Zoom starts rolling out end-to-end encryption for all users
A technical preview is available now, but Zoom has warned that it will block certain functions such as cloud recording and live transcription


Zoom has started rolling out end-to-end encryption (E2EE) to both free and paying users.
E2EE is now available in technical preview on the Zoom desktop client version for macOS and Windows, the Zoom Android app and Zoom Rooms, with the Zoom iOS app currently pending App Store approval.
Zoom’s E2EE uses the same 256-bit AES-GCM encryption that secures Zoom meetings by default. Account administrators can enable the feature in the web dashboard at an account, group, and user level, and participants must also enable the feature to join a meeting with end-to-end encryption.
When E2EE is enabled, nobody except each participant - not even Zoom’s meeting servers - has access to the encryption keys that are used to secure the meeting.
However, the company has warned that at least in the first stage of the four-phase rollout, E2EE will block certain Zoom functions, including cloud recording, streaming, live transcription, Breakout Rooms, polling, 1:1 private chat, and meeting reactions.
“End-to-end encryption is another stride toward making Zoom the most secure communications platform in the world,” said Zoom CEO Eric S. Yuan.
RELATED RESOURCE
A guide to becoming cloud-native smart and secure
The transcendence of cloud-native application development
“This phase of our E2EE offering provides the same security as existing end-to-end-encrypted messaging platforms, but with the video quality and scale that has made Zoom the communications solution of choice for hundreds of millions of people and the world’s largest enterprises.”
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
Phase 2 of the E2EE rollout is "tentatively roadmapped" for 2021, according to Zoom.
The rollout of end-to-end encryption comes five months after Zoom initially announced plans to add support for the security standard. However, at the time it said it would only be available for businesses and institutions that pay for a premium Zoom subscription. Following backlash from users and privacy activists, Zoom backtracked two week's later and announced that it would make E2EE available to both free and paying users.
Carly Page is a freelance technology journalist, editor and copywriter specialising in cyber security, B2B, and consumer technology. She has more than a decade of experience in the industry and has written for a range of publications including Forbes, IT Pro, the Metro, TechRadar, TechCrunch, TES, and WIRED, as well as offering copywriting and consultancy services.
Prior to entering the weird and wonderful world of freelance journalism, Carly served as editor of tech tabloid The INQUIRER from 2012 and 2019. She is also a graduate of the University of Lincoln, where she earned a degree in journalism.
You can check out Carly's ramblings (and her dog) on Twitter, or email her at hello@carlypagewrites.co.uk.
-
 Okta and Palo Alto Networks are teaming up to ‘fight AI with AI’
Okta and Palo Alto Networks are teaming up to ‘fight AI with AI’News The expanded partnership aims to help shore up identity security as attackers increasingly target user credentials
-

 Sophos XGS 116 review: A small and mighty appliance
Sophos XGS 116 review: A small and mighty applianceReviews This clever and compact security gateway brings outstanding security and remote management features at a tempting price
-

 WatchGuard Firebox M290 review: Stiff security at a great price
WatchGuard Firebox M290 review: Stiff security at a great priceReviews The Firebox M290 delivers an incredible range of gateway security measures priced right for SMBs
-
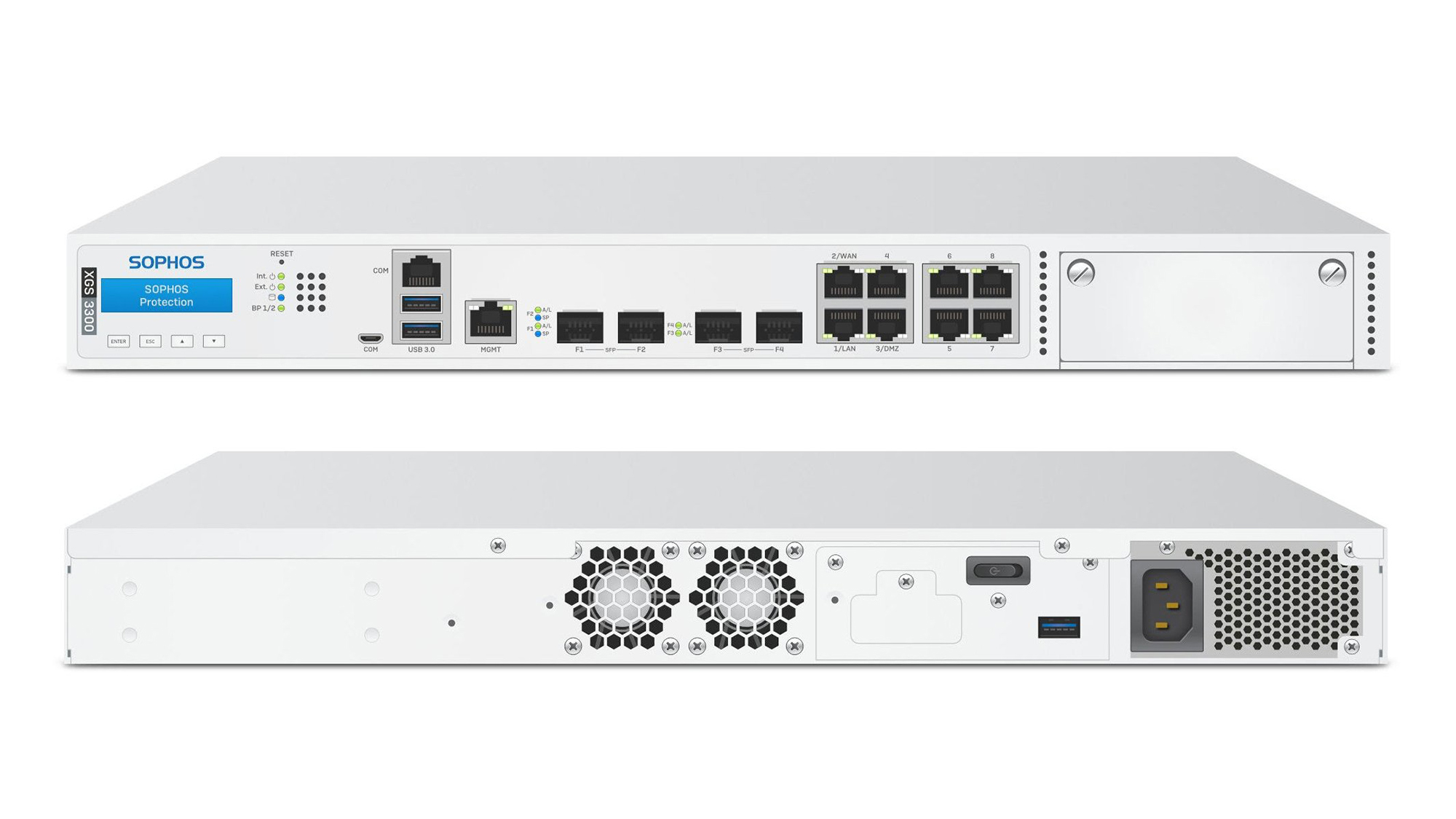
 Sophos XGS 3300 review: Xstream firewall performance
Sophos XGS 3300 review: Xstream firewall performanceReviews A powerful firewall appliance combining hardware acceleration with a vast array of security measures
-

 Ubiquiti Networks UniFi Dream Machine Pro review: All the security you need in one handy box
Ubiquiti Networks UniFi Dream Machine Pro review: All the security you need in one handy boxReviews An affordable security gateway that can take care of a wide range of security needs
-
 Big zero-day flaw found in Palo Alto security appliance
Big zero-day flaw found in Palo Alto security applianceNews Vulnerability in GlobalProtect VPN could enable hackers to take control of the security system
-
 SonicWall warns of imminent ransomware campaign on VPN hardware
SonicWall warns of imminent ransomware campaign on VPN hardwareNews Current and legacy secure VPN appliances under attack now
-
 Zyxel USG Flex 100 review: Flexible gateway security
Zyxel USG Flex 100 review: Flexible gateway securityReviews Perfect for SMBs, with the promise of cloud management coming soon


