What is cloud ransomware and how can you avoid attacks?
With cloud ransomware increasingly targeting applications and data, as well as cloud-based companies, we explain how you can protect your business


In recent years, cloud ransomware has grown to become one of the most pervasive threats faced by organisations across a range of industries. This surge, combined with the widespread shift to cloud computing, has presented a dual challenge for businesses.
Harnessing the power of cloud computing is no longer the daunting task that it used to be, and the COVID-19 pandemic undoubtedly has accelerated the shift to cloud, with many organisations now running at least part of their operations on public cloud services.
However, hackers are now taking advantage of this shift, targeting a new security posture that many businesses will be unfamiliar with. Serious incidents are still far rarer on cloud infrastructure, as most ransomware payloads have been configured to operate on isolated computers, but experts have warned hackers are not far behind.
There are very few, if any, hacker groups solely targeting cloud infrastructure, according to security firm Uni42. However, that doesn't mean the threat of disruption is low. There are plenty of cases of major cloud providers being targeted by ransomware directly, which can be catastrophic for customers.
Cloudstar’s incident in July 2022 is a prime example of that and should serve as a warning for organisations. Similarly, malware gangs such as TeamTNT have been observed targeting Kubernetes in the past.
It's critical for IT decision-makers to have a full understanding of their company's weak points, and what high-value data may be at risk if a cloud-based vulnerability is exploited. Customer information, business-critical data, and key processes are all attractive targets for cyber criminals, and so spending time to get ahead of the attackers could be hugely significant for business continuity and reputation in the long term.
What is cloud ransomware and how does it work?
There are multiple ways cyber criminals can obtain access to cloud-based resources and data, says Gavin Knapp, cyber defence technical lead at Bridewell Consulting. They can target vulnerabilities in cloud services to gain an initial foothold, or web applications to deploy web shells and malware.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
A cloud ransomware attack happens when hackers are able to compromise weak access controls on internet-facing services before propagating ransomware to an internal infrastructure as a service (IaaS) environment.
Knapp cites the example of the zero-day vulnerability found in Apache Log4j. “It took little time for bad actors to exploit payloads to include ransomware,” he says. “The threat was exacerbated by the widespread public sharing of the exploit code, Log4Shell.”
Cloud ransomware attacks can make use of a variety of techniques, including stealing user credentials. These can then be used to gain access to cloud consoles and OAuth app consent, or launch phishing or other identity-based cyber attacks.
In fact, attacks can often occur when hackers successfully bypass poorly configured cloud API services, or obtain access to accidentally shared credentials.
RELATED RESOURCE
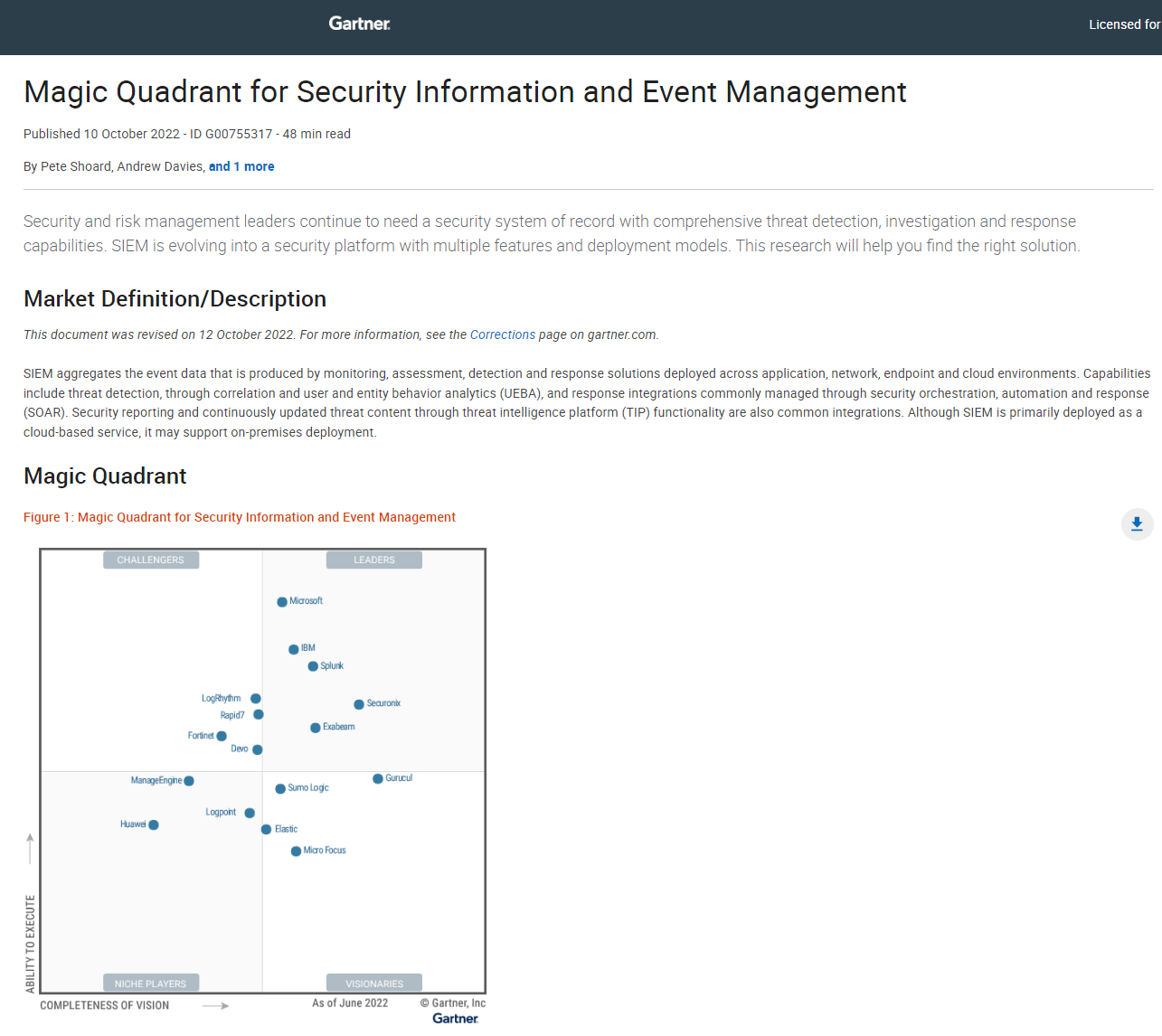
2022 Magic quadrant for Security Information and Event Management (SIEM)
SIEM is evolving into a security platform with multiple features and deployment models
“Attackers can go through services such as GitHub and search for cloud access keys that have been incorrectly posted to public repositories,” says Rob Demain, CEO of security firm e2e-assure. “Hackers simply pull out the authentication keys written in the code.”
Malware authors and criminal groups operate like any modern business and are transforming their own tactics and techniques to include cloud, warns Knapp. “The automation of cloud attacks is also growing and the time between vulnerability releases and weaponization of malware including ransomware is getting shorter.”
The cloud ransomware business model is becoming increasingly ‘professionalised’, with cyber criminals hiring dedicated malware developers as an efficient and cost-effective way of carrying out operations, says Deloitte cyber risk partner, Nick O’Kelly.
“These developers typically advertise through cyber criminal marketplaces, and their services can range from initial ’dropper’ malware that exploits specific vulnerabilities, to bespoke ransomware designed to the clients’ needs and victim specification – such as cloud infrastructure.”
This is already starting to happen, at least in theory. Security firm KnowBe4 posted a blog in January about a white hat hacker who developed a working RansomCloud strain that encrypts cloud email accounts, including Microsoft Office 365 accounts, in real-time.
Any business using the cloud is at risk, but those lacking maturity in architecting secure cloud services are “particularly vulnerable”, as well as businesses lacking security controls to prevent users from granting permissions to applications, warns Knapp. Organisations that fail to understand the so-called shared security responsibility model – which means the business and cloud provider are jointly responsible for security – are also at risk.
How to defend a business against cloud ransomware
As the volume and scale of ransomware attacks increases, there are no concrete guarantees that you won't be hit by strains specifically targeting the cloud. However, your business can take several steps to avoid it.
1. Maintain an effective backup strategy
Backups are critical in this context, and testing your defences is key. Regular assessments and checks should be conducted to examine your organisation's resilience to ransomware attacks, says Phil Robinson, principal consultant and founder of cyber security consultancy, Prim Infosec.
This should include looking at the data held in cloud services and establishing whether it can be recovered if it’s deleted or encrypted. Robinson, in particular, urges businesses to examine whether data is being versioned, snapshotted or backed up to another platform, how frequently this is happening, and when the last time a simulated loss and restore was tested.
Don’t assume that because your organisation is using a cloud-based service provided by a key player such as Microsoft, Amazon, or Google, it means data is safe, says Robinson. “In particular, the use of IaaS will more than likely mean it’s your own responsibility to ensure you’re resilient against these types of attacks.”
Even platform as a service (PaaS) or software as a service (SaaS) doesn’t provide automatic protection, Robinson warns. “Microsoft Onedrive and Sharepoint have a level of ransomware protection via the Versioning feature. This, however, might not be enabled by your organisation, or an attacker who has gained administrative privileges may be able to disable it.”
2. Invest in cyber security tools
While maintaining stringent security hygiene processes, such as multifactor authentication (MFA) and regular patching, technical solutions can play a key role in mitigating potential threats. Businesses are advised to implement robust endpoint, email, and cloud app detection and response capabilities.
Long-term, this will enable cloud developers and engineers to avoid falling prey to social engineering tactics, Knapp says. All alerts should be sent to either a security information and event management (SIEM) or security orchestration, automation, and response (SOAR) system. This will ensure 24/7 monitoring of potential threats, he adds.
Threat intelligence services also prove highly beneficial in providing early warnings of an attack and help organisations to adjust their security posture accordingly.
3. Educate your employees
Education, in addition, is the key to mitigating the cloud ransomware threat, says Knapp.
“IT, security and end-users must be made aware of how cloud-focused attacks are performed, what can be done to protect against them, and how to report an incident when needed.”
This is particularly important for those employees that are not normally exposed to a company's cyber security posture, and may lack the necessary skills the identify threats or report incidents should they occur. Beyond corporate policies about the correct use of work devices, regular cyber security awareness training can be useful for keeping employees up to date with the latest threats, whether that's simply how to spot a phishing email or a detailed look at some of the cutting-edge trends across the cyber security landscape.
It's also critical that your business has an effective process for reporting suspicious activity. It should be clear to employees who they should turn to if they suspect their account or information has been compromised, and the actions they may need to take if a cloud ransomware attack is underway.
This article was first published on 25/03/2022 and has since been updated.
Kate O'Flaherty is a freelance journalist with well over a decade's experience covering cyber security and privacy for publications including Wired, Forbes, the Guardian, the Observer, Infosecurity Magazine and the Times. Within cyber security and privacy, her specialist areas include critical national infrastructure security, cyber warfare, application security and regulation in the UK and the US amid increasing data collection by big tech firms such as Facebook and Google. You can follow Kate on Twitter.
-
 ‘Perfect’ Zero Trust is killing your mid-market productivity
‘Perfect’ Zero Trust is killing your mid-market productivitySponsored Security theory often collapses under real-world deadlines. It’s time for a more auditable, “human-centric” approach to privileged access management
-
 Increased AI use means developers spend more time reviewing code than ever
Increased AI use means developers spend more time reviewing code than everNews While AI is improving productivity and efficiency, many developers are caught up in a vicious cycle of code reviews and bug hunting
-
 Instructure chose to a pay ransom following the Canvas cyber attack – research shows more than half of security leaders would follow suit
Instructure chose to a pay ransom following the Canvas cyber attack – research shows more than half of security leaders would follow suitAnalysis Opting to pay ransoms creates huge risks for enterprises – you’re relying on the word of criminals
-
 Ransomware negotiator sentenced for role in major cyber crime group
Ransomware negotiator sentenced for role in major cyber crime groupNews Deniss Zolotarjovs was a key player in a group associated with Conti
-
 Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitation
Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitationNews A dip in ransomware volumes points to a more targeted approach focused on vulnerability exploitation
-
 Security leaders overconfident about ransomware recovery
Security leaders overconfident about ransomware recoveryNews Few manage to recover all their data, and many experience business disruption
-
 German authorities want your help finding the hackers behind GandCrab and REvil
German authorities want your help finding the hackers behind GandCrab and REvilNews Daniil Maksimovich Shchukin and Anatoly Sergeevitsch Kravchuk are believed to have made millions from ransomware as a service schemes
-
 The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in life
The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in lifeNews With family responsibilities and mortgages to pay, it's not teenagers dishing out malware or carrying out cyber extortion
-
 Ransomware gangs are using employee monitoring software as a springboard for cyber attacks
Ransomware gangs are using employee monitoring software as a springboard for cyber attacksNews Two attempted attacks aimed to exploit Net Monitor for Employees Professional and SimpleHelp
-
 Ransomware gangs are sharing virtual machines to wage cyber attacks on the cheap – but it could be their undoing
Ransomware gangs are sharing virtual machines to wage cyber attacks on the cheap – but it could be their undoingNews Thousands of attacker servers all had the same autogenerated Windows hostnames, according to Sophos

