Windows 10 users encounter ‘blue screen of death’ after latest Patch Tuesday update
Microsoft said it is working on a fix for the issue and has offered users a temporary workaround


Microsoft has warned that some Windows 10 users may encounter the infamous ‘blue screen of death’ (BSOD) after installing its latest 'Patch Tuesday' security updates.
In an update on the Windows Health Dashboard, the company revealed that the blue screen issue could affect selected users who downloaded the KB5021233 update in this month’s recent raft of security fixes.
KB5021233 was initially intended to resolve an issue affecting the Camera app after users reported that the app stops responding when memory is low.
The issue has so far affected users operating several different versions of Windows 10, the firm revealed, including 22H2, 21H2, 21H1, and 20H2.
Impacted users have been met with the BSOD and error code 0xc000021a upon startup, and have been unable to access devices.
“After installing KB5021233, there might be a mismatch between the file versions of hidparse.sys in c:/windows/system32 and c:/windows/system32/drivers (assuming Windows is installed to your C: drive), which might cause signature validation to fail when cleanup occurs,” Microsoft confirmed in its update over the weekend.
How to fix the issue
Microsoft revealed it is currently “working on a resolution” for the issue and said it will provide an update in an upcoming release.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
However, for users currently affected by the problem, the firm offered a temporary workaround using the Windows Recovery Environment (WinRE).
“To mitigate this issue on devices already experiencing it, you will need to use Windows Recovery Environment (WinRE),” Microsoft said.
The firm outlined the following steps for affected users:
- Enter Windows Recovery Environment. If your device has not automatically started up into WinRE, please see Entry points into WinRE.
- Select 'Troubleshoot'
- Select the 'Start recovery, troubleshooting, and diagnostic tools button
- Select 'Advanced Options'
- Select 'Command Prompt' and wait for your device to restart, if needed.
- Your device should restart to a Command Prompt window. You might need to sign into your device with your password before getting to the Command Prompt window
- Run the following command (Important: If Windows is not installed to C:\windows you will need to modify the command to your environment): xcopy C:\windows\system32\drivers\hidparse.sys C:\windows\\system32\hidparse.sys
- Once the previous command completes, type: exit
- Select 'Continue'
After following these steps, Microsoft said Windows should now startup “as expected” for users. The firm also warned users against finding alternative workarounds.
“It is not recommended to follow any other workaround than those recommended above. We do not recommend deleting the hidparse.sys from your Windows\System32 folder,” the company said.
Patch Tuesday
This particular issue comes as a result of Microsoft’s recent Patch Tuesday update, issued on 13 December.
As part of the update, Microsoft patched a number of critical vulnerabilities along with fixes for two critical zero-day vulnerabilities.
49 vulnerabilities were disclosed in the bulletin last week. Six were rated as ‘critical’ while another was identified as having been actively exploited in the wild.
The exploited bug, tracked as CVE-2022-44698, was found to affect Windows SmartScreen and enabled threat actors to bypass Mark of the Web (MOTW) protocols.

Ross Kelly is ITPro's News & Analysis Editor, responsible for leading the brand's news output and in-depth reporting on the latest stories from across the business technology landscape. Ross was previously a Staff Writer, during which time he developed a keen interest in cyber security, business leadership, and emerging technologies.
He graduated from Edinburgh Napier University in 2016 with a BA (Hons) in Journalism, and joined ITPro in 2022 after four years working in technology conference research.
For news pitches, you can contact Ross at ross.kelly@futurenet.com, or on Twitter and LinkedIn.
-
 The Microsoft bug bounty program just got a big update — and even applies to third-party code
The Microsoft bug bounty program just got a big update — and even applies to third-party codeNews Microsoft is expanding its bug bounty program to cover all of its products, even those that haven't previously been covered by a bounty before and even third-party code.
-
 IBM AIX users urged to patch immediately as researchers sound alarm on critical flaws
IBM AIX users urged to patch immediately as researchers sound alarm on critical flawsNews Network administrators should patch the four IBM AIX flaws as soon as possible
-
 A journey to cyber resilience
A journey to cyber resiliencewhitepaper DORA: Ushering in a new era of cyber security
-
 A new framework for third-party risk in the European Union
A new framework for third-party risk in the European Unionwhitepaper Report: DORA and cyber risk
-
 Should your business start a bug bounty program?
Should your business start a bug bounty program?In-depth Big tech firms including Google, Apple and Microsoft offer bug bounty programs, but can they benefit smaller businesses too?
-
 OpenAI to pay up to $20k in rewards through new bug bounty program
OpenAI to pay up to $20k in rewards through new bug bounty programNews The move follows a period of unrest over data security concerns
-
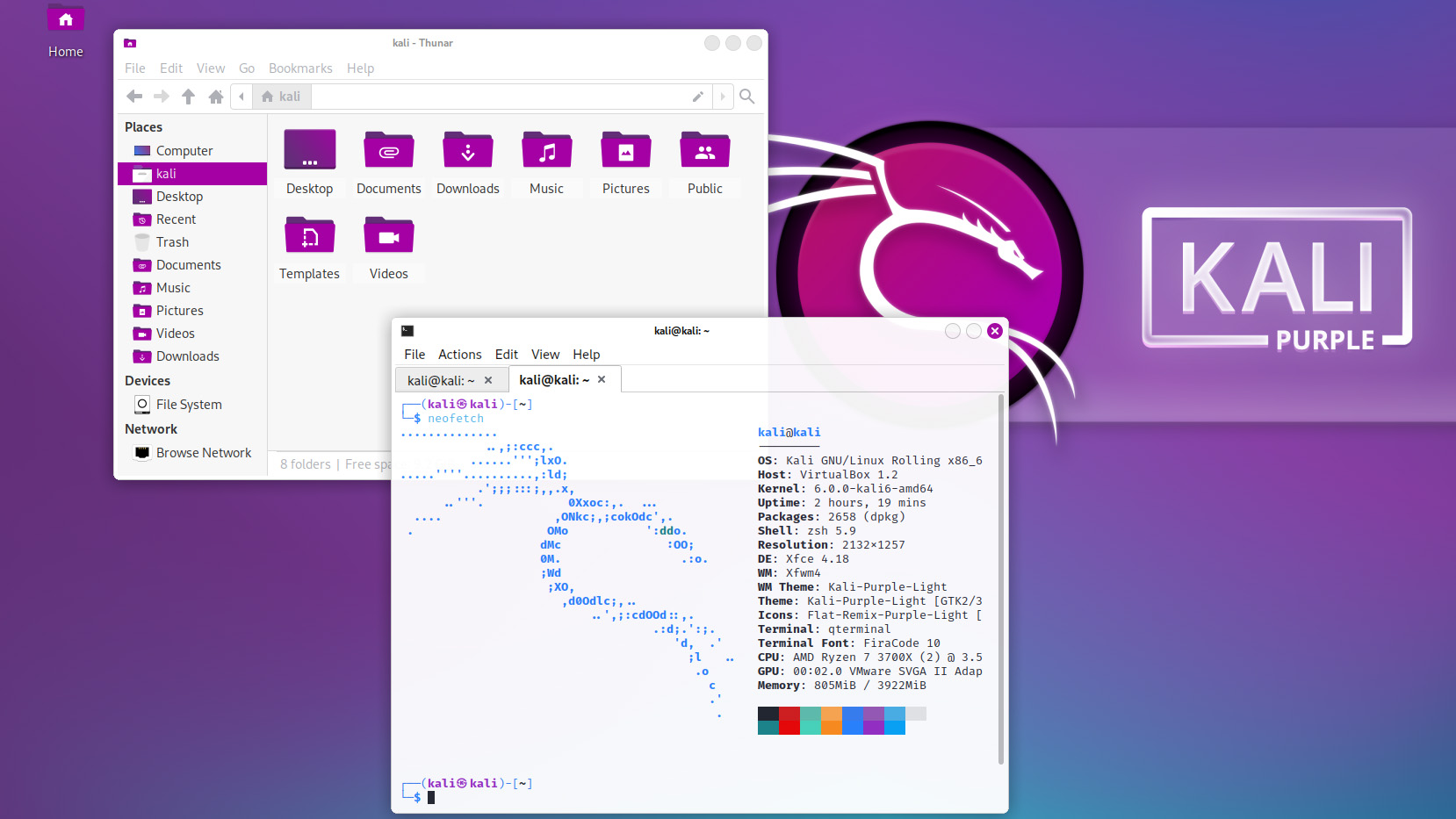 Kali Linux releases first-ever defensive distro with score of new tools
Kali Linux releases first-ever defensive distro with score of new toolsNews Kali Purple marks the next step for the red-teaming platform on the project's tenth anniversary
-
 Windows 11 System Restore bug preventing users from accessing apps
Windows 11 System Restore bug preventing users from accessing appsNews Microsoft has issued a series of workarounds for the issue which is affecting a range of apps including Office and Terminal

