Tresorit Business Plus review: Perfect for handling confidential data
A seriously secure cloud collaboration and file-sharing service that’s very easy to use and great value for SMBs

-
+
Affordable
-
+
Highly secure
-
+
Easy to use

Businesses worried about storing and sharing confidential information in the cloud will love Tresorit, as this Swiss company has security as its top priority. Tresorit employs a zero-knowledge policy to encryption keys so nobody else but you can access your data. This latest version adds a raft of new features, including enhanced access controls, document usage analytics and stricter security policies for sharing data with external clients.
Ease of use is another winning attribute of this product, as Tresorit is exceptionally simple to deploy and manage. We reviewed the Business Plus plan and swiftly added new users simply by sending email invitations to them from its administrative web portal.
The message contains a download link for the Tresorit desktop app and, after installing it, users provide their full name, choose a password and wait while it creates their first personal “Tresor” – Tresorit’s jargon for a secure encrypted folder. Tresorit weaves its encryption magic behind the scenes so users only need to remember their password; if they forget it, administrators can use the portal’s Advanced Control feature to reset it for them.
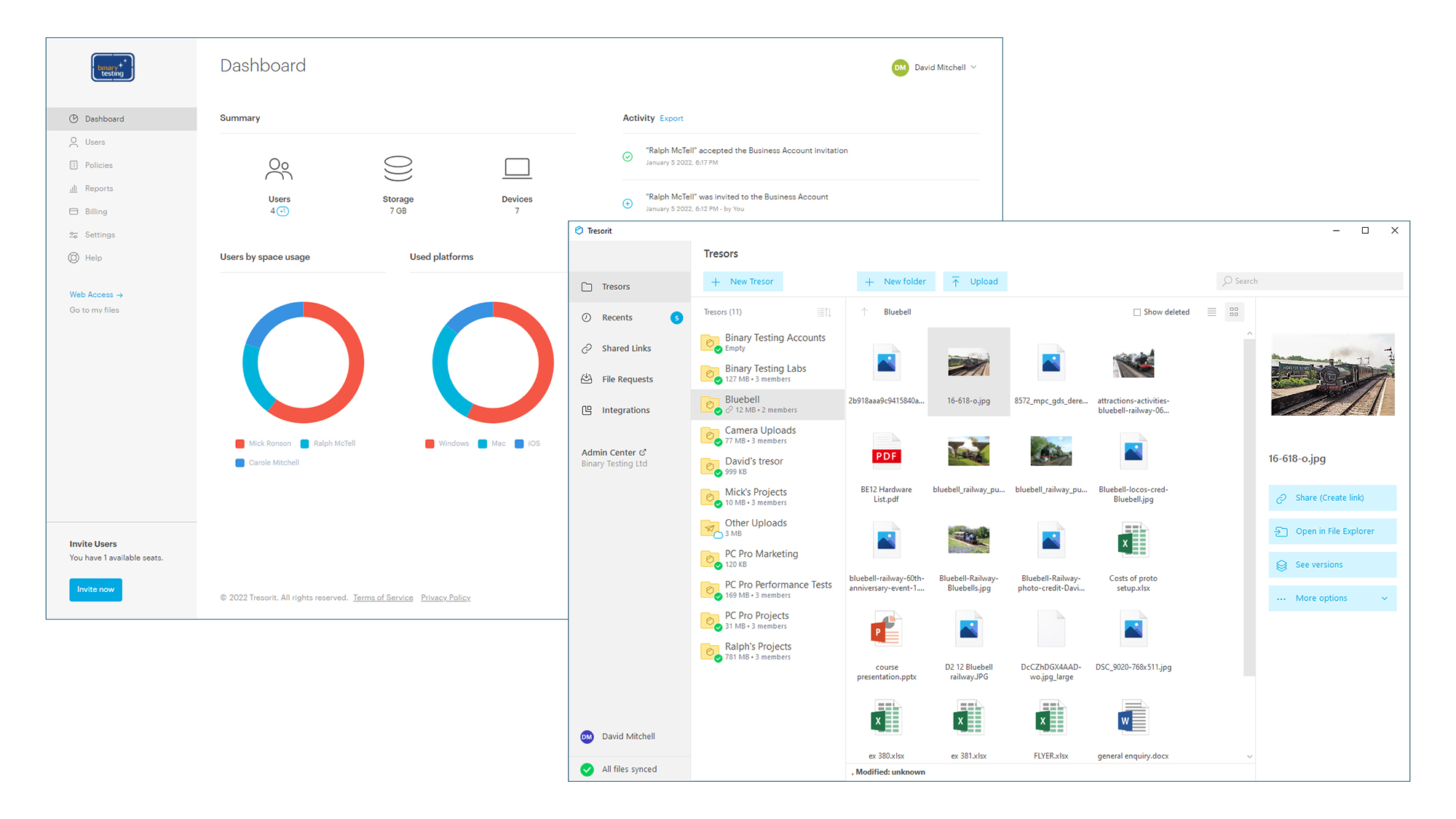
The portal’s dashboard summary shows the top three users and platforms, and you can view each user to see their Tresors, which devices they’ve been using and all their web sessions. Policies provide a wealth of access controls, including limiting account access from Windows, macOS, Linux, iOS and Android devices, enforcing single sign-on or two-factor authentication, setting login session limits in days and choosing which users can create file links.
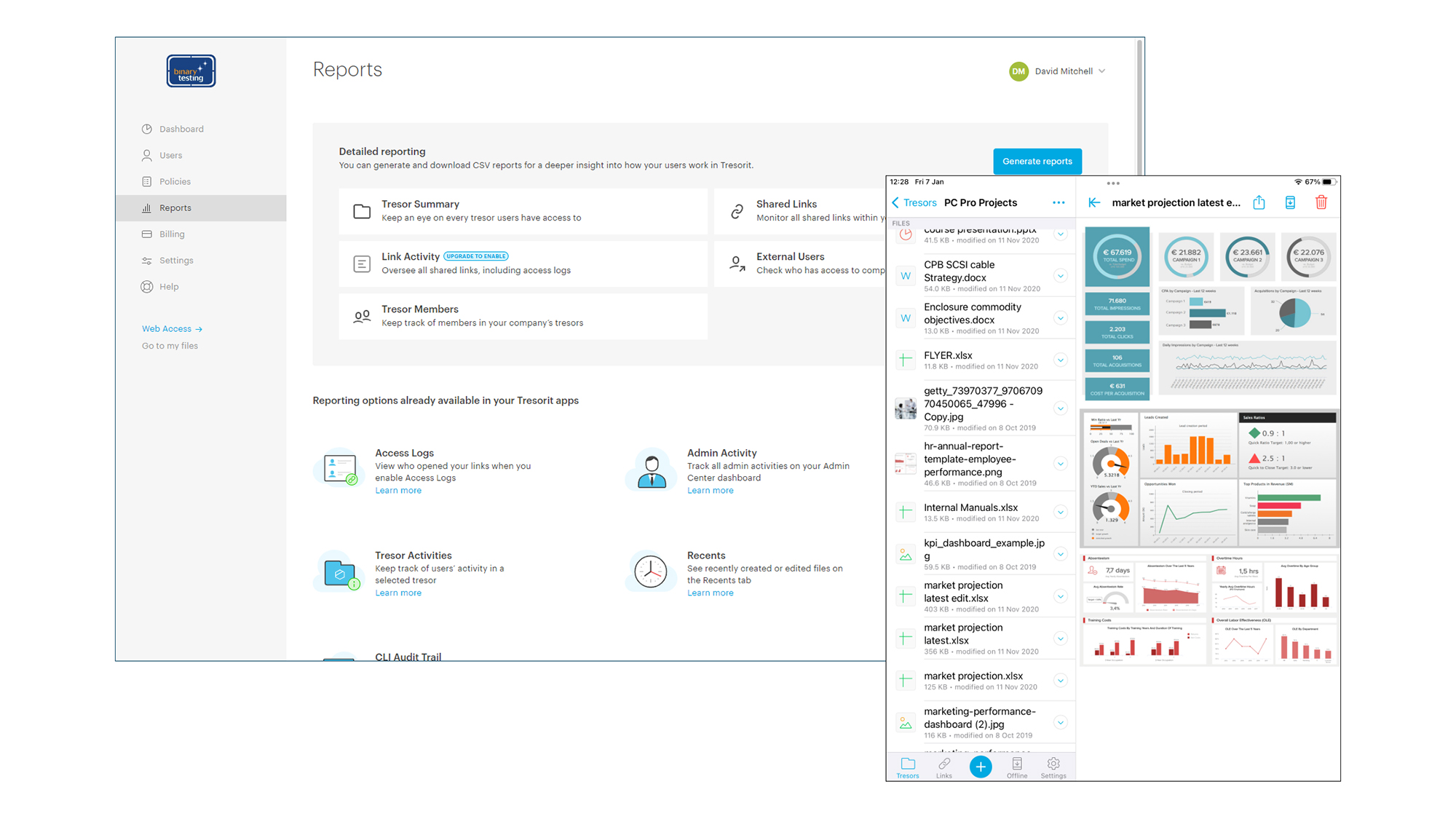
The Business Plus and Enterprise subscriptions include company email domain verification for keeping all your users under one roof and controlling their activities with global policies. Part of Tresorit’s Content Shield service, document analytics is available in the Enterprise version and allows users to track clients and see how they are engaging with documents sent to them.
Users can create any number of Tresors up to the limit of their personal cloud storage which, for the Business Plus plan, is 2TB each with a generous 15GB maximum file size. When creating Tresors, you can add an existing local folder, which is uploaded and synced with the cloud, or you can create a new one in the cloud and decide when to enable local syncing.
The well-designed desktop app makes it easy to view the contents of personal Tresors, upload new files to them, and move, delete or rename individual files. It creates a local drive for quick access to Tresors from Windows Explorer or the macOS Finder, and each user gets their own personal web portal.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
The desktop app and web portal can be used to share files and folders by selecting team members from a contact list and granting manager, editor or viewer privileges. Once recipients accept an invitation, the shares automatically appear in their app and portal.
External clients that don’t have a Tresorit account can join in as users can email secure file upload requests and file-sharing web links to them using their local email client, Outlook on the web or Gmail. For greater share security, you can add link expiration dates, set the number of times they can be opened or downloaded, apply password protection, enable access logging, and require recipients to verify their email address by entering the unique six-digit code sent to them by Tresorit when they first open the link.
SMBs that demand the toughest cloud file-sharing security won’t go wrong with Tresorit. Along with its total end-to-end encryption, its ease of use and extensive access controls add even more appeal, and the Business Plus plan compares well on price with the competition.
Dave is an IT consultant and freelance journalist specialising in hands-on reviews of computer networking products covering all market sectors from small businesses to enterprises. Founder of Binary Testing Ltd – the UK’s premier independent network testing laboratory - Dave has over 45 years of experience in the IT industry.
Dave has produced many thousands of in-depth business networking product reviews from his lab which have been reproduced globally. Writing for ITPro and its sister title, PC Pro, he covers all areas of business IT infrastructure, including servers, storage, network security, data protection, cloud, infrastructure and services.
-
 Dell raises annual forecasts as AI boom continues to reward hardware vendors
Dell raises annual forecasts as AI boom continues to reward hardware vendorsNews Supply chain adjustments and shrewd management of the memory chip shortage help Dell capitalize on increased demand for AI
By Bobby Hellard Published
-
 IBM and Red Hat believe they have the answer to open source security risks
IBM and Red Hat believe they have the answer to open source security risksNews Project Lightwell is backed by a $5 billion investment and a team of more than 20,000 engineers
By Emma Woollacott Published
-
 Security professionals want leaders who have already led their organization through a major cyber incident – regardless of how things turned out
Security professionals want leaders who have already led their organization through a major cyber incident – regardless of how things turned outNews Research from ISC2 reveals what makes for a good security leader
By Emma Woollacott Published

