Microsoft releases Fusion ransomware detection tool for Azure
Fusion Detection for Ransomware uses machine learning to spot malicious activity across a user's network


Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
You are now subscribed
Your newsletter sign-up was successful
Microsoft has released a new ransomware detection feature for Azure that uses machine learning to spot potential attacks.
'Fusion Detection for Ransomware' will send an alert to customers when it observes actions that are "potentially associated with ransomware activities".
The alerts will inform users of what was detected, and on which device, with the system correlating data from other Azure services, such as Azure Defender, Microsoft Defender for Endpoint, Microsoft Defender for Identity, Microsoft Cloud App Security, and Azure Sentinel scheduled analytics rules.
Once ransomware activities are detected and correlated by the Fusion's machine learning model, a high severity incident with the label "Multiple alerts possibly related to Ransomware activity detected" will be triggered in the customer's Azure Sentinel workspace (shown in the image below).
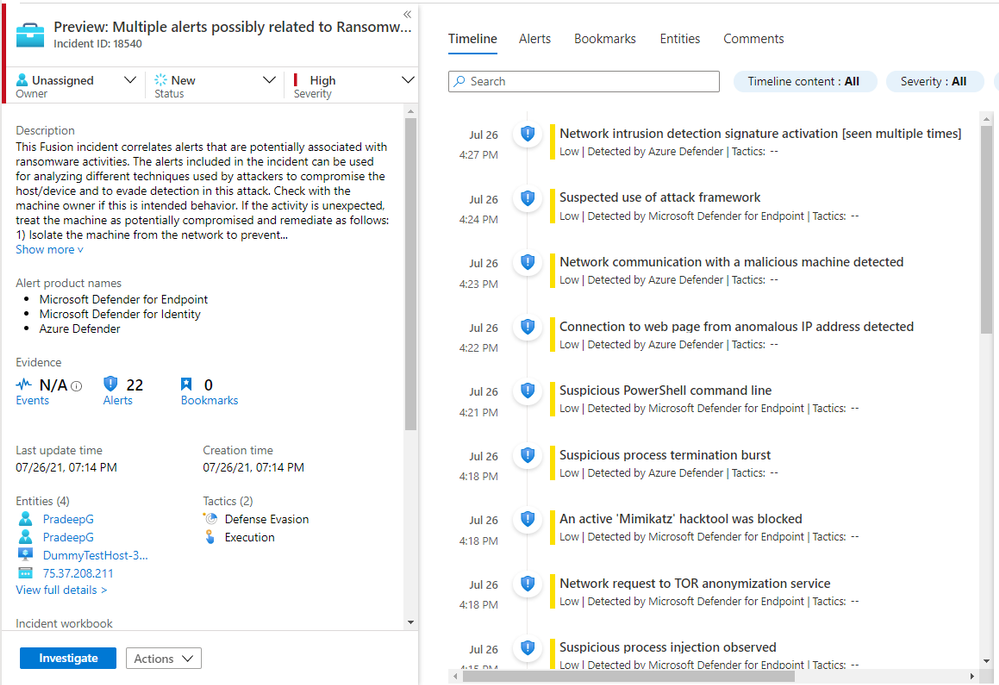
After an alert has been sent, Microsoft recommends users check the device/host in question to see if its behaviour is "unexpected". If so, the user should treat the machine as "potentially compromised" and take immediate actions, such as isolating the machine from the network, running full anti-virus scans, and investigating the rest of the network for similar signs.
Ransomware has become a lucrative occupation, according to a recent report from Unit 42, with average payouts almost doubling over the past year. Since 2020, payouts for successful ransomware attacks have increased 82% to a record $570,000 in the first half of 2021. The increase followed the previous year's 171% jump to more than $312,000.
"Preventing such attacks in the first place would be the ideal solution but with the new trend of 'ransomware as a service' and human operated ransomware, the scope and the sophistication of attacks are increasing - attackers are using slow and stealth techniques to compromise network, which makes it harder to detect them in the first place," Microsoft security researcher Sylvie Liu wrote in a blog post.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
Bobby Hellard is ITPro's Reviews Editor and has worked on CloudPro and ChannelPro since 2018. In his time at ITPro, Bobby has covered stories for all the major technology companies, such as Apple, Microsoft, Amazon and Facebook, and regularly attends industry-leading events such as AWS Re:Invent and Google Cloud Next.
Bobby mainly covers hardware reviews, but you will also recognize him as the face of many of our video reviews of laptops and smartphones.
-
 Security leaders overconfident about ransomware recovery
Security leaders overconfident about ransomware recoveryNews Few manage to recover all their data, and many experience business disruption
-
 German authorities want your help finding the hackers behind GandCrab and REvil
German authorities want your help finding the hackers behind GandCrab and REvilNews Daniil Maksimovich Shchukin and Anatoly Sergeevitsch Kravchuk are believed to have made millions from ransomware as a service schemes
-
 The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in life
The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in lifeNews With family responsibilities and mortgages to pay, it's not teenagers dishing out malware or carrying out cyber extortion
-
 Ransomware gangs are using employee monitoring software as a springboard for cyber attacks
Ransomware gangs are using employee monitoring software as a springboard for cyber attacksNews Two attempted attacks aimed to exploit Net Monitor for Employees Professional and SimpleHelp
-
 Microsoft patches six zero-days targeting Windows, Word, and more – here’s what you need to know
Microsoft patches six zero-days targeting Windows, Word, and more – here’s what you need to knowNews Patch Tuesday update targets large number of vulnerabilities already being used by attackers
-
 Ransomware gangs are sharing virtual machines to wage cyber attacks on the cheap – but it could be their undoing
Ransomware gangs are sharing virtual machines to wage cyber attacks on the cheap – but it could be their undoingNews Thousands of attacker servers all had the same autogenerated Windows hostnames, according to Sophos
-
 Google issues warning over ShinyHunters-branded vishing campaigns
Google issues warning over ShinyHunters-branded vishing campaignsNews Related groups are stealing data through voice phishing and fake credential harvesting websites
-
 The FBI has seized the RAMP hacking forum, but will the takedown stick? History tells us otherwise
The FBI has seized the RAMP hacking forum, but will the takedown stick? History tells us otherwiseNews Billing itself as the “only place ransomware allowed", RAMP catered mainly for Russian-speaking cyber criminals


