Apple's T2 security chip has an "unpatchable" vulnerability
Exploiting the checkm8 and blackbird flaws can grant attackers control over a macOS-powered device


The sophisticated T2 security module embedded in Mac computers can be hijacked by combining two existing vulnerabilities that can allow hackers to successfully “jailbreak” Macs and MacBooks.
The operating system run by the T2 security chip, sepOS, suffers from an exploit first identified in the iPhone X, dubbed checkm8, which can be used to circumvent activation lock, allowing stolen handsets to be reset and sold illegally.
Researchers with Iron Peak have demonstrated how it’s possible to combine this flaw, which is also present in the T2 chips embedded in some Mac devices, with the blackbird vulnerability, first identified by Pangu researchers.
When hit with checkm8, the T2 chip on macOS devices normally exits with a fatal error if it’s in Device Firmware Update (DFU) mode and detects a decryption call. Exploiting blackbird, however, could allow a hacker to bypass this check.
“Apple left a debugging interface open in the T2 security chip shipping to customers, allowing anyone to enter Device Firmware Update (DFU) mode without authentication,” Iron Peak said in a blog post. “Using this method, it is possible to create an USB-C cable that can automatically exploit your macOS device on boot.
“Once you have access on the T2, you have full root access and kernel execution privileges since the kernel is rewritten before execution.
Apple’s T2 security chip is a co-processor that sits alongside the CPU and harbours data and functions pertinent to the security of the device, including boot operations, and includes features such as audio processing.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
The hardware-enabled security component, which runs bridgeOS, is a custom Arm processor based on the A10 CPU found in the iPhone 7. Modern Macs run more recent iterations of the T2 chip based on A12 architecture, and bridgeOS firmware, although a huge portion of current devices still use the A10 and sepOS.
The T2 chip performs a set of predefined tasks in macOS including functioning as a hardware security module for features such as Apple KeyChain or two-factor authentication. Other functions may include accelerating media playback, whitelisting kernel extensions, and cryptographic operations.
The flaw currently affects the devices shipped with Intel CPUs and may not affect Mac devices that are manufactured with Arm-based processors in the next hardware cycle, although the researchers added there was no guarentee.
Alarmingly, Iron Peak researchers claim the core vulnerability is unpatchable because sepOS/BootROM is read-only memory for security reasons, and therefore it cannot be fixed without hardware revisions.
The better news is that if users deploy FileVault2 as disk encryption, potential hackers won’t have access to data stored on the device immediately. They can, however, inject a keylogger in the T2 firmware since it manages keyboard access, storing any passwords for retrieval or transmission, in the event of a malicious hardware attachment.
IT Pro approached Apple for a statement on the two vulnerabilities.

Keumars Afifi-Sabet is a writer and editor that specialises in public sector, cyber security, and cloud computing. He first joined ITPro as a staff writer in April 2018 and eventually became its Features Editor. Although a regular contributor to other tech sites in the past, these days you will find Keumars on LiveScience, where he runs its Technology section.
-
 Windows 11 Pro and CDW - Overcoming today's escalating cyberthreats
Windows 11 Pro and CDW - Overcoming today's escalating cyberthreatswhitepaper Employing a security-by-default approach with the latest Windows 11 Pro devices
-
 Onward: How security drives business opportunity
Onward: How security drives business opportunitywhitepaper Do you consider security as a business investment or a business enabler?
-
 ASUS routers receive patches for critical vulnerabilities affecting more than a dozen product lines
ASUS routers receive patches for critical vulnerabilities affecting more than a dozen product linesNews Nearly 20 models have been affected by a spate of vulnerabilities, including two rated ‘critical’
-
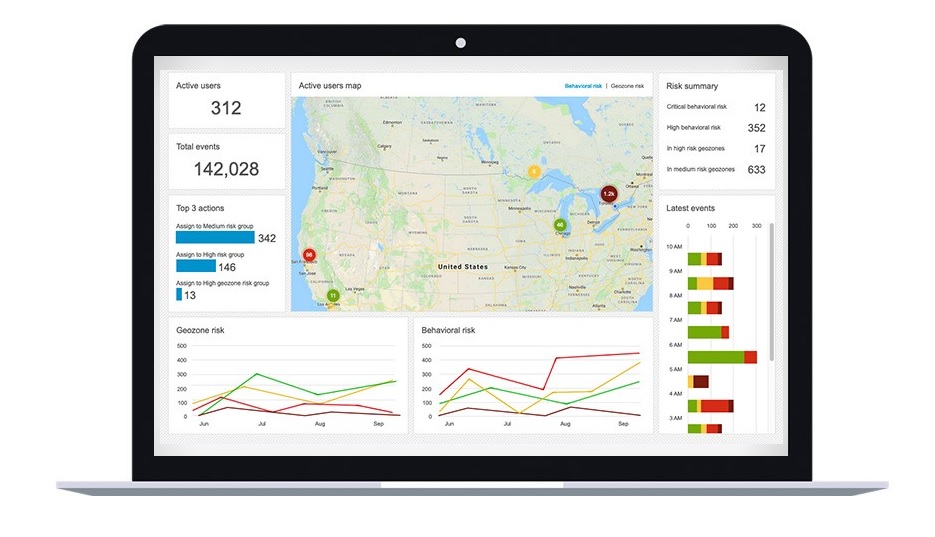 BlackBerry Persona Desktop delivers zero-trust security at the endpoint
BlackBerry Persona Desktop delivers zero-trust security at the endpointNews New security solution learns user behavior and can take action if there’s an abnormality


