Hackers use 200,000 insecure Brazilian routers to mine cryptocurrencies
The attack exploits a flaw that was previously patched

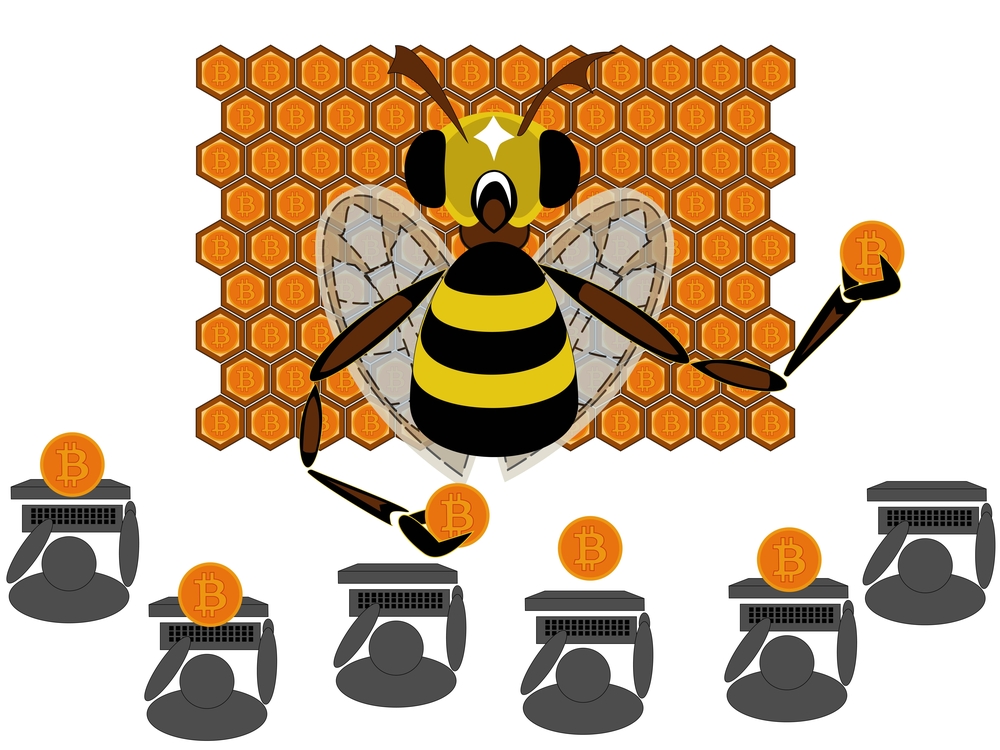
Hackers are using a network of vulnerable routers to spread crypto-mining malware to unsuspecting users, security researchers have discovered.
An unknown cyber criminal (or possibly a network of cyber criminals) is using a flaw in more than 170,000 routers manufactured by MikroTik to run scripts on the computers of unsuspecting victims which mine cryptocurrencies for the hacker, according to TrustWave researcher Simon Kenin.
The attack uses a previously-discovered flaw - which has since been patched by MikroTik - to inject a mining script from CoinHive into the browser of anyone connected to an infected router. Most of the affected devices are located in Brazil, but Kenin warned that the attack has been observed in other places as well.
Another researcher, Troy Mursch, also observed a similar case in Moldova involving more than 25,000 MikroTik routers running CoinHive scripts. It is currently unknown whether the two attacks are connected.
The security flaw that allows the routers to be exploited has now been addressed by MikroTik, but numerous devices remain unpatched. This is a big problem, Kenin explains, as MikroTik manufacture high-end equipment that is often used by ISPs, web companies and businesses.
"Let me emphasize how bad this attack is," he said. "The attacker wisely thought that instead of infecting small sites with few visitors, or finding sophisticated ways to run malware on end user computers, they would go straight to the source; carrier-grade router devices."
"There are hundreds of thousands of these devices around the globe, in use by ISPs and different organizations and businesses, each device serves at least tens if not hundreds of users daily."
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
Adam Shepherd has been a technology journalist since 2015, covering everything from cloud storage and security, to smartphones and servers. Over the course of his career, he’s seen the spread of 5G, the growing ubiquity of wireless devices, and the start of the connected revolution. He’s also been to more trade shows and technology conferences than he cares to count.
Adam is an avid follower of the latest hardware innovations, and he is never happier than when tinkering with complex network configurations, or exploring a new Linux distro. He was also previously a co-host on the ITPro Podcast, where he was often found ranting about his love of strange gadgets, his disdain for Windows Mobile, and everything in between.
You can find Adam tweeting about enterprise technology (or more often bad jokes) @AdamShepherUK.
-
 European Commission opens public consultation on draft for high-risk AI guidelines
European Commission opens public consultation on draft for high-risk AI guidelinesNews Guidance aims to help organizations and regulators decide whether their AI products and deployments need to conform to tougher rules
-
 Microsoft reveals Surface Pro and Surface Laptop for Business
Microsoft reveals Surface Pro and Surface Laptop for BusinessNews New 13in Pro and Laptop claim big performance improvements and vast AI capabilities
-
 Anthropic targets vulnerability detection gains with Claude Security public beta — here's what users can expect
Anthropic targets vulnerability detection gains with Claude Security public beta — here's what users can expectNews The Claude Mythos developer is aiming for a more limited approach to cyber tooling for public consumption
-
 Researchers warn millions of RDP and VNC servers are wide open to exploitation
Researchers warn millions of RDP and VNC servers are wide open to exploitationNews Researchers at Forescout spotted millions of RDP and VNC servers exposed online
-
 Brace yourselves for a vulnerability explosion, Forescout warns
Brace yourselves for a vulnerability explosion, Forescout warnsNews AI advances are helping identify software flaws at record pace and scale, but that's not the good news some would think
-
 Ubuntu vulnerability exposes enterprises to root escalation, complete system compromise
Ubuntu vulnerability exposes enterprises to root escalation, complete system compromiseNews The high-severity Ubuntu vulnerability allows an unprivileged local attacker to escalate privileges through the interaction of two standard system components
-
 Security agencies issue warning over critical Cisco Catalyst SD-WAN vulnerability
Security agencies issue warning over critical Cisco Catalyst SD-WAN vulnerabilityNews Threat actors have been exploiting the vulnerability to achieve root access since 2023
-
 Millions of developers could be impacted by flaws in Visual Studio Code extensions – here's what you need to know and how to protect yourself
Millions of developers could be impacted by flaws in Visual Studio Code extensions – here's what you need to know and how to protect yourselfNews The VS Code vulnerabilities highlight broader IDE security risks, said OX Security
-
 CVEs are set to top 50,000 this year, marking a record high – here’s how CISOs and security teams can prepare for a looming onslaught
CVEs are set to top 50,000 this year, marking a record high – here’s how CISOs and security teams can prepare for a looming onslaughtNews While the CVE figures might be daunting, they won't all be relevant to your organization
-
 Microsoft patches six zero-days targeting Windows, Word, and more – here’s what you need to know
Microsoft patches six zero-days targeting Windows, Word, and more – here’s what you need to knowNews Patch Tuesday update targets large number of vulnerabilities already being used by attackers

