Justice Department seizes domains used in USAID spear-phishing attacks
The APT29 hacking group is behind recent campaign


The US Department of Justice (DoJ) has confiscated two command-and-control (C2) and malware distribution domains used in a recent spear-phishing activity that imitated email communications from the US Agency for International Development (USAID). Bad actors used the domains to spread malware and access internal networks.
Microsoft was among the first to alert the public of the attacks last week. The hacking gang Nobelium, a Russian state-sponsored cybercriminal group, reportedly carried out the attacks. The gang, also known as APT29, was behind the SolarWinds attacks, the SUNBURST backdoor, TEARDROP malware, GoldMax malware, and others.
The two domains seized were theyardservice[.]com and worldhomeoutlet[.]com. The threat actors used these domains to grab data from phishing victims and send commands to malware on compromised devices.
The phishing campaign used Constant Contact's service to send malicious links obscured behind the mailing service's URL. The hackers targeted approximately 3,000 accounts across more than 150 organizations, including government organizations, non-government organizations (NGOs), think tanks, military, IT service providers, health technology and research, and telecommunications providers.
ON May 25, hackers started a wide-scale spear-phishing campaign using a compromised USAID account. Victims who clicked the links in the email were prompted to download HTML attachments.
"Upon a recipient clicking on a spear-phishing email's hyperlink, the victim computer was directed to download malware from a sub-domain of theyardservice[.]com. Using that initial foothold, the actors then downloaded the Cobalt Strike tool to maintain persistent presence and possibly deploy additional tools or malware to the victim's network," the DoJ said in a statement.
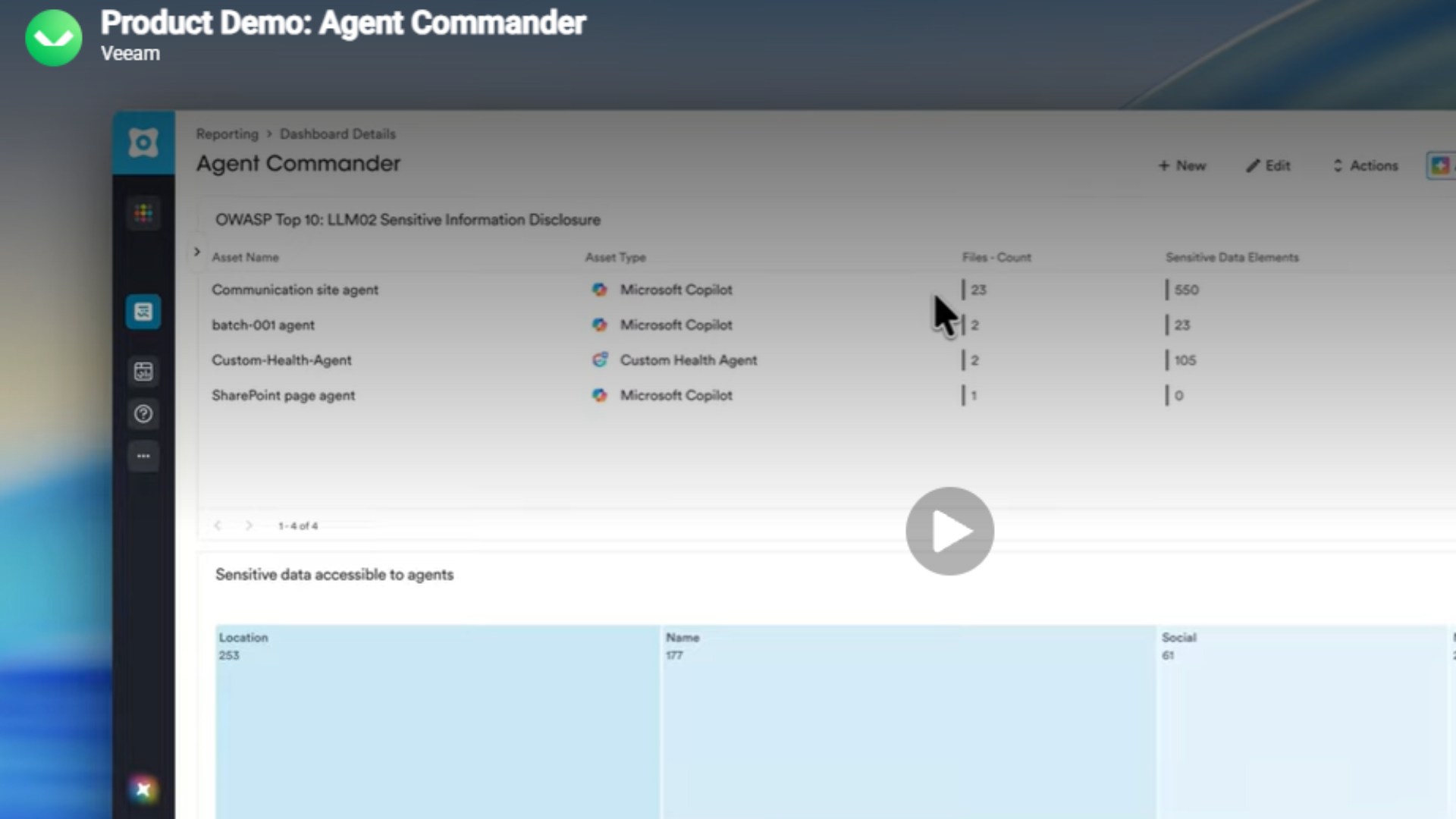
RELATED RESOURCE
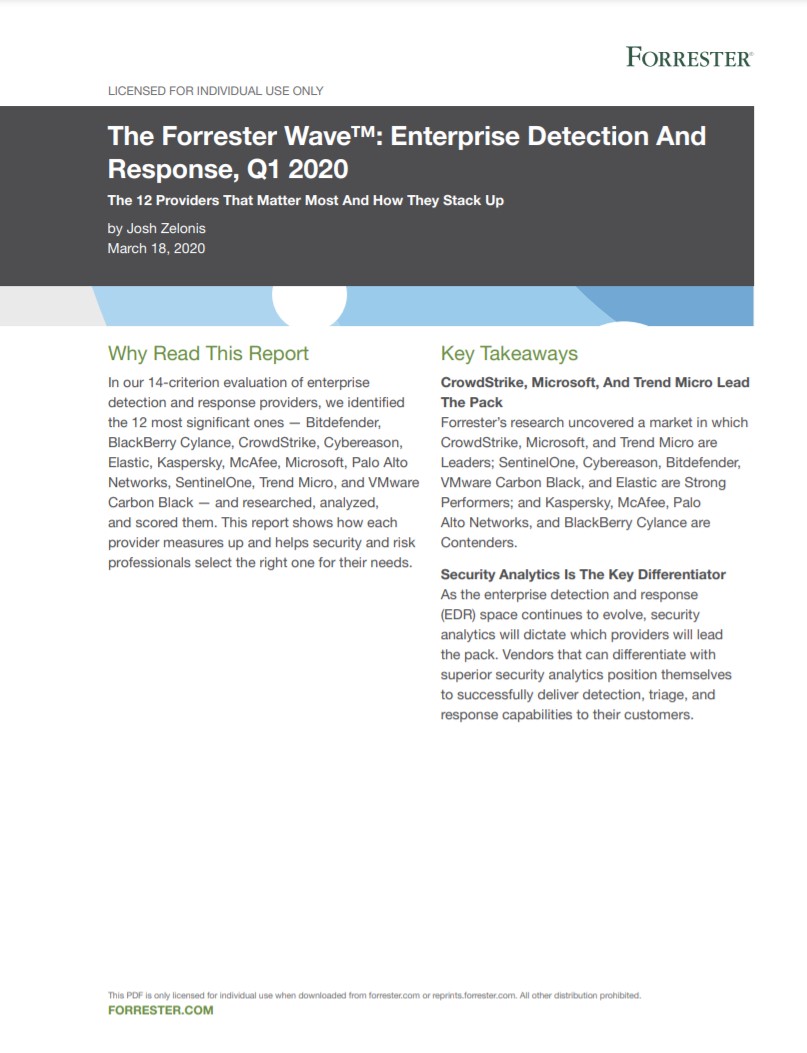
A guide to enterprise detection and response providers
The 12 providers that matter most and how they stack up
"The actors' instance of the Cobalt Strike tool received C2 communications via other subdomains of theyardservice[.]com, as well as the domain worldhomeoutlet[.]com. It was those two domains that the Department seized pursuant to the court's seizure order."
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
Assistant Director in Charge of the FBI's Washington Field Office Steven D'Antuono said the court-authorized domain seizures reflect the FBI Washington Field Office's "continued commitment to cyber victims in our region".
"These actions demonstrate our ability to quickly respond to malicious cyber activities by leveraging our unique authorities to disrupt our cyber adversaries," he added.
The DoJ said the National Security Division's Counterintelligence and Export Control Section and the United States Attorney's Office for the Eastern District of Virginia are continuing investigations with the FBI's Cyber Division and Washington Field Office.
Rene Millman is a freelance writer and broadcaster who covers cybersecurity, AI, IoT, and the cloud. He also works as a contributing analyst at GigaOm and has previously worked as an analyst for Gartner covering the infrastructure market. He has made numerous television appearances to give his views and expertise on technology trends and companies that affect and shape our lives. You can follow Rene Millman on Twitter.
-
 Salt Typhoon attack on US congressional email system ‘exposes how vulnerable core communications systems remain to nation-state actors’
Salt Typhoon attack on US congressional email system ‘exposes how vulnerable core communications systems remain to nation-state actors’News The Salt Typhoon campaign marks the latest in a string of attacks on US government communications networks
-
 ‘All US forces must now assume their networks are compromised’ after Salt Typhoon breach
‘All US forces must now assume their networks are compromised’ after Salt Typhoon breachNews The announcement marks the second major Salt Typhoon incident in the space of two years
-
 UK cyber experts on red alert after Salt Typhoon attacks on US telcos
UK cyber experts on red alert after Salt Typhoon attacks on US telcosAnalysis The UK could be next in a spate of state-sponsored attacks on telecoms infrastructure
-
 Healthcare data breaches are out of control – here's how the US plans to beef up security standards
Healthcare data breaches are out of control – here's how the US plans to beef up security standardsNews Changes to HIPAA security rules will require organizations to implement MFA, network segmentation, and more
-
 The US could be set to ban TP-Link routers
The US could be set to ban TP-Link routersNews US authorities could be lining up the largest equipment proscription since the 2019 ban on Huawei networking infrastructure
-
 US government IT contractor could face death penalty over espionage charges
US government IT contractor could face death penalty over espionage chargesNews The IT pro faces two espionage charges, each of which could lead to a death sentence or life imprisonment, prosecutors said
-
 US identifies and places $10 million bounty on LockBit, Hive ransomware kingpin
US identifies and places $10 million bounty on LockBit, Hive ransomware kingpinNews Mikhail Pavlovich Matveev was linked to specific ransomware attacks, including a 2021 raid on the DC police department
-
 Breach at US Transportation Department exposes 240,000 employee records
Breach at US Transportation Department exposes 240,000 employee recordsNews An investigation is underway into the breach, which affected former and current employee data