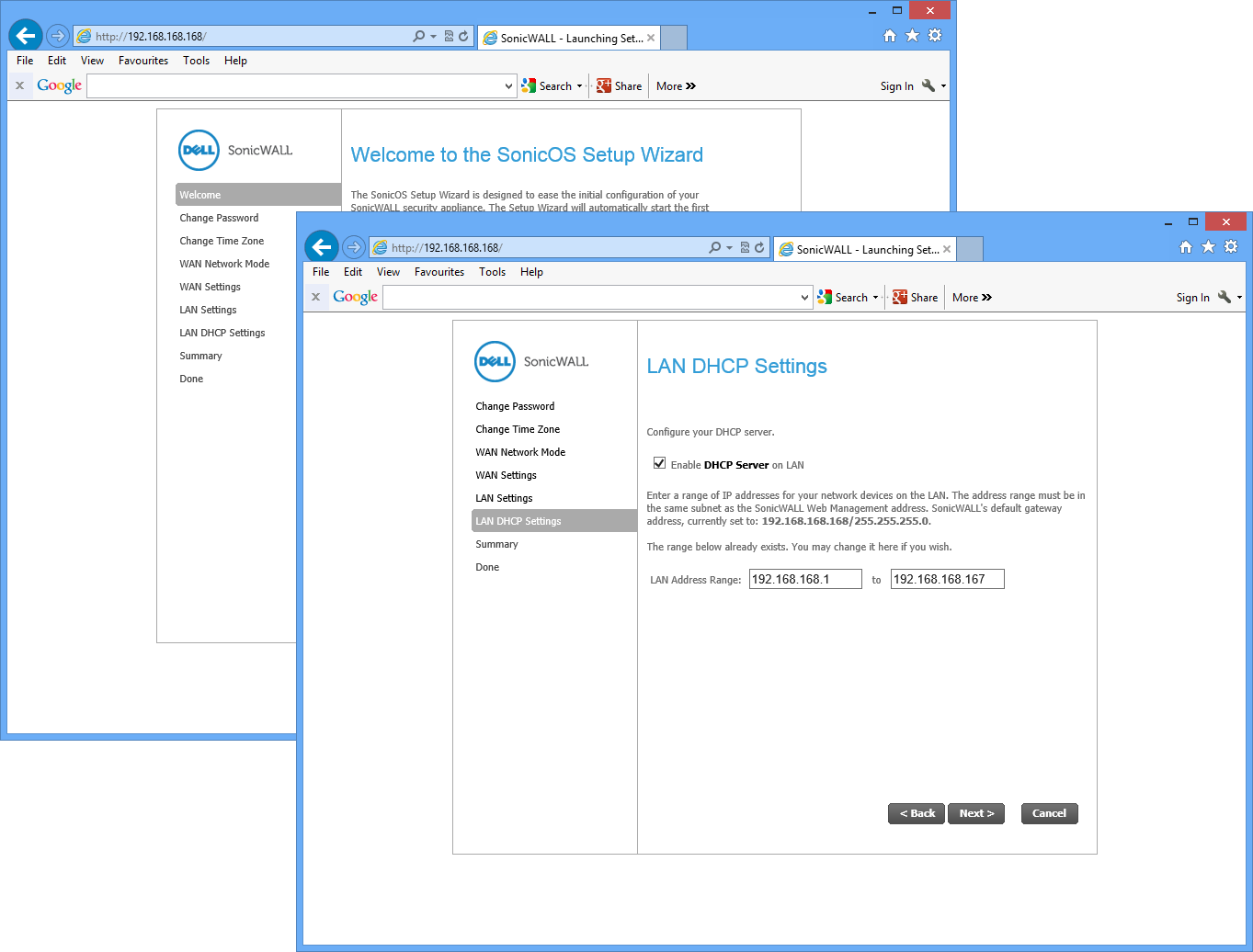
A quick start wizard gets the appliance up and running in a few minutes
Installation
We had no problems installing the NSA 2600 in the lab. The simple, browser-based quick start wizard secures administrative access, sets up the LAN and WAN ports and applies a security policy to the default port zone.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
Only the first LAN port is placed in a zone so you need to decide what to do with the others. You can group them into a single zone so new policies will be automatically applied to all connected systems or create separate zones for selected ports, each with their own security settings.
Selecting a security type for each zone also determines what traffic can pass across it. All LAN ports are trusted but the appliance's WAN port is untrusted so no traffic will be allowed to pass from it to another zone unless you create a rule permitting this.
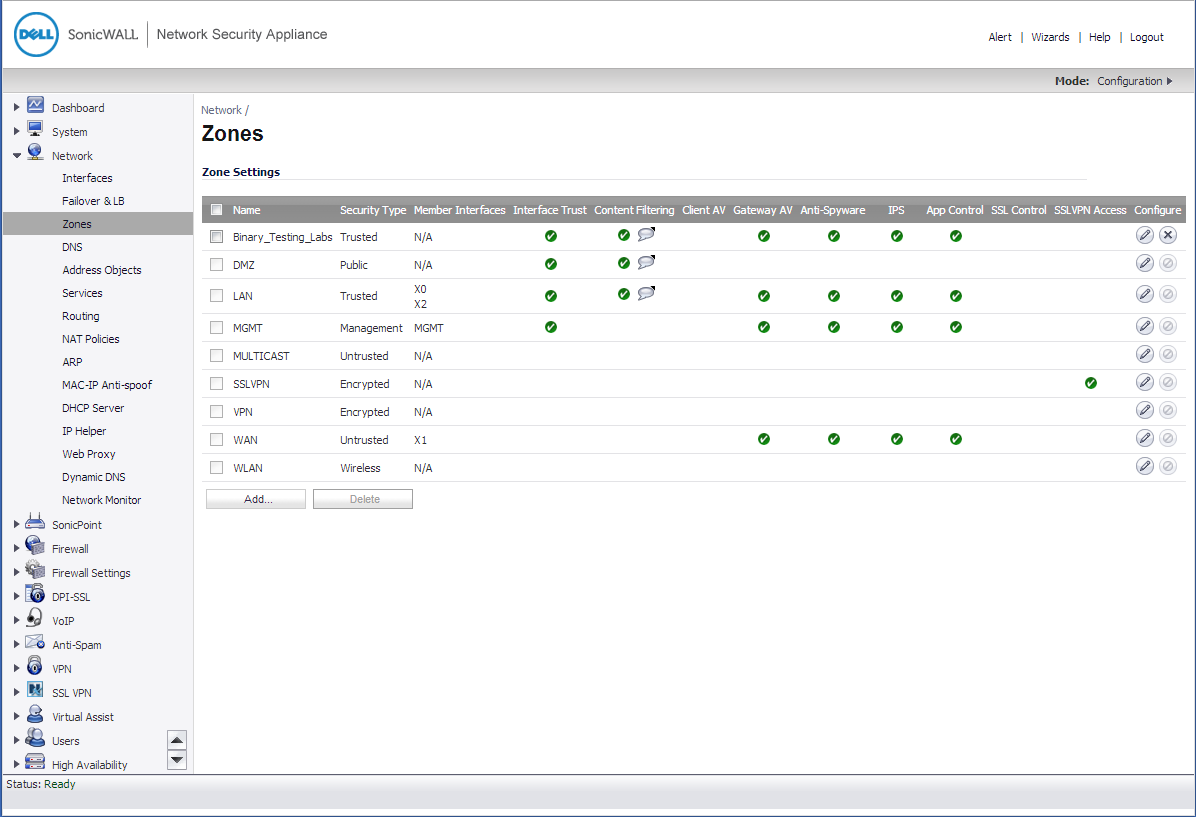
Security policies can be applied using the appliance's port zone feature
AV and web filtering
Anti-virus scanning is applied at the gateway and can be enabled on selected zones. It uses a single, global configuration where you can activate scanning on HTTP, FTP, IMAP, POP3, SMTP, CIFS and TCP streams.
Two options are provided for web content filtering as you can use the CFS (content filter service) included with the TotalSecure subscription or pay extra for the WebSense Enterprise hosted service. CFS will be adequate for most businesses as we found very few dodgy web sites slipped past it during testing.
It provides over 60 URL categories and you can create multiple filtering policies and apply them to different port zones. Each policy can be customised with black and white lists, you can use schedules to determine when they are active and apply AUPs by redirecting users to a consent web page. For even more browsing control you can activate the Geo-IP filter which blocks access to web sites hosted in specific countries.
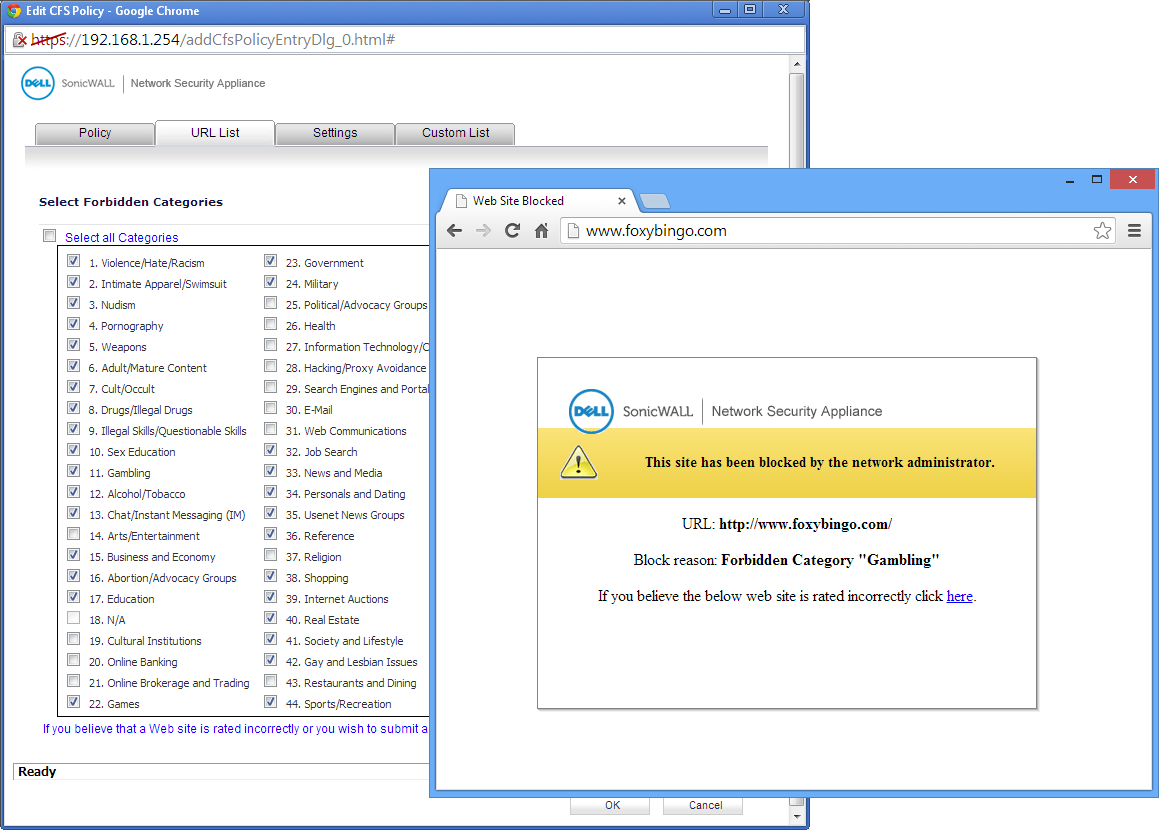
There are plenty of categories to choose from for URL filtering which performs well
Monitor your apps
The Application Control provides precise management of activities such as web browsing, file transfers and messaging. App Rules are complex but a wizard helps create inspection policies for SMTP, POP3, FTP and HTTP.
You can, for example, create an Application Firewall policy for FTP transfers. This inspects all uploads and downloads through a port zone looking for specific file types and blocks their transfer. Likewise with email, you can create a policy to inspect message subjects, content and attachments and decides whether to permit or deny the transfer.
For even greater control there are advanced app controls which use signature IDs to identify specific activities. These can spot a huge range including Facebook likes, pokes and posts, Exchange address book requests and much more and block or log them.
Rule creation can be streamlined by monitoring the App Flow graphs in the main dashboard. If you see any suspect activities or apps popping up you can create a rule to block, monitor or apply bandwidth restrictions.
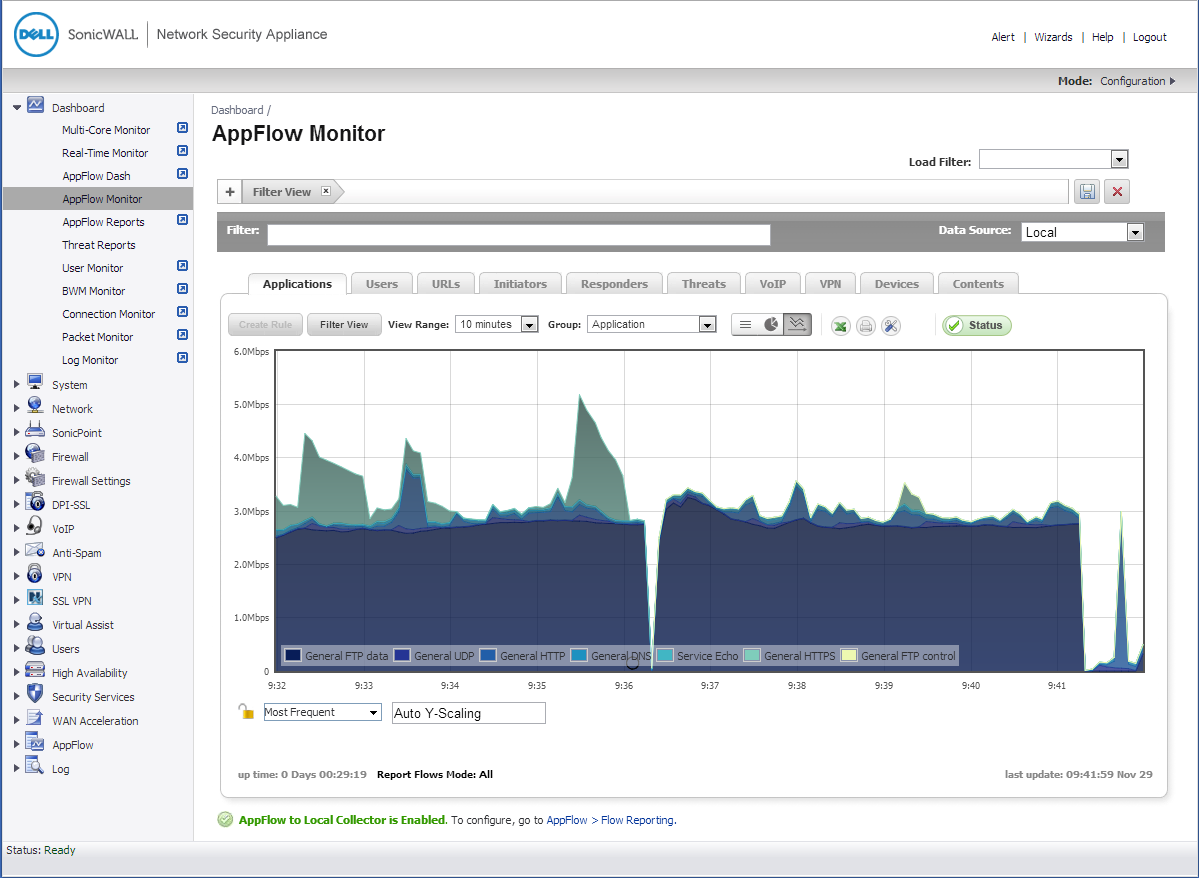
Real time graphs show user activity but the optional Analyzer report module costs extra
Anti-spam and reporting
The appliance comes with basic anti-spam measures using RBLs but we have never found these to be a substitute for the real thing as they let too much through. The Dell SonicWALL hosted anti-spam service is a better bet with a yearly subscription costing an additional 574 ex VAT.
This uses its own GRID network for applying sender IP reputation checks. It the message passes this test it's then subjected to further analyse in the cloud using a unique hash, or GRIDprint', generated using the message contents.
Although the Dashboard screen provides plenty of real time statistics, full reporting costs extra with the Analyzer adding around 220 ex VAT to the asking price. Running from a Windows or VMware host, this Syslog server takes all data from multiple appliances, stores it in a central database and provides an impressive range of report generation tools.
Conclusion
We had no problems installing the NSA 2600 with its zone feature making light work of security policy assignment. You'll need to factor in the extra costs of reporting and anti-spam but it's still reasonable value and offers a substantial speed boost over the NSA 2400.
Verdict
The NSA 2600 is miles than its predecessor and packs more into its 1U chassis. Some features cost extra but this appliance is easy to install and its zone based security makes light work of policy deployment.
Chassis: 1U rack
CPU: 800MHz quad-core MIPS64 Octeon
Memory: 2GB DDR3, 1GB Flash
Network: 8 x Gigabit
Other ports: Gigabit management, 2 x USB, RJ-45 console
Expansion: 1 x module slot, SDHC slot
Management: Web browser
Modules: 10Gbase-SR, £762; 10Gbase-LR, £1,350; 10Gbase-T, £291 (all ex VAT)
Dave is an IT consultant and freelance journalist specialising in hands-on reviews of computer networking products covering all market sectors from small businesses to enterprises. Founder of Binary Testing Ltd – the UK’s premier independent network testing laboratory - Dave has over 45 years of experience in the IT industry.
Dave has produced many thousands of in-depth business networking product reviews from his lab which have been reproduced globally. Writing for ITPro and its sister title, PC Pro, he covers all areas of business IT infrastructure, including servers, storage, network security, data protection, cloud, infrastructure and services.
-
 IBM wins biggest slice of $2bn US gov investment in domestic quantum firms
IBM wins biggest slice of $2bn US gov investment in domestic quantum firmsNews The Department of Commerce says it wants to strengthen the country's presence in this critical technology sector
By Emma Woollacott Published
-
 Data center industry faces ticking power time bomb
Data center industry faces ticking power time bombNews Technical and regulatory hurdles make colocation unscalable for most developers, Wood Mackenzie has warned
By Emma Woollacott Published
-
 Terzo taps former Accenture leader to drive channel expansion
Terzo taps former Accenture leader to drive channel expansionNews The financial and analytics specialist has named Daniel Haitz as head of strategic partnerships and channel growth
By Daniel Todd Published

