Windows Phone Wi-Fi flaw puts user passwords at risk
Weak encryption allows hackers to steal passwords from Windows Phones.


A vulnerability in how Windows Phone devices connect to wireless access points and handle encryption could disclose corporate passwords, it is feared.
In an advisory, Microsoft warns that a flaw in a protocol known as PEAP-MS-CHAPv2 (Protected Extensible Authentication Protocol with Microsoft Challenge Handshake Authentication Protocol version 2), used by Windows Phones for WPA2 Wi-Fi access could allow hackers to snoop passwords from users.
In vulnerable scenarios, an attacker who successfully exploited this issue could achieve information disclosure against the targeted device.
To exploit this issue, an attacker-controlled system could pose as a known Wi-Fi access point, causing the targeted device to automatically attempt to authenticate with it, and in turn allow the attacker to intercept the victim's encrypted domain credentials.
An attacker could then exploit cryptographic weaknesses in the PEAP-MS-CHAPv2 protocol to obtain the victim's domain credentials.
"Those credentials could then be re-used to authenticate the attacker to network resources, and the attacker could take any action that the user could take on that network resource," the firm said.
"In vulnerable scenarios, an attacker who successfully exploited this issue could achieve information disclosure against the targeted device."
The software giant said it is not currently aware of any active attacks involving the flaw or of any customers who have been affected by it.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
"Microsoft is actively monitoring this situation to keep customers informed and to provide customer guidance as necessary," the company stated.
The vulnerability affects Windows Phone 7.8 and 8 devices but not earlier versions of the mobile operating system, according to Microsoft.
The firm has not issued a patch but is urging organisations to use a certificate verifying a wireless access point before starting an authentication process from Windows Phone 8 devices.
"A Windows Phone 8 device can be configured to validate a network access point to help make sure the network is your company's network before starting an authentication process," the advisory stated.
"This can be done by validating a certificate that's on your company's server. Only after validating the certificate is user name and password information sent to the authentication server."
Rene Millman is a freelance writer and broadcaster who covers cybersecurity, AI, IoT, and the cloud. He also works as a contributing analyst at GigaOm and has previously worked as an analyst for Gartner covering the infrastructure market. He has made numerous television appearances to give his views and expertise on technology trends and companies that affect and shape our lives. You can follow Rene Millman on Twitter.
-
 Kaseya shifts from AI ‘insights’ to autonomous action with new agentic platform
Kaseya shifts from AI ‘insights’ to autonomous action with new agentic platformNews The company aims to evolve from its suite of management tools into an autonomous operating system for MSPs
-
 Accenture to roll-out Copilot to 700,000+ staff
Accenture to roll-out Copilot to 700,000+ staffNews Accenture will roll out Microsoft Copilot to nearly three quarters of a million employees after years of testing
-
 Best Windows Phone apps for 2018
Best Windows Phone apps for 2018Best We list the important Windows Phone apps to help you choose what to download
-
 Getting Windows onto your new SSD
Getting Windows onto your new SSDTutorials Whether you want to start afresh or migrate from an existing disk, here’s how to make the move
-
 RIP Windows Phone: Microsoft ends support for its dying OS
RIP Windows Phone: Microsoft ends support for its dying OSNews Windows Phone 8.1's support finished yesterday - will Windows 10 Mobile last much longer?
-
 Facebook messenger not working? Your phone might be too old
Facebook messenger not working? Your phone might be too oldNews Certain smartphone users will no longer be able to access their Facebook messages
-
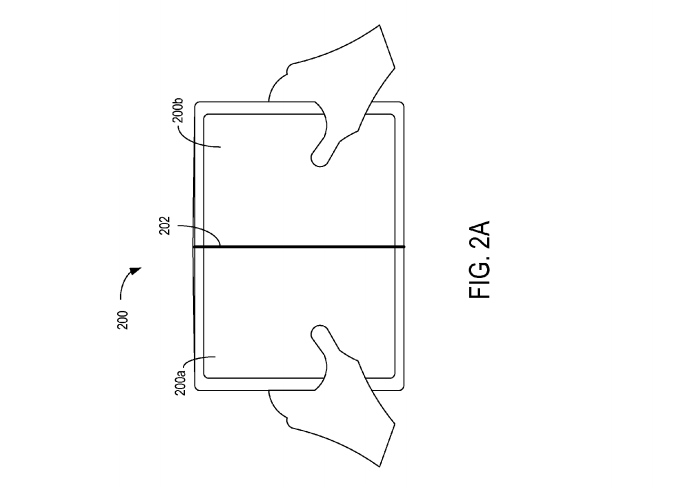 Microsoft patents a foldable Surface phone
Microsoft patents a foldable Surface phoneNews Will Microsoft build a Surface flip phone?
-
 Microsoft shifts its focus on tools and devices for creative professionals
Microsoft shifts its focus on tools and devices for creative professionalsNews At yesterday's event, Microsoft announced several products developed to help people 'create'
-
 Microsoft axes nearly 3,000 staff from smartphone division
Microsoft axes nearly 3,000 staff from smartphone divisionNews Total number of job cuts, across smartphone hardware and sales, in 2016 climbs to 4,700
-
 Microsoft's results show Windows Phone really is dead
Microsoft's results show Windows Phone really is deadNews Overall, Microsoft income slumps to $20 billion despite cloud gains
