Only a third of businesses have taken out insurance against ransomware attacks
Almost one in six also reported having no disaster recovery plan in place


Only a third (35.8%) of businesses have insurance cover for ransomware attacks, despite it being one of the most common forms of cyber threat.
That's according to a survey of more than 820 organisations by Hornetsecurity, which shared the findings exclusively with IT Pro.
The findings show that one in five (21.1%) had fallen victim to a ransomware attack, while almost one in 10 (9.2%) were forced to pay the ransom to recover data after an attack. This comes just weeks after a Unit 42 report found that ransomware payments had increased 82% since 2020 to a record $570,000 in the first half of 2021.
Hornetsecurity's report also revealed that of those reporting ransomware, just under 12% of respondents were able to recover data through backups, although some data was still lost during this process. The report added that the rise in prevalence of ransomware has prompted 71.3% of organisations to reconsider the ways they back up their data.
The two most common forms of prevention were end-point detection software with anti-ransomware capabilities (75.6%), and email filtration and threat analysis (76.1%). However, it also found a comparably low uptake (47.8%) in the use of air-gapped, offsite storage, which is highly effective in recovering data.
Despite the rising threat of ransomware, Hornetsecurity found that education on how to prevent ransomware attacks can be lacking, and employees often believe in cyber security myths. More than a quarter (28.7%) of surveyed organisations do not provide training to end-users on how to recognise and handle potential ransomware threats, despite them being the easiest targets of social engineering techniques such as phishing.
RELATED RESOURCE

The best defence against ransomware
How ransomware is evolving and how to defend against it
Another 22.2% of those surveyed believe that Microsoft 365 data is immune to ransomware attacks, or stated that they don’t know whether it can be affected. This view can be dangerous for businesses: although notably secure, Microsoft 365 can fall victim to ransomware through malicious attachments sent via email or a potential system vulnerability.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
Almost one in six (15.9%) of respondents also reported having no disaster recovery plan in place, making them unprepared to deal with a potential ransomware attack.
Hornetsecurity’s findings come days after CISA, the FBI, and the National Security Agency (NSA) released a joint Cybersecurity Advisory (CSA) warning organisations of increased threat of Conti attacks.
Having only graduated from City University in 2019, Sabina has already demonstrated her abilities as a keen writer and effective journalist. Currently a content writer for Drapers, Sabina spent a number of years writing for ITPro, specialising in networking and telecommunications, as well as charting the efforts of technology companies to improve their inclusion and diversity strategies, a topic close to her heart.
Sabina has also held a number of editorial roles at Harper's Bazaar, Cube Collective, and HighClouds.
-
 Integris makes first international move with Australian MSP acquisition
Integris makes first international move with Australian MSP acquisitionNews The provider’s first international acquisition will extend its reach across APAC.
-
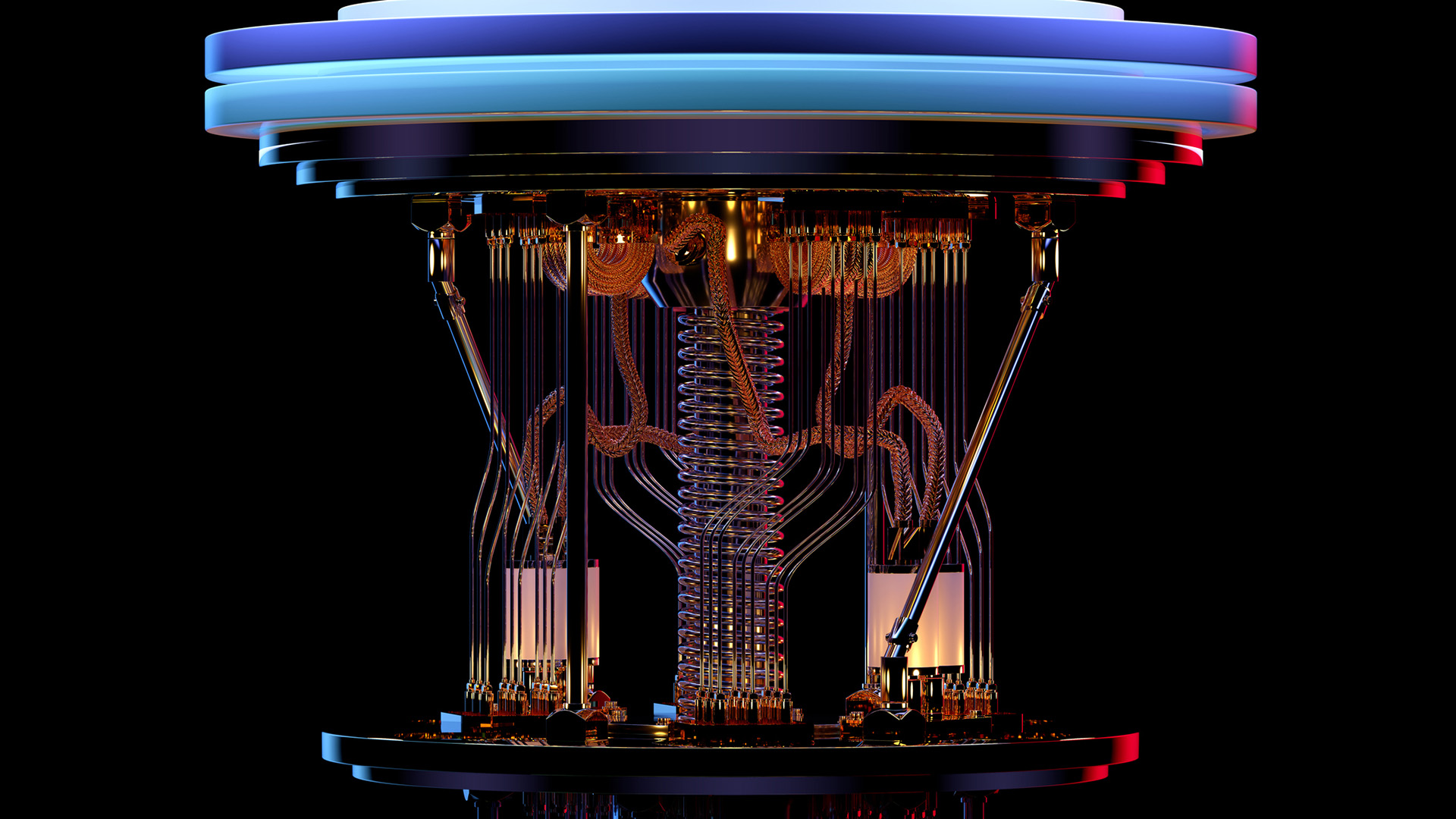 Bell Labs’ Michael Eggleston on Nokia’s research into topological quantum computing
Bell Labs’ Michael Eggleston on Nokia’s research into topological quantum computingInterview Bell Labs is known for developing radio astronomy technology, transistors and lasers – now owned by Nokia, its research is focusing on quantum computing
-
 Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitation
Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitationNews A dip in ransomware volumes points to a more targeted approach focused on vulnerability exploitation
-
 Security leaders overconfident about ransomware recovery
Security leaders overconfident about ransomware recoveryNews Few manage to recover all their data, and many experience business disruption
-
 German authorities want your help finding the hackers behind GandCrab and REvil
German authorities want your help finding the hackers behind GandCrab and REvilNews Daniil Maksimovich Shchukin and Anatoly Sergeevitsch Kravchuk are believed to have made millions from ransomware as a service schemes
-
 The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in life
The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in lifeNews With family responsibilities and mortgages to pay, it's not teenagers dishing out malware or carrying out cyber extortion
-
 Ransomware gangs are using employee monitoring software as a springboard for cyber attacks
Ransomware gangs are using employee monitoring software as a springboard for cyber attacksNews Two attempted attacks aimed to exploit Net Monitor for Employees Professional and SimpleHelp
-
 Ransomware gangs are sharing virtual machines to wage cyber attacks on the cheap – but it could be their undoing
Ransomware gangs are sharing virtual machines to wage cyber attacks on the cheap – but it could be their undoingNews Thousands of attacker servers all had the same autogenerated Windows hostnames, according to Sophos
-
 Google issues warning over ShinyHunters-branded vishing campaigns
Google issues warning over ShinyHunters-branded vishing campaignsNews Related groups are stealing data through voice phishing and fake credential harvesting websites
-
 The FBI has seized the RAMP hacking forum, but will the takedown stick? History tells us otherwise
The FBI has seized the RAMP hacking forum, but will the takedown stick? History tells us otherwiseNews Billing itself as the “only place ransomware allowed", RAMP catered mainly for Russian-speaking cyber criminals
