Mastering endpoint security implementation
More devices connecting to the corporate network means more security risks. Here are some of the ways to protect your business

The amount of flexibility we have in our working lives is one of the best things about the business world today for many people. Thanks to mobile devices like smartphones, tablets, and laptops, we can carry out our duties more or less anywhere with a connection to the internet. We can even have a better work-life balance, since we can choose to work the hours that suit us.
Similarly, the the Internet of Things (IoT) is bringing in a variety of small devices and sensors that can aid organisations with core aspects of their business like productivity monitoring, increased automation, and preventative maintenance.
RELATED RESOURCE
However, each one of these endpoints represents a potential security threat to the business.
55% of vulnerable endpoints contain sensitive or confidential data, according to The Cost of Insecure Endpoints report from the Ponemon Institute. If these endpoints are stolen, lost or accessed by a malicious actor – through spyware, for example – this data is at risk. A compromised endpoint may even allow a bad actor access to the information stored on it, or information that has passed through it, and it also provides an opportunity for this kind of individual to infiltrate the corporate network itself.
IT has had to turn its attention, therefore, to putting the right endpoint and data security solutions in place, as well as network security to maintain the safety of a business’s data.
What is endpoint security?
Protecting individual user devices that connect to a corporate network, and the confidential data they hold, is a practice known as endpoint security. Usually, this is implemented through the use of a centrally managed software that communicates with client software installed on each device.
Like any other security policy, endpoint security protects against existing and emerging threats to software, although devices tend to be targeted most often by the likes of trojans, which are designed to spread the reach of botnets, or occasionally ransomware.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
Given that endpoint security is often offered as part of a software package, capabilities can differ depending on the provider. Most basic suites will offer antivirus protection, anti-spyware functions, firewalls, and host intrusion prevention systems (HIPS). You might also find data loss prevention, email encryption, network access control, endpoint detection, and application whitelisting services offered as part of the package, although the way these are deployed might vary and not all of them will be discrete options.
Endpoint security implementation best practices

What configuration of endpoint security services will be most effective will depend on the business you’re in. For example, a business that operates a bring your own device (BYOD) policy, or has a large number of IoT sensors deployed across a manufacturing line, will have notably different security needs over a business that runs a single traditional office environment.
However, there are some basic principles that every business will need to follow if they hope to get the most from endpoint security.
Know the risks
When planning this kind of security strategy, it's important to know what your endpoint landscape looks like. This can include a survey of your IT estate (company-issued laptops, PCs and smartphones, for example) as well as an audit of what personal devices access corporate data and which users they belong to.
It's also important to understand what data is passing through your endpoints. This can help establish an access management policy not just by the user but by the endpoint, which can help catch security threats early through behavioural analysis.
It's also worth keeping in mind any regulations in your industry, such as GDPR, that could dictate who is able to access what data.
Deploy endpoint protection
Antivirus on the endpoint is not enough nowadays. Endpoint security needs to cover as many threats as possible, so protection software needs to offer malware protection, application whitelisting, access control and so on.
Sometimes, one endpoint protection suite isn't enough. You may find that it's better for you to add dedicated antimalware, plus a separate access control or containerisation system, plus a level of artificial intelligence or machine learning to help detect divergence in normal behaviour or unknown devices trying to connect. However, bear in mind you will also need to manage all these setups, so a single solution that fits your needs as closely as possible may be more practical.
Amid all this focus on endpoints, it's also important not to forget the network perimeter. Corporate firewalls, data encryption and segregation are all still vital components of any security strategy.
Endpoint security in 2022

How businesses manage endpoint security has come under increased scrutiny since the mass move to remote work.
Although not an entirely new concept, many businesses have been forced to introduce brand new policies to cope with the sheer number of employees working away from the office. Although the mandatory work from home orders are no longer in force, businesses have been slow to move back to the old ways. In fact, only a third of companies plan to introduce a full return to the office, and those that have tried to revert back have been met with resistance from those employees who have demonstrated that you don't need an office to stay productive, or secure.
What's largely emerged from the pandemic is a hybrid model of working, embracing the fact that employees are going to be remote at least half of the time. One prominent example of this is Salesforce, which revealed in 2021 that employees would have the choice of three different working models, provided they have proof of vaccination; namely fully office-based at its San Francisco site, fully remote, or a combination of the two. Prior to the pandemic, just 18% of staff were deemed remote workers. Today, most Salesforce workers are either hybrid or fully remote.
This arrangement, while beneficial for employee wellbeing, raises legitimate questions about endpoint security. Combining remote working with in-office might prove troublesome to oversee from a security standpoint, particularly if there's no formal BYOD policy in place, or there's a blurring of the lines between what is a home device and a work device even if it's company provisioned.
IT teams will have to be mindful of what kind of devices staff are using, as well as the software they're installing – this may force some businesses to roll out fairly restrictive policies.
-
 Kaseya shifts from AI ‘insights’ to autonomous action with new agentic platform
Kaseya shifts from AI ‘insights’ to autonomous action with new agentic platformNews The company aims to evolve from its suite of management tools into an autonomous operating system for MSPs
-
 Accenture to roll-out Copilot to 700,000+ staff
Accenture to roll-out Copilot to 700,000+ staffNews Accenture will roll out Microsoft Copilot to nearly three quarters of a million employees after years of testing
-
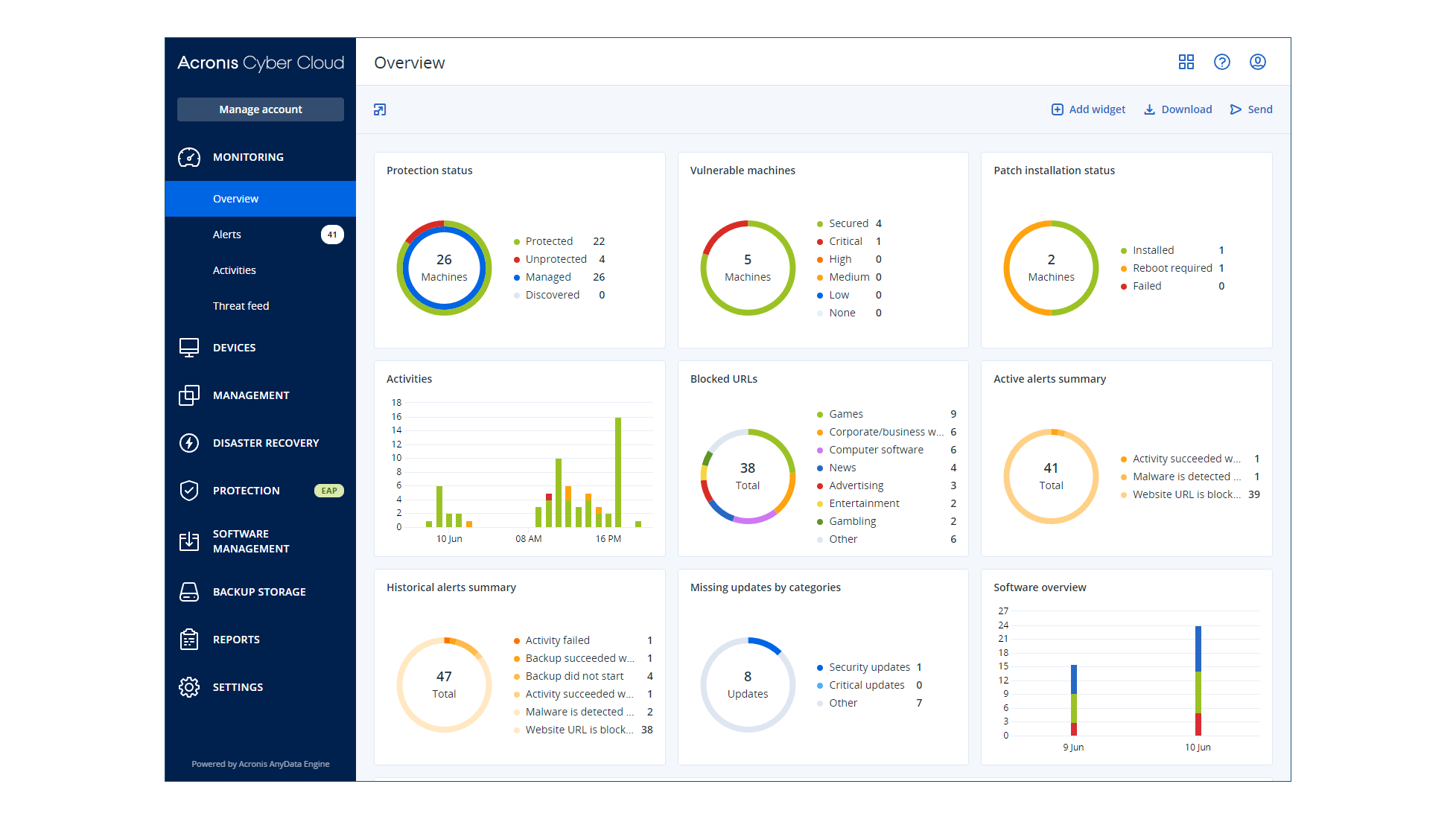 Acronis Cyber Protect 22 Advanced review: The next level of data protection
Acronis Cyber Protect 22 Advanced review: The next level of data protectionReviews Joined-up hybrid backup and cybersecurity services, all easily managed from a single cloud portal
-
 Medigate and CrowdStrike bolster IoT medical device security
Medigate and CrowdStrike bolster IoT medical device securityNews CrowdStrike will integrate its Falcon software with Medigate’s device security platform
-
 Dell and Secureworks team up to protect IT environments
Dell and Secureworks team up to protect IT environmentsNews The subscription-based service is available today in North America but the rest of the world will have to wait until 10 May
-
 AWS CISO urges companies to adopt a zero-trust security approach
AWS CISO urges companies to adopt a zero-trust security approachNews Steve Schmidt outlines how his entire security strategy is based around the zero-trust philosophy
-
 Microsoft expands Defender capabilities for Linux systems
Microsoft expands Defender capabilities for Linux systemsNews Defender for Endpoint customers will be able to detect and remediate advanced threats involving Linux servers
-
 Mobile browser flaw exposes users to spoofing attacks
Mobile browser flaw exposes users to spoofing attacksNews Safari and Opera Touch browsers are among those which can be exploited to target victims with malware
-
 What is shadow IT?
What is shadow IT?In-depth Hardware and software that isn't authorised by IT departments can leave businesses vulnerable