Night Dragon hackers smash energy multinationals
Hackers target global energy firms as they seek to gain insider information, McAfee reveals.


Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
You are now subscribed
Your newsletter sign-up was successful
The skills and tools used by the hackers were fairly orthodox, according to the report.
Firstly, the attackers used SQL-injection techniques to compromise their target's company extranet web servers, thereby allowing remote command execution.
They then uploaded widely available tools onto the compromised servers, providing access to internal desktops and servers. Password cracking tools let the hackers gain extra usernames and passwords.
By disabling Internet Explorer proxy settings, the infiltrators enabled direct communication from infected machines to the internet, allowing them to exfiltrate emails and other sensitive documents from company executives.
Spear-phishing techniques were also used to gain additional information from company accounts.
Although the hackers used typical techniques, this was not a sign that the energy companies' systems were weak, Day said.
"It's a sign of the complexity of the IT world we work in," he explained.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
"A SQL injection is something organisations see every day the challenge is most organisations, especially large ones, have such a breadth of environment and the challenge is being able to stay on top of all of that."
Day said it has become very hard for businesses to remain "100 per cent compliant" given the complexity of the security environment now.
Tom Brewster is currently an associate editor at Forbes and an award-winning journalist who covers cyber security, surveillance, and privacy. Starting his career at ITPro as a staff writer and working up to a senior staff writer role, Tom has been covering the tech industry for more than ten years and is considered one of the leading journalists in his specialism.
He is a proud alum of the University of Sheffield where he secured an undergraduate degree in English Literature before undertaking a certification from General Assembly in web development.
-
 Selecting a trusted infrastructure partner: A checklist for now and next
Selecting a trusted infrastructure partner: A checklist for now and nextSponsored With much to consider, what should be your key infrastructure concerns?
-
 Most organizations make a mess of handling digital disruption
Most organizations make a mess of handling digital disruptionNews Poor governance and a lack of collaboration with suppliers and partners can lead to disaster
-
 McAfee and Visa offer 50% off antivirus subscriptions for small businesses
McAfee and Visa offer 50% off antivirus subscriptions for small businessesNews UK Visa Classic Business card holders can access the deal starting today
-
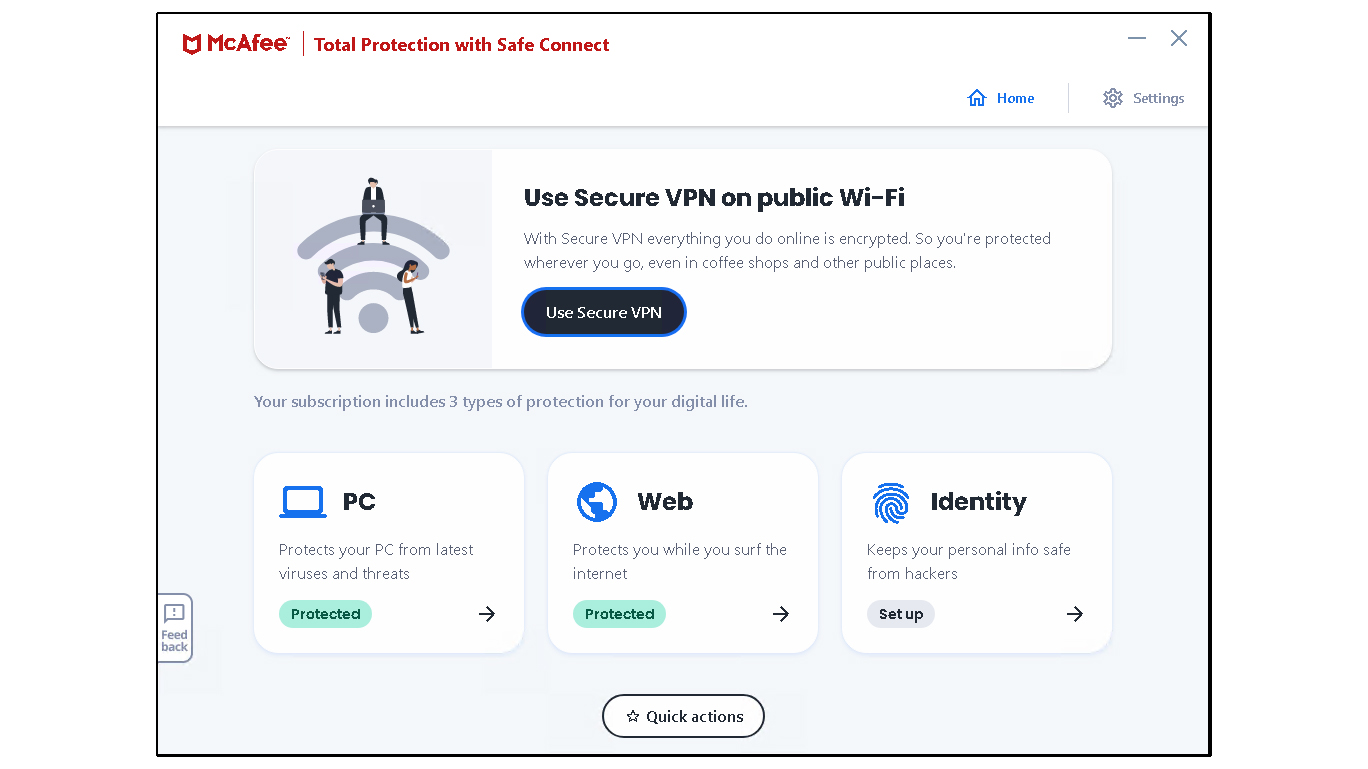 McAfee Total Protection review: Expensive at full price
McAfee Total Protection review: Expensive at full priceReviews Protects your PC and includes a decent firewall, but costly and less effective than some rivals
-
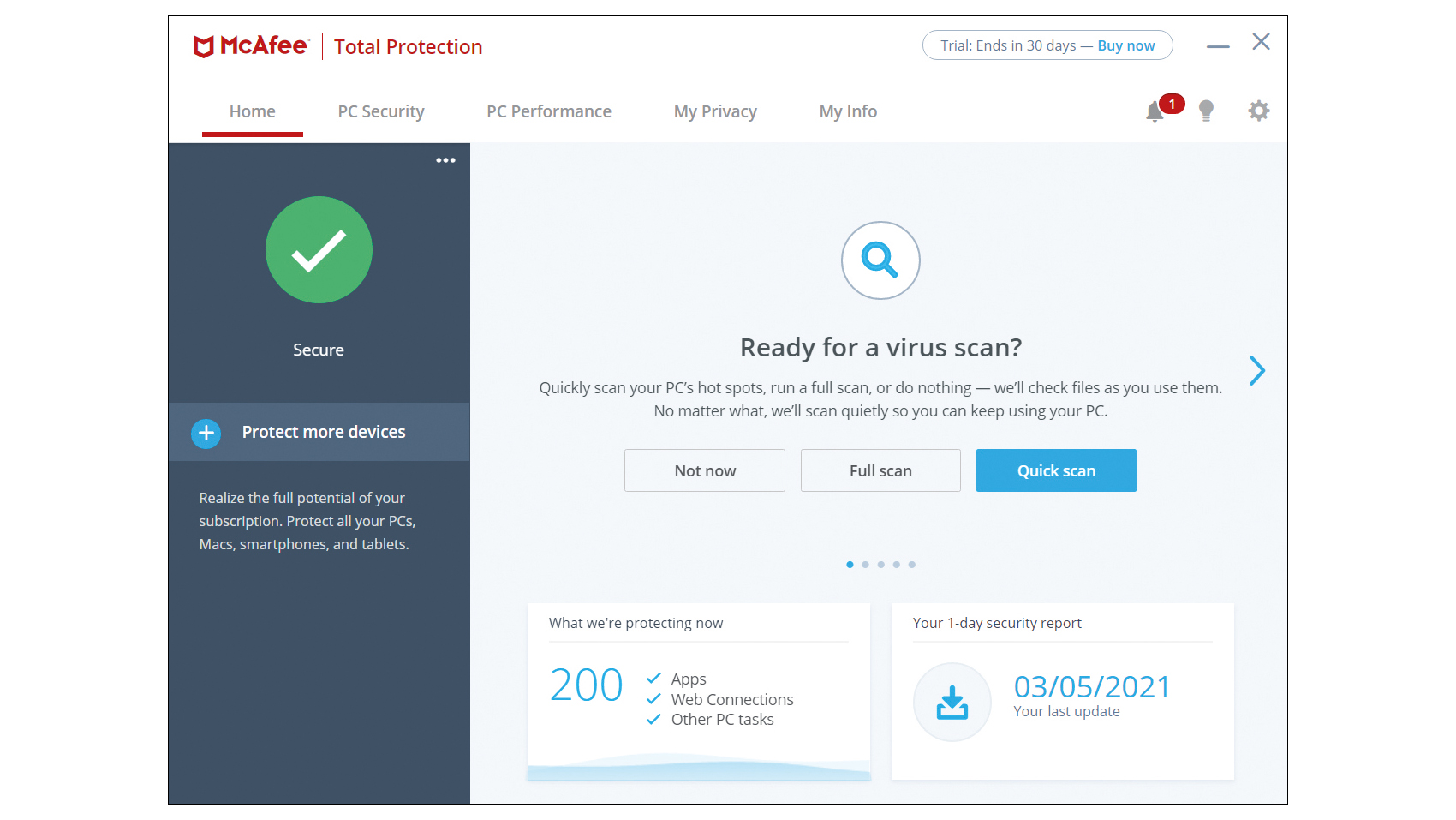 McAfee Total Protection review: Quick, effective and affordable
McAfee Total Protection review: Quick, effective and affordableReviews A solid security choice, with perfect malware protection, a fully functional VPN and more
-
 McAfee’s zero trust solution strengthens private applications’ security
McAfee’s zero trust solution strengthens private applications’ securityNews MVISION Private Access grants secure access to private resources from any device or location
-
 PowerShell threats increased over 200% last year
PowerShell threats increased over 200% last yearNews A new McAfee report finds PowerShell attacks driven largely by Donoff malware.
-
 McAfee to sell enterprise business to STG for £2.8 billion
McAfee to sell enterprise business to STG for £2.8 billionNews The enterprise business will be rebranded, with McAfee focusing on personal security
-
 Has the US government finally nabbed John McAfee?
Has the US government finally nabbed John McAfee?News Official Twitter account claims notorious tech tycoon has been “detained by authorities”
-
 John McAfee ordered to pay $25 million over neighbour's murder
John McAfee ordered to pay $25 million over neighbour's murderNews Controversial figure insists that he will not pay
