What is the Computer Misuse Act?
Knowing what the Computer Misuse Act is helps you understand how and when legislation keeps your systems safe


It’s important to know what the Computer Misuse Act (CMA) is, as it forms the backbone of law enforcement against hacking in the UK. It’s through this law that UK legislators enforce protections for devices and data and in the UK, like their international counterparts.
The CMA was first introduced in the UK in 1990 and sought to draw boundaries between lawful and unlawful access to a computer system and its data. The CMA intended to criminalize any unauthorized activity of this nature.

The UK government has updated the CMA several times in the decades since, to match contemporary cyber threats. A particularly major overhaul was passed in 2015, which aligned the CMA with EU law and with the Serious Crime Act 2015 through added protections for attacks on personal property.
Some have argued that the CMA is seriously out of date and should be subjected to a more radical overhaul to address growing attacks on the UK and new concerns such as the cyber security implications of generative AI.
Computer Misuse Act summary and criticisms
The CMA is used to protect against and prosecute hackers and would-be cyber criminals. In 2022, computer misuse accounted for 14% of total UK crime and the CMA has provisions to cover a broad variety of criminal digital activity.
One of several laws that protects the devices and data of UK citizens, the CMA sits alongside the Data Protection Act 2018 and UK GDPR. It has alsom been joined by government projects such as the UK’s National Cyber Strategy, which seeks to shore up the UK’s digital skills.
Why was the Computer Misuse Act introduced?
Much of the justification for the CMA lay in the 1988 case of Regina v Gold and Schifreen, which saw two hackers gain access to a BT data service using stolen engineer credentials obtained through shoulder surfing.
Both individuals were found guilty under the Forgery and Counterfeiting Act 1981, but this was subsequently overturned on appeal as they did not commit the hacking for profit, a specification of the 1981 Act. This helped to expose gaps in the law that had to be filled, with legal experts expressing concerns that the case set a precedent for recreational hacking being legal activity. Two years later, the CMA was introduced to parliament.
What are the Computer Misuse Act penalties?
There are four penalty levels if you are prosecuted under the CMA, applied in proportion to the severity of the Act. They range from potential fines to imprisonment.
The first level applies if one gains unauthorized access to a computer without permission, you could face a penalty of up to two years in prison and a £5,000 ($6,254) fine.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
Those who gain access to a computer without permission to steal data or take part in another crime, such as using that data to commit fraud, will be tried under the second penalty level. For this, you face a sentence of up to 10 years in prison and can receive an unlimited fine. The extent of the punishment depends on the severity of the individual case, and the prosecution has to prove they had intent to commit another crime with illicit access, which can be difficult.
RELATED RESOURCE

More than a number: Your risk score explained
Leverage a company-wide risk index to make a high-level assessment of your organization’s risk
If one modifies the content of a computer or provides the tools for others to alter or destroy them, for example through the sale of ransomware, they could face a prison sentence of up to ten years alongside an unlimited fine.
The final level relates to those who perform acts that cause or risk causing serious material damage. It carries a maximum prison sentence of 14 years, but if this potential damage is found to threaten human well-being or put national security at risk the sentence could be up to life imprisonment.
How has the Computer Misuse Act changed?
When the CMA was passed in 1990, computers were not yet commonly used and the act was therefore unable to anticipate all the cyber threats of the coming decades. If one had access to a computer back then, it was likely at a place of work and commercial internet access was still years away. Nowadays we access the internet and use devices like laptops and tablets every day, with the threat landscape having grown in tandem.
Legislators have been repeatedly forced to tweak the act to adapt to new online threats. For example, updates to the law added definitions for cyber attack methods that criminals could carry out, as well as considering the preparation required to launch an attack as a malicious action in and of itself.
The legislation was additionally amended in 2015, thanks to the Serious Crime Act, which included specific passages on computer misuse and introduced three alterations to the original law. Amendments in Section 3ZA defined unauthorized acts causing serious damage as offenses and brought the EU Directive on Attacks against Information Systems into law in the UK. It also sought to clarify the "savings" provision that protects law enforcement from prosecution for acts performed on computers under powers of inspection or examination.
In a fact sheet [PDF], the government stated that the new offense of unauthorized acts causing serious damage "addresses the most serious cyber attacks, for example, those on essential systems controlling power supply, communications, food or fuel distribution".
This helped to align the CMA with the severe nature of modern cyber crime, with organizations such as the National Cyber Security Centre (NCSC) having warned of advanced attacks on critical national infrastructure (CNI) by Russia-aligned threat actors. The government’s own National Risk Register (NRR) report has also compared cyber threats to chemical weapons in terms of severity, particularly those that could affect critical utilities.
Until this provision, the most serious crime covered by the act was the aforementioned section 3 offense of unauthorized access to impair the operation of a computer, which carries a maximum penalty of 10 years. The government argued that this "did not sufficiently reflect the level of personal and economic harm that a major cyber attack on critical systems could cause". Therefore, conviction under the new offense can result in a more severe prison sentence, of up to 14 years.
Changes made regarding the EU Directive on Attacks against Information Systems extended extraterritorial jurisdiction, increasing the ease with which cyber criminals using the UK as a base of operations can be prosecuted. It applies even if they are not physically located within the UK, and also allows the police and Crown Prosecution Service (CPS) to pursue and prosecute UK residents for cyber crimes committed overseas.
What are the Computer Misuse Act's problems?
Additions to the CMA have been far from a cure-all, and in many cases have simply complicated the legal landscape through which legitimate computer users must navigate.
Section 37 of the Police and Justice Act of 2006 is one of many provisions that has faced criticism for its poorly conceived scope, with its sub-section 3a stating that making, supplying, or obtaining any articles for use in a malicious act using a computer is categorized as criminal activity. Under this legislation, owning any hacking software or exploit tools is a crime, even if you are a ‘white hat’ hacker using them for ethical hacking, or for researching security threats.
A provision relating to protection for law enforcement accessing computers in the act of investigation caused much controversy. The government argued that the changes were made "to remove any ambiguity for the lawful use of powers to investigate crime (for example under Part 3 of the Police Act 1997) and the interaction of those powers with the offenses in the 1990 Act".
"The changes do not extend law enforcement agencies' powers but merely clarify the use of existing powers (derived from other enactments, wherever exercised) in the context of the offenses in the 1990 Act," it added.
However, civil rights groups including Privacy International have argued that the changes are far too broad, and that complete legal exemption for police and spy agencies such as MI5 is excessive and unwarranted. Privacy raised concerns in a case to the European Court of Human Rights along with five other complainants.
Is the Computer Misuse Act fit for purpose?
Recent years have seen repeated calls to reform or scrap the CMA, with many security researchers and law enforcement professionals citing its ability to cope with the complexities of modern-day computing.
Some point to the act’s relatively poor record of backing criminal investigations, with around less than 1% of computer hacking offenses investigated in the UK in 2019 resulting in prosecution. The National Fraud Intelligence Bureau (NFIB) does not link individual computer misuse offenses to their outcomes, which makes analysis of its effectiveness difficult.
There is also little evidence of the CMA acting as a deterrent to criminals, with the 850,000 offenses of computer misuse reported by the Crime Survey for England and Wales (CSEW) in the year ending June 2023 similar to the 876,000 offenses recorded in the year ending March 2020. Much CMA criticism hinges on the limitations of the act’s definitions and its binary view on hacking.
The definition of 'computer' in the Act
Perhaps the most obvious criticism is that the act represents a time when ‘computer’ is mainly referred to as a desktop or all-in-one PC. In this regard, it fails to account for much of the innovation of the 21st century, putting it well out of step with the demands of the modern world.
“The Computer Misuse Act 1990 contains several issues that apply subjectivity when objectivity should be the test,” argues Tim Mackey, principal security strategist at the Synopsys Cybersecurity Research Centre. “The term “computer” isn’t defined and the contemporary definition of “computer” has likely shifted in the intervening thirty years.”
This lack of clear definition creates a “grey area”, adds Mackey, where prosecutors are forced to apply the act based on subjective interpretation, rather than objective information.
“This can lead to interesting scenarios that would question whether a smartphone, nanny-cam, Wi-Fi-connected dishwasher, or CCTV system are in fact computers – despite the reality that each of these devices often runs a general-purpose operating system, is connected to a network, and runs software at the behest of its user.”
Failure to keep up with novel cyber threats
Another area of criticism for the CMA is that it has failed to keep up with the developments in cyber crime landscape such as the rise in identity-based attacks and business email compromise (BEC).
“The types of crime the act was originally designed to fight are actually decreasing – but new threats are emerging seemingly every month,” says Peter Yapp, Partner at law firm Schillings and former deputy director of the UK’s NCSC. “For example, hacking for extortion has nearly doubled over the past year while virus/malware reports have dropped. This underlines one of the main shortfalls of the act – the evolution of using computers to commit fraud to the computer becoming the main conduit for fraud.”
RELATED RESOURCE
An EDR buyer's guide
How to pick the best endpoint detection and response solution for your business
The subjective interpretation of the Act ultimately drives a wedge between the legal system and security researchers, and some have argued that judges often appear to misunderstand the wider issues facing the industry.
“In essence, the Act isn’t working for cyber security practitioners, law enforcement officers, the Crown Prosecution Office and the Courts,” adds Yapp. “Even more worryingly, judges don’t seem to understand the issues. For example, Southwark Crown Court is supposedly a specialist fraud center that deals with the majority of the serious and major fraud cases in England and Wales, but its level of understanding around computer crime isn’t sufficient to facilitate any significant number of successful prosecutions. The police have dedicated many more resources to this area over the past five years, but until every police officer understands cybercrime, we will be playing catch up.”
Richard Millett, training development manager at Firebrand Training and regular cyber security advisor for police forces across the UK, explains that many cyber crime cases are instead tried under other legislation, such as fraud and theft, not only because of a lack of definitions but also because it allows stricter penalties to be issued.
“If you look at the tariffs for the various sections under the [Computer Misuse] Act you see that the penalties defined do not match the severity of some of the offenses that have been committed,” says Millett. “It is only when you look at section 3za which covers “causing or creating a risk of serious damage” do you see tariffs of “imprisonment for life”. The financial and economic damage that has been inflicted by some individuals is not reflected in the penalties that have been applied, running into millions in many cases.”
How the Computer Misuse Act limits ethical hacking
The greatest challenge facing cyber security researchers trying to operate within the scope of the act is its failure to distinguish between criminal and ethical hacking.
As Rob Shooter, managing partner of law firm Fieldfisher explains to ITPro, many in the industry argue that offenses under the CMA are too “broad brush”, leaving cyber security researchers with little legal room to perform ethical hacking against cyber criminals.
The Act defines non-consensually accessing a computer system as a crime, regardless of the intent or benefits that may come about as a result of the action. Technically, this means that core cyber security skills and research tasks used to analyze potential threats from probing for vulnerability management, file interrogation, or analyzing compromised systems are illegal unless consent has been given by both the victim and perpetrator of the crime.
“As an example, there are a multitude of US-based companies offering vulnerability scanning services of the extended supply chain, whereas there are few, if any, UK companies offering the same service,” explains Yapp.
Although this technicality may limit the actions of ethical hacking or may leave some wary about potential prosecution, Yapp adds that he is unaware of any cases involving UK researchers being sanctioned by law enforcement as a direct result of their work.

Jane McCallion is Managing Editor of ITPro and ChannelPro, specializing in data centers, enterprise IT infrastructure, and cybersecurity. Before becoming Managing Editor, she held the role of Deputy Editor and, prior to that, Features Editor, managing a pool of freelance and internal writers, while continuing to specialize in enterprise IT infrastructure, and business strategy.
Prior to joining ITPro, Jane was a freelance business journalist writing as both Jane McCallion and Jane Bordenave for titles such as European CEO, World Finance, and Business Excellence Magazine.
-
 ‘Perfect’ Zero Trust is killing your mid-market productivity
‘Perfect’ Zero Trust is killing your mid-market productivitySponsored Security theory often collapses under real-world deadlines. It’s time for a more auditable, “human-centric” approach to privileged access management
-
 Increased AI use means developers spend more time reviewing code than ever
Increased AI use means developers spend more time reviewing code than everNews While AI is improving productivity and efficiency, many developers are caught up in a vicious cycle of code reviews and bug hunting
-
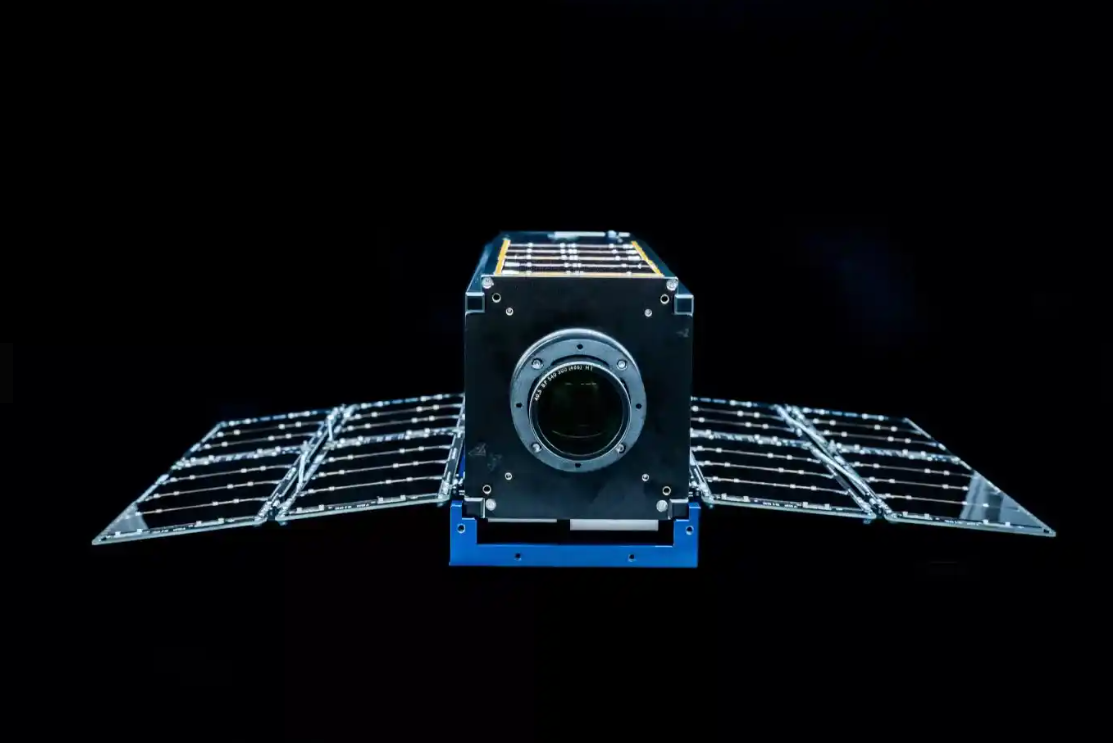 Why the Space Force wants white hats to attack a satellite
Why the Space Force wants white hats to attack a satelliteCase study Authorities hope the first-of-its-kind competition could bring benefits to the cyber sector
-
 OpenAI to pay up to $20k in rewards through new bug bounty program
OpenAI to pay up to $20k in rewards through new bug bounty programNews The move follows a period of unrest over data security concerns
-
 New ‘DarkBit’ ransomware gang shuts down Technion, demands $1.7 million ransom
New ‘DarkBit’ ransomware gang shuts down Technion, demands $1.7 million ransomNews A politically charged ransom note suggests DarkBit are one of the newest hacktivist gangs to emerge in recent months
-
 Research: Luxury cars and emergency services vehicles vulnerable to remote takeover
Research: Luxury cars and emergency services vehicles vulnerable to remote takeoverNews A "global API issue" has been highlighted through months-long research into brands such as Ferrari and Mercedes-Benz, leaving owners open to hacking, account takeovers, and more
-
 Podcast transcript: Meet the cyborg hacker
Podcast transcript: Meet the cyborg hackerIT Pro Podcast Read the full transcript for this episode of the IT Pro Podcast
-
 The IT Pro Podcast: Meet the cyborg hacker
The IT Pro Podcast: Meet the cyborg hackerIT Pro Podcast Resistance is futile - offensive biotech implants are already here
-
 SpaceX bug bounty offers up to $25,000 per Starlink exploit
SpaceX bug bounty offers up to $25,000 per Starlink exploitNews The spacecraft manufacturer has offered white hats immunity to exploit a wide range of Starlink systems, with a dedicated report page
-
 Nomad happy to forgive hackers if they return 90% of $190 million that was stolen
Nomad happy to forgive hackers if they return 90% of $190 million that was stolenNews The crypto bridge is offering 'white hat hackers' a 10% bounty following the attack earlier this week
