BRATA malware has evolved to target online banking across Europe, researchers warn
The new variant can now access SMS, GPS, and device control to better steal financial data


Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
You are now subscribed
Your newsletter sign-up was successful
An Android malware strain, known for its attacks on the Google Play store, has been spotted targeting the login pages of online banks, in what experts believe is a long-term shift in strategy by its developers.
The Brazilian Remote Access Tool (BRATA) first surfaced in 2018, targeting Android users with fake antivirus apps and similar security software in an effort to steal credentials.
RELATED RESOURCE
The Total Economic Impact™ of Mimecast
Cost savings and business benefits enabled by using Mimecast with Microsoft 365
FREE DOWNLOAD
However, new attacks suggest the group behind the malware has pivoted towards targeting financial institutions directly, attempting to put fake login pages in front of users trying to access online banking services.
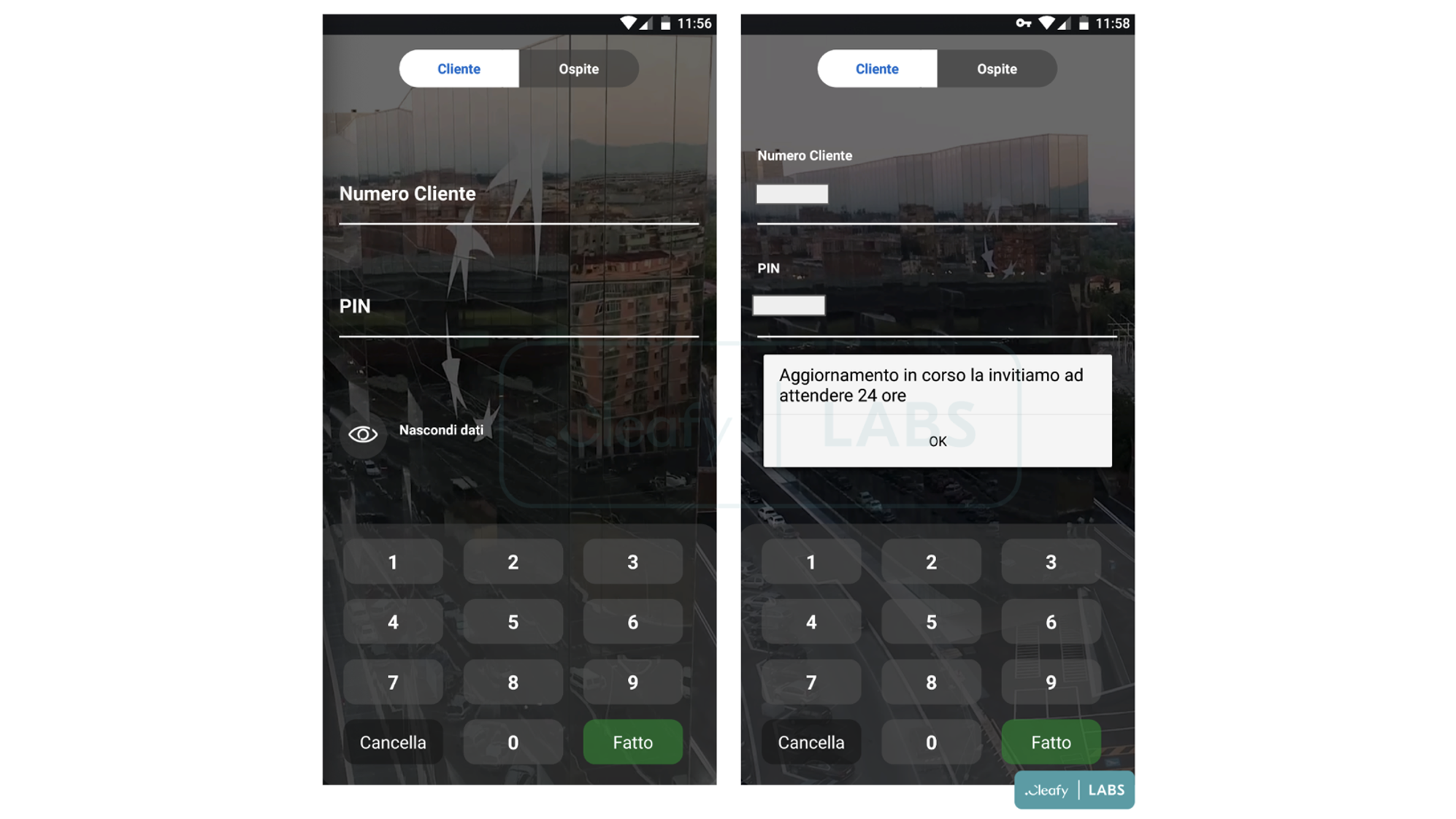
The new variant has been flagged by the cyber security organisation Cleafy, who provided screenshots of a phishing page new to BRATA that mimics the login field for a prominent bank, asking users to input their PIN and client number.
“They usually focus on delivering malicious applications targeted to a specific bank for a couple of months, and then moving to another target,” Cleafy explained in a blog post on the discovery.
Moves to socially engineer the customers of specific banks indicate that BRATA’s threat actors are curating their pool of targets. Formerly localised to South America, efforts to steal financial information have resulted in a shift in focus towards users across mainland Europe and the UK, with Italy-based Cleafy first discovering the variant through increased activity across the region.
The evolution has also seen the introduction of new features, which allow the strain to seek permissions over SMS, GPS, and device management. Additionally, on install an event-logger plugin labelled 'unrar.jar' is downloaded from the BRATA command and control (C2) infrastructure. Cleafy expressed concerns that these additions “could be used to perform a complete Account Takeover (ATO) attack”.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
At time of writing, targeted devices do not appear to be exchanging information with the threat actors behind the malware, and that this may indicate that the newest variant BRATA.A is still undergoing development, according to researchers.
However, the organisation has already identified a separate SMS stealer app connected to the BRATA C2 infrastructure, also targeting users in mainland Europe and the UK. With threat actors testing out new attack vectors linked by a common framework, there are fears that, once active, this variant could prove effective at taking over users’ financial accounts.
For this reason, Cleafy has assigned BRATA an Advanced Persistent Threat (APT) status, which they define as “an attack campaign in which criminals establish a long-term presence on a targeted network to steal sensitive information".
As malware evolves to deceive in more sophisticated ways, it is important that users keep up to date with threat prevention tactics, and only download apps from trusted sources.

Rory Bathgate is Features and Multimedia Editor at ITPro, overseeing all in-depth content and case studies. He can also be found co-hosting the ITPro Podcast with Jane McCallion, swapping a keyboard for a microphone to discuss the latest learnings with thought leaders from across the tech sector.
In his free time, Rory enjoys photography, video editing, and good science fiction. After graduating from the University of Kent with a BA in English and American Literature, Rory undertook an MA in Eighteenth-Century Studies at King’s College London. He joined ITPro in 2022 as a graduate, following four years in student journalism. You can contact Rory at rory.bathgate@futurenet.com or on LinkedIn.
-
 Microsoft and NCSC issue alerts over hacker campaigns targeting WhatsApp, Signal messaging apps
Microsoft and NCSC issue alerts over hacker campaigns targeting WhatsApp, Signal messaging appsNews Microsoft warns about a sophisticated attack that starts with WhatsApp messages, while the NCSC says such incidents are on the rise
-
 Is your new hire an AI clone? Microsoft says North Korean hackers are using AI to impersonate job seekers and steal company secrets
Is your new hire an AI clone? Microsoft says North Korean hackers are using AI to impersonate job seekers and steal company secretsNews The groups are increasingly using face-changing or voice-changing software to make their fake identities more plausible
-
 Google issues warning over ShinyHunters-branded vishing campaigns
Google issues warning over ShinyHunters-branded vishing campaignsNews Related groups are stealing data through voice phishing and fake credential harvesting websites
-
 Thousands of Microsoft Teams users are being targeted in a new phishing campaign
Thousands of Microsoft Teams users are being targeted in a new phishing campaignNews Microsoft Teams users should be on the alert, according to researchers at Check Point
-
 Microsoft warns of rising AitM phishing attacks on energy sector
Microsoft warns of rising AitM phishing attacks on energy sectorNews The campaign abused SharePoint file sharing services to deliver phishing payloads and altered inbox rules to maintain persistence
-
 Warning issued as surge in OAuth device code phishing leads to M365 account takeovers
Warning issued as surge in OAuth device code phishing leads to M365 account takeoversNews Successful attacks enable full M365 account access, opening the door to data theft, lateral movement, and persistent compromise
-
 Amazon CSO Stephen Schmidt says the company has rejected more than 1,800 fake North Korean job applicants in 18 months – but one managed to slip through the net
Amazon CSO Stephen Schmidt says the company has rejected more than 1,800 fake North Korean job applicants in 18 months – but one managed to slip through the netNews Analysis from Amazon highlights the growing scale of North Korean-backed "fake IT worker" campaigns
-
 Complacent Gen Z and Millennial workers are more likely to be duped by social engineering attacks
Complacent Gen Z and Millennial workers are more likely to be duped by social engineering attacksNews Overconfidence and a lack of security training are putting organizations at risk

