Microsoft Authenticator mandates number matching to counter MFA fatigue attacks
The added layer of complexity aims to keep social engineering at bay


Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
You are now subscribed
Your newsletter sign-up was successful
Microsoft Authenticator will now enforce number matching for all push notifications to make multi-factor authentication (MFA) less susceptible to social engineering attacks.
High-profile cyber criminals have seen success exploiting MFA fatigue attacks. These involve sending a barrage of MFA push notification requests to organizations’ staff, often at unsociable hours, to manipulate them into authenticating a login attempt just to clear the frustrating notifications.
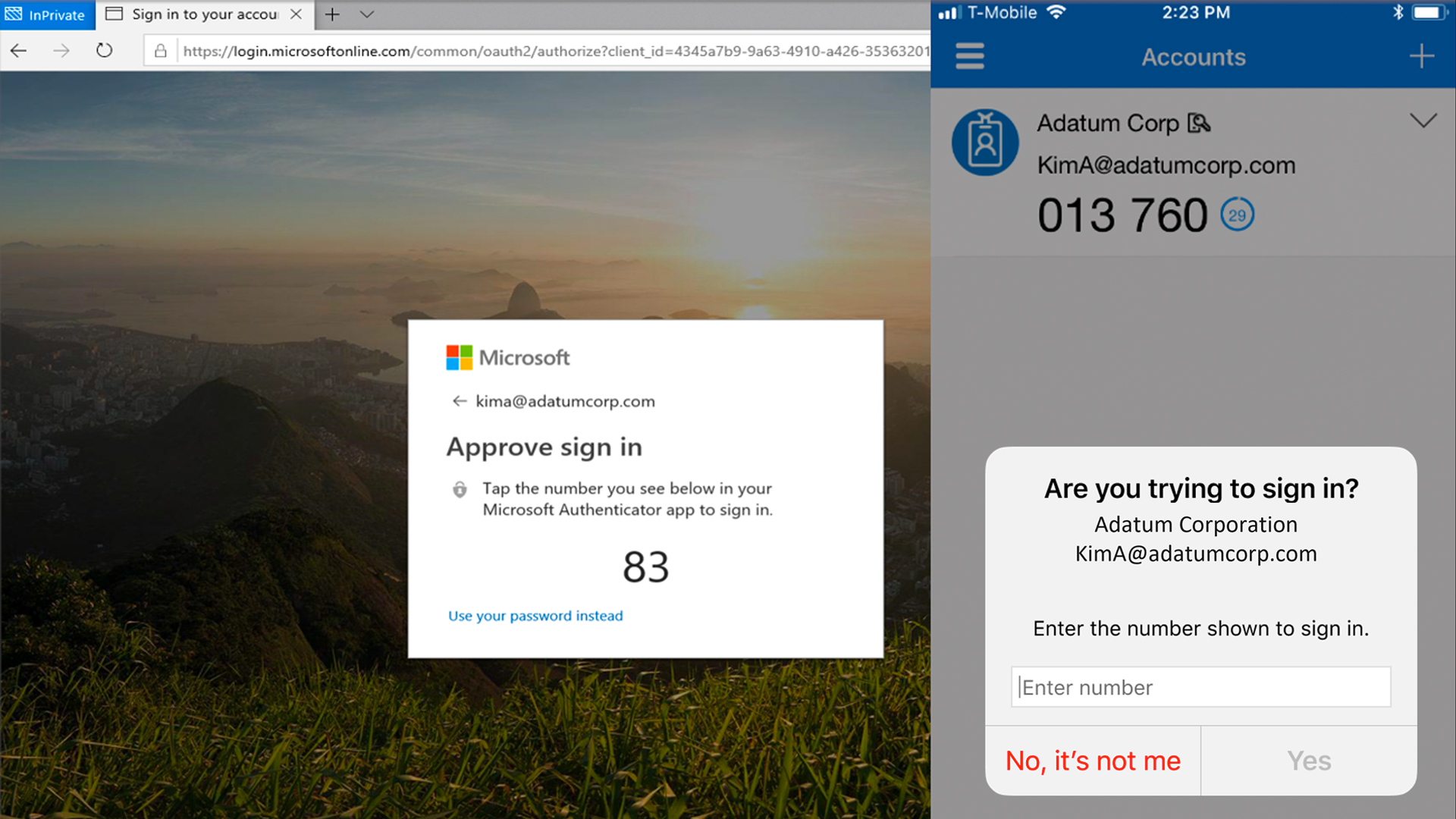
Number matching involves opening a push notification, launching Microsoft Authenticator, and entering a series of numbers that appear in the app in order to approve the login attempt.
The technique has been around for years and marries the authentication methods of MFA and two-factor authentication (2FA).
These numbers usually reset after a given time period, like 30 seconds, and add an additional layer of interaction to help reduce the risk of successful social engineering attacks.
In a typical attack scenario, recipients of the constant notifications are often asleep and wake up to a series of loud alerts from their smartphone.
Half asleep, the attack can see success when staff simply approve login attempts so they can get back to sleep, for example.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
Adding another manual layer increases the difficulty in quickly approving requests, making the process more manual and potentially allowing more time for the recipient to realize that the event is being triggered by a bad actor.
“As relevant services deploy, users worldwide who are enabled for Authenticator push notifications will begin to see number matching in their approval requests,” said Microsoft in its Active Directory (AD) documentation.
“Users can be enabled for Authenticator push notifications either in the Authentication methods policy or the legacy multifactor authentication policy if Notifications through mobile app is enabled.”
Microsoft said number matching will be applied as standard to a number of different authentication scenarios.
RELATED RESOURCE

Users attempting a self-service password reset (SSR) will also have to use MFA number matching to complete the process.
Number matching will also be enforced for combined registration in Azure AD and the AD FS adapter for Windows Server.
Microsoft clarified that users cannot opt out of number matching, but there may be some scenarios that don’t enforce it, such as in MFA Server, which is deprecated, and with old versions of Authenticator which will no longer work, requiring an update.
The AD portal may also still show the setting to enable number matching manually, but Microsoft said that you may just need to refresh the browser in order to see the update.

Connor Jones has been at the forefront of global cyber security news coverage for the past few years, breaking developments on major stories such as LockBit’s ransomware attack on Royal Mail International, and many others. He has also made sporadic appearances on the ITPro Podcast discussing topics from home desk setups all the way to hacking systems using prosthetic limbs. He has a master’s degree in Magazine Journalism from the University of Sheffield, and has previously written for the likes of Red Bull Esports and UNILAD tech during his career that started in 2015.
-
 Cohere's Aleph Alpha merger could create a transatlantic sovereign AI powerhouse
Cohere's Aleph Alpha merger could create a transatlantic sovereign AI powerhouseAnalysis The merger between Cohere and Aleph Alpha aims to capitalize on the burgeoning sovereign AI market
-
 Everything you need to know about OpenAI's new workspace agents
Everything you need to know about OpenAI's new workspace agentsNews New ‘workspace agents’ from OpenAI will automate tasks for workers and can be customized for specific roles
-
 The NCSC says it’s time to switch to passkeys
The NCSC says it’s time to switch to passkeysNews UK security organization calls for companies to step up and offer more secure ways to login
-
 AI agents are creating new identity security risks: 1Password wants to solve that
AI agents are creating new identity security risks: 1Password wants to solve thatNews The Unified Access system from 1Password will help enterprises manage AI agent access across different devices and users
-
 Using AI to generate passwords is a terrible idea, experts warn
Using AI to generate passwords is a terrible idea, experts warnNews Researchers have warned the use of AI-generated passwords puts users and businesses at risk
-
 Researchers called on LastPass, Dashlane, and Bitwarden to up defenses after severe flaws put 60 million users at risk – here’s how each company responded
Researchers called on LastPass, Dashlane, and Bitwarden to up defenses after severe flaws put 60 million users at risk – here’s how each company respondedNews Analysts at ETH Zurich called for cryptographic standard improvements after a host of password managers were found lacking
-
 Thousands of exposed civil servant passwords are up for grabs online
Thousands of exposed civil servant passwords are up for grabs onlineNews While the password security failures are concerning, they pale in comparison to other nations
-
 Gen Z has a cyber hygiene problem
Gen Z has a cyber hygiene problemNews A new survey shows Gen Z is far less concerned about cybersecurity than older generations
-
 Passwords are a problem: why device-bound passkeys can be the future of secure authentication
Passwords are a problem: why device-bound passkeys can be the future of secure authenticationIndustry insights AI-driven cyberthreats demand a passwordless future…
-
 LastPass just launched a tool to help security teams keep tabs on shadow IT risks
LastPass just launched a tool to help security teams keep tabs on shadow IT risksNews Companies need to know what apps their employees are using, so LastPass made a browser extension to help