Over 300,000 Android users downloaded banking trojan malware
Hackers defeated Google Play restrictions by using smaller droppers in apps and eliminating permissions needed


Hackers have managed to bypass Google Play app restrictions to chalk up over 300,000 banking trojan infections in just four months.
According to a blog post by security researchers at Threat Fabric, hackers have avoided being detected by Google Play by using smaller droppers in apps, reducing the number of permissions being asked of users and improving code as well as creating more convincing fake websites.
This has also made them difficult to detect from an automation (sandbox) and machine learning perspective, according to Threat Fabric.
“This small footprint is a (direct) consequence of the permission restrictions enforced by Google Play,” they said.
Hackers have also started carefully planned small malicious code updates over a longer period in Google Play, as well as sporting a dropper C2 backend to fully match the theme of the dropper app. The researchers cited an example here of a working fitness website for a workout-focused app.
“To make themselves even more difficult to detect, the actors behind these dropper apps only manually activate the installation of the banking trojan on an infected device in case they desire more victims in a specific region of the world. This makes automated detection a much harder strategy to adopt by any organization,” they said.
The 300,000 dropper installations came from just four types of malware. Anatsa (200,000+ installations); Alien (95,000+ installations) and Hydra/Ermac (15,000+ installations).
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
RELATED RESOURCE

The largest, Anatsa, is an advanced Android banking trojan with RAT and semi-ATS capabilities. It carries out classic overlay attacks to steal credentials, accessibility logging (capturing everything shown on the user’s screen), and keylogging.
Researchers discovered the first dropper in June 2021 masquerading as an app for scanning documents. In total, researchers found six Anatsa droppers published in Google Play since June 2021.
A hacking group called Brunhilda dropped malware from established families, like Hydra, as well as novel ones, like Ermac. This posed as a QR code creator app. Both families have been very active in the last months according to researchers and have recently started appearing in the US.
The Alien campaign was also run by the Brunhilda group. This used a fake fitness app to spread.
“This dropper, that we dubbed “Gymdrop”, is another example of how cybercriminals try to convince victims and detection systems that their app is legitimate. The app website is designed to look legitimate at first glance. However, it is only a template for a gym website with no useful information on it, even still containing ‘Lorem Ipsum’ placeholder text in its pages,” said researchers.
Researchers said the attention dedicated by these hackers to evading unwanted attention renders automated malware detection less reliable.
Rene Millman is a freelance writer and broadcaster who covers cybersecurity, AI, IoT, and the cloud. He also works as a contributing analyst at GigaOm and has previously worked as an analyst for Gartner covering the infrastructure market. He has made numerous television appearances to give his views and expertise on technology trends and companies that affect and shape our lives. You can follow Rene Millman on Twitter.
-
 Mobile app security is a huge blind spot for developer teams – 93% are confident their applications are secure, but 62% reported breaches last year
Mobile app security is a huge blind spot for developer teams – 93% are confident their applications are secure, but 62% reported breaches last yearNews Organizations are overconfident about their mobile app security practices, according to new research, and it’s putting enterprises and consumers alike at risk.
-
 APIs: Understanding the business benefits and risks
APIs: Understanding the business benefits and riskswhitepaper What you need to know about potential data exposure from APIs
-
 Apple patches actively exploited iPhone, iPad zero-day and 18 other security flaws
Apple patches actively exploited iPhone, iPad zero-day and 18 other security flawsNews The out-of-bounds write error is the eighth actively exploited zero-day impacting Apple hardware this year and could facilitate kernel-level code execution
-
 Qualcomm and Mediatek flaws left millions of Android users at risk
Qualcomm and Mediatek flaws left millions of Android users at riskNews An open source audio codec used by chipset firms is believed to have put two-thirds of Android users' private calls and files at risk
-
 Businesses on alert as mobile malware surges 500%
Businesses on alert as mobile malware surges 500%News Researchers say hackers are deploying new tactics that put Android and iOS at equal risk
-
 Apple fixes array of iOS, macOS zero-days and code execution security flaws
Apple fixes array of iOS, macOS zero-days and code execution security flawsNews The first wave of security updates for Apple products in 2022 follows a year in which a wide variety of security flaws plagued its portfolio of devices
-
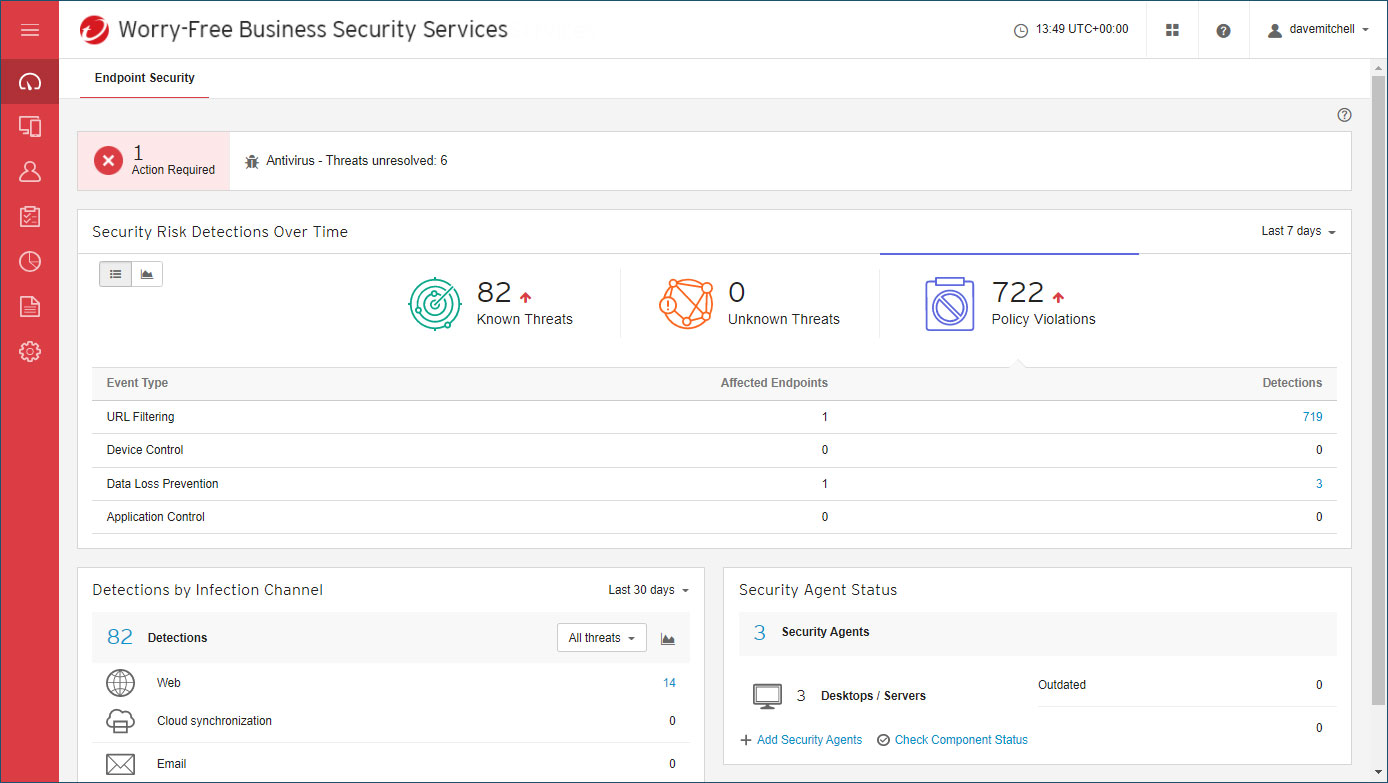 Trend Micro Worry-Free Business Security review: Great cloud-managed malware protection
Trend Micro Worry-Free Business Security review: Great cloud-managed malware protectionReviews A reassuringly simple endpoint-protection solution – although mobile support is basic
-
 Flaw in Android phones could let attackers eavesdrop on calls
Flaw in Android phones could let attackers eavesdrop on callsNews The vulnerable chips are thought to be present in 37% of all smartphones worldwide



