Crypto-mining hackers hit Kubernetes clusters
New campaign abused Kubeflow dashboards to install malicious containers

Security researchers have warned of hackers' continued attacks against Kubernetes clusters running Kubeflow machine learning (ML) instances by installing malicious containers that mine cryptocurrencies, such as Monero and Ethereum.
According to Microsoft Senior Security Researcher Yossi Weizman, the attacks began at the end of last month as he and his team discovered a spike in TensorFlow machine learning pod deployments. An investigation of the entry point of the pods revealed deployment aimed to mine cryptocurrency.
"The burst of deployments on the various clusters was simultaneous. This indicates that the attackers scanned those clusters in advance and maintained a list of potential targets, which were later attacked at the same time," said Weizman.
The hackers used two images in the attack. The first was the latest version of TensorFlow (tensorflow/tensorflow:latest), and the second was the latest version with GPU support (tensorflow/tensorflow:latest-gpu).
The images were legitimate but ran malicious crypto-mining code. The attackers abused the access to the Kubeflow centralized dashboard to create a new pipeline. Kubeflow Pipelines is a platform for deploying ML pipelines based on Argo Workflow. These dashboards were exposed to the internet instead of being only open to local access.
Hackers deployed at least two pods on each cluster: one for CPU mining, and the other for GPU mining. Both containers used open-source miners from GitHub: Ethminer in the case of the GPU container and XMRIG in the CPU one.
RELATED RESOURCE
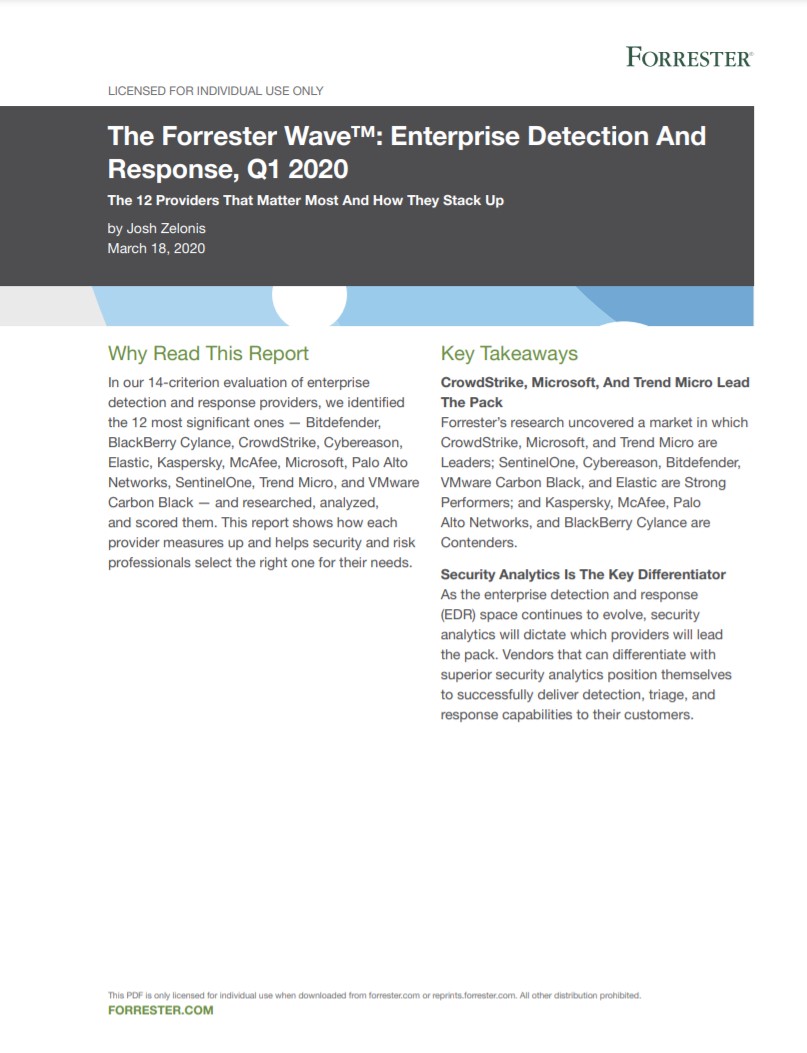
A guide to enterprise detection and response providers
The 12 providers that matter most and how they stack up
The malicious pods all had the same pattern of name; "sequential-pipeline-{random pattern}."
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
Weizman said that as part of the attack, hackers deployed a reconnaissance container that queries information about the environment, such as GPU and CPU information, as preparation for the mining activity. This also ran from a TensorFlow container.
"The attack is still active, and new Kubernetes clusters that run Kubeflow get compromised," Weizman added.
The campaign is similar to one staged in April last year. This also abused Kubernetes clusters in a crypto-mining campaign. However, instead of using Kubeflow Pipelines to deploy ML pipelines, it used a Jupyter notebook server. This campaign was the first that Microsoft observed targeting Kubeflow environments.
Weizman said that organizations running Kubeflow should ensure that the centralized dashboard isn't insecurely exposed to the internet. If Kubeflow should be exposed to the internet, make sure you use authentication. Administrators should also search containers that run TensorFlow images and inspect the entry point of those containers.
Rene Millman is a freelance writer and broadcaster who covers cybersecurity, AI, IoT, and the cloud. He also works as a contributing analyst at GigaOm and has previously worked as an analyst for Gartner covering the infrastructure market. He has made numerous television appearances to give his views and expertise on technology trends and companies that affect and shape our lives. You can follow Rene Millman on Twitter.
-
 Liquid cryptocurrency exchange loses $97 million after hack
Liquid cryptocurrency exchange loses $97 million after hackNews Amount lost includes $45 million in Ethereum tokens
-
 False crypto-mining apps plague Google Play
False crypto-mining apps plague Google PlayNews Apps deceive users into clicking on ads or buying non-existent mining subscriptions
-
 Ohio resident pleads guilty to running Bitcoin “mixer” money laundering scheme
Ohio resident pleads guilty to running Bitcoin “mixer” money laundering schemeNews More than $300 million went through Darknet-based bitcoin hashing (BTC) service
-
 Study: Cryptocurrency value spikes encourage more illicit mining
Study: Cryptocurrency value spikes encourage more illicit miningNews Researchers tracked Modero cryptocurrency and illicit mining for nearly three years
-
 FTC warns of rising cryptocurrency fraud
FTC warns of rising cryptocurrency fraudNews Marked rise in cryptocurrency losses began just as pandemic took hold
-
 Encrypted messaging site Privnote cloned to steal Bitcoin
Encrypted messaging site Privnote cloned to steal BitcoinNews Criminals aim to redirect users’ Bitcoins using a phishing scam
-
 US identifies and charges SamSam ransomware authors
US identifies and charges SamSam ransomware authorsNews In a wave of attacks spanning three years, the US government has charged the people behind it, but getting them in handcuffs won't be easy
-
 Hackers are increasingly exploiting cryptojacking malware without needing active browsers
Hackers are increasingly exploiting cryptojacking malware without needing active browsersNews Crypto malware is quickly extending to non-browser applications, says Checkpoint