Ubuntu shifts to four-week update cycle
Critical fixes will also come every two weeks, mitigating the issues involved with releasing prompt patches on the old three-week cadence


Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
You are now subscribed
Your newsletter sign-up was successful
The Canonical Kernel Team is abandoning its update cadence in favor of a four-week cycle, and will add an additional update every two weeks for the most urgent fixes.
A move to a four-week cycle with a midpoint update will result in regular upstream stable updates, including security patches, bug fixes, and feature requests coming every four weeks. Critical fixes that can’t wait will arrive on a two-week cadence.
In the past, the Canonical team worked to a three-week kernel update cycle. This, according to Kleber Souza, Linux kernel engineering manager at Canonical, made for reasonable responsiveness but was “prone to interruptions from urgent CVEs, urgent customer requests and regressions found in -updates or during testing.”
The result was that the cycle tended to be extended, and delivering CVE fixes promptly was challenging.
Souza noted that OEM kernels would follow a more flexible schedule in terms of their deadlines for the acceptance of new patches.
Ubuntu is one of the most popular Linux distributions, and the changes will interest engineers charged with maintaining fleets of hardware running the operating system - on-premises or in the cloud - in light of the pace of vulnerability discovery and patching.
RELATED RESOURCE

Quantifying the public vulnerability market
Read how the reporting of vulnerabilities is contributing to greater, comprehensive security for all.
The move was described by one user on the company’s forums as “ambitious” and comes in the wake of a relatively easy-to-exploit privilege escalation vulnerability disclosed recently.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
The vulnerability in the OverlayFS module used in Ubuntu was documented in CVE-2023-2640 and CVE-2023-32629 and was exclusive to the operating system following changes made by the Canonical team in 2018.
CVE-2023-2640 permits an unprivileged user to set privileged extended attributes on mounted files. CVE-2023-32629 is a local privilege escalation vulnerability where permission checks are skipped.
Those changes only became an issue in 2020 when a security vulnerability patched in the Linux kernel did not make it into Ubuntu due to the earlier changes.
One report stated that the vulnerability could affect 40% of Ubuntu cloud workloads. Ubuntu fixed the vulnerabilities on 24 July 2023, and users were instructed to update their kernels.
With the revised cycle schedule, Souza said: “The Canonical Kernel Team is expecting to deliver more predictable updates with quicker turnaround for time-sensitive fixes”.

Richard Speed is an expert in databases, DevOps and IT regulations and governance. He was previously a Staff Writer for ITPro, CloudPro and ChannelPro, before going freelance. He first joined Future in 2023 having worked as a reporter for The Register. He has also attended numerous domestic and international events, including Microsoft's Build and Ignite conferences and both US and EU KubeCons.
Prior to joining The Register, he spent a number of years working in IT in the pharmaceutical and financial sectors.
-
 Cohere's Aleph Alpha merger could create a transatlantic sovereign AI powerhouse
Cohere's Aleph Alpha merger could create a transatlantic sovereign AI powerhouseAnalysis The merger between Cohere and Aleph Alpha aims to capitalize on the burgeoning sovereign AI market
-
 Everything you need to know about OpenAI's new workspace agents
Everything you need to know about OpenAI's new workspace agentsNews New ‘workspace agents’ from OpenAI will automate tasks for workers and can be customized for specific roles
-
 Windows 10 extended support costs could top $7 billion
Windows 10 extended support costs could top $7 billionNews Enterprises sticking with Windows 10 after the October deadline face huge costs
-
 Shifting left might improve software security, but developers are becoming overwhelmed – communication barriers, tool sprawl, and ‘vulnerability overload’ are causing serious headaches for development teams
Shifting left might improve software security, but developers are becoming overwhelmed – communication barriers, tool sprawl, and ‘vulnerability overload’ are causing serious headaches for development teamsNews Developers are becoming overwhelmed amid the 'shift left' in development practices, new research shows.
-
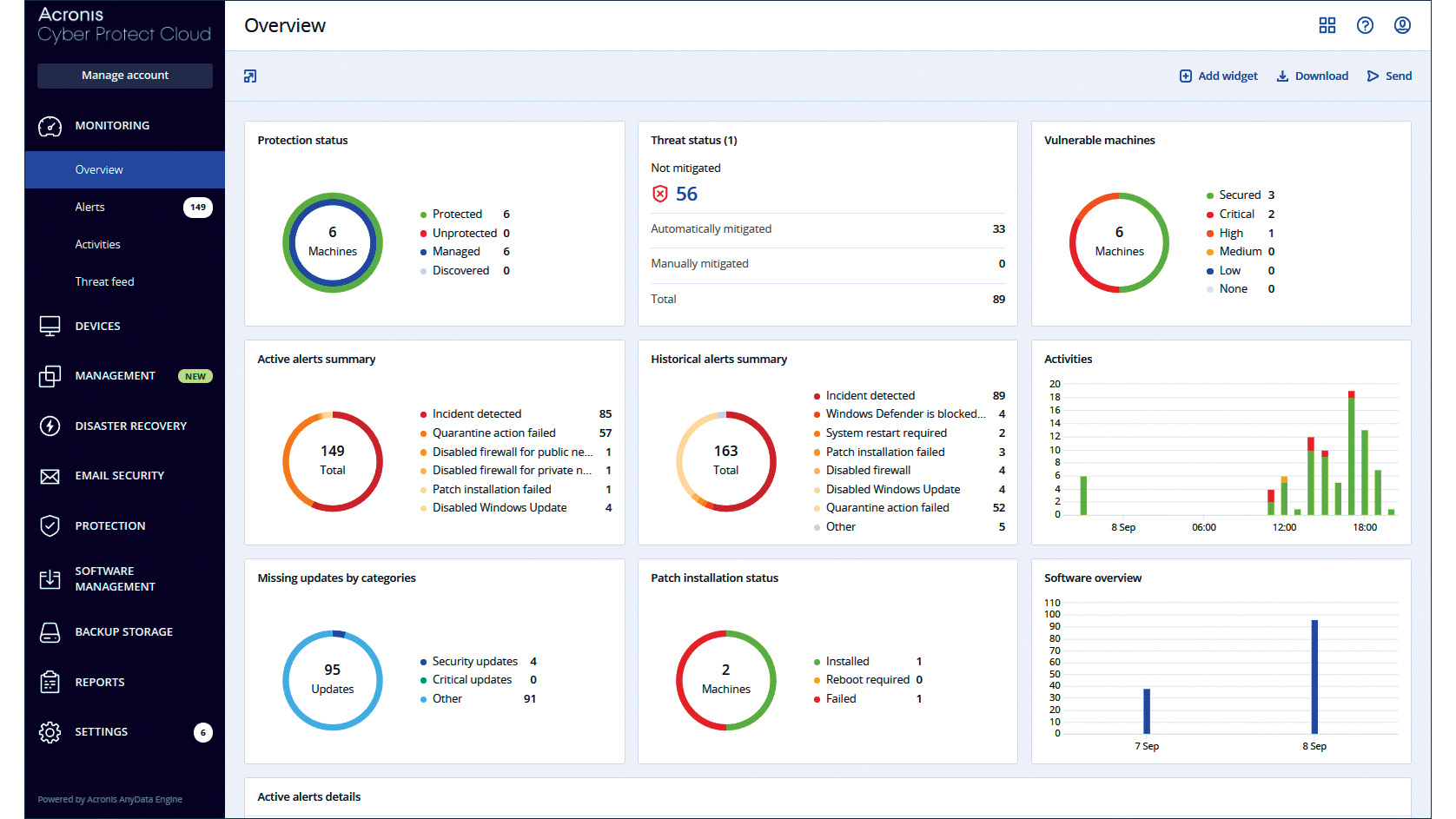 Acronis Cyber Protect Cloud review: Slick automated threat remediation
Acronis Cyber Protect Cloud review: Slick automated threat remediationReviews A single cloud service that neatly combines malware protection with backup and recovery features
-
 Tiny11 review: Windows 11 with only 2GB of RAM
Tiny11 review: Windows 11 with only 2GB of RAMReview A version of Windows 11 for older machines that don't meet the full requirements
-
 Red Hat Enterprise Linux becomes foundational operating system for Cohesity Data Cloud
Red Hat Enterprise Linux becomes foundational operating system for Cohesity Data CloudNews New strategic partnership between Red Hat and Cohesity aims to drive innovation in the data security and management space
-
 Microsoft defends “negligent” security approach that prolonged vulnerability fix for five months
Microsoft defends “negligent” security approach that prolonged vulnerability fix for five monthsNews The tech giant has refuted claims that its practices have left customers “in the dark”
-
 AlmaLinux follows Oracle in ditching RHEL compatibility
AlmaLinux follows Oracle in ditching RHEL compatibilityNews Application binary compatibility is now the aim with 1:1 now dropped
-
 What is platform engineering and will it see the end of DevSecOps?
What is platform engineering and will it see the end of DevSecOps?In-depth Platform engineering is not just the latest industry buzzword but could represent a profound change in how software is developed and governed