AWS malvertising campaign a “potent threat” to users, researchers warn
The recent flurry of ‘malvertising’ attacks is raising concerns that users face heightened search engine risks


AWS customers have been targeted in a malvertising campaign which sought to steal user cloud credentials, prompting warnings from security experts.
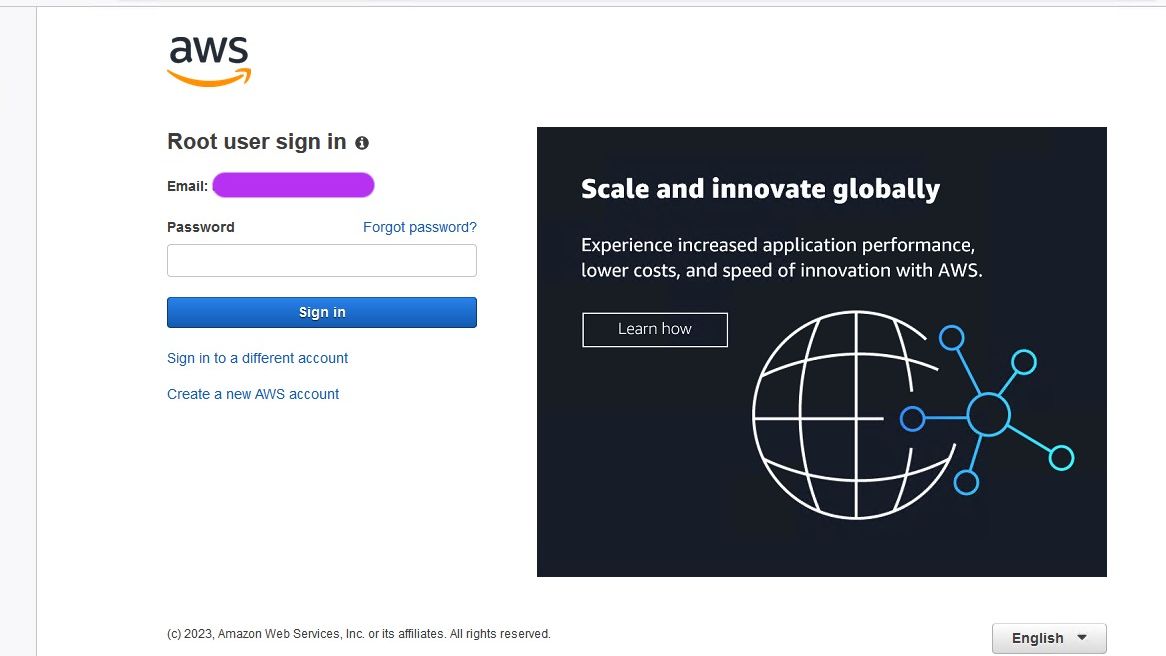
Research from security firm SentinelOne uncovered fake AWS ads distributed on Google to dupe unknowing users into disclosing login credentials.
The malicious ads were ranked second behind the official AWS site, researchers revealed, and directed users to a phishing website which mimicked the official page.
In an attempt to evade Google’s ad-fraud detection tools, threat actors were also found to have adapted their campaign by adding additional redirects to further deceive users.
“The ad itself goes to a hop domain, which is an actor-controlled blogger website,” said Tom Hegel, senior threat researcher at SentinelOne. "This first hop then redirects to the actual credentials phishing page hosted on a second domain.
“After the victim submits their credentials, a final redirect sends the victim to the legitimate AWS login page,” he added. “The redirect represents an effort to evade detection by cautious users, but more importantly to evade automated detection of the phishing websites and malicious ad monitors.”
Hegel noted that the various hops and content included in the webpages of each domain added to the complexity of automated detection in attacks such as these.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
SentinelOne said it reported the malvertising campaign to Cloudflare, which hosted the phishing sites. The firm subsequently shut down accounts belonging to the threat actors.
Recurring threats
SentinelOne believes that this malvertising campaign can be attributed to an attacker responsible for previous attempts to trick AWS users.
Permiso’s P0 Labs conducted a recent review of AWS phishing sites, and researchers observed a number of notable similarities.
“Several characteristics unique to the phishing pages are noteworthy, including the layout, design, and efforts to hinder analysis as well as the developers’ spoken language,” Hegel said.
The phishing websites used in this campaign included a specific JavaScript function to prevent right clicks, middle mouse buttons, and keyboard shortcuts, SentinelOne revealed.
The purpose of this code is “likely to prevent users from copying content from the webpage,” researchers said.
Malvertising on the rise
This incident marks the latest in a growing number of malvertising campaigns as attackers seek new ways to target users.
Last month, Bitwarden customers raised concerns that malicious Google ads were being used to direct users to malware-ridden sites.
RELATED RESOURCE
PowerEdge - Cyber resilient infrastructure for a Zero Trust world
Combat threats with an in-depth security stance
Just days prior, users of streaming platform OBS were targeted in a campaign which saw a cryptocurrency influencer lose access to their NFT wallet and Substack account.
This prompted criticism of Google’s current process with regard to tackling malicious ads circulating in its search engine.
Security researcher Will Dormann questioned why VirusTotal, a Google-owned threat analysis tool, has not been leveraged by the tech giant to automatically vet sponsored links for malware.
IT Pro has approached Google for comment on its ad fraud detection processes.
Research from the HP Wolf Security Threat Research division has observed a marked increase in this attack method in recent months, and issued a warning to users over the surge in attacks.
“In the last two months, we’ve seen a significant increase in malware distributed through malvertising, with multiple threat actors currently using this technique,” researchers said in a January blog post.
SentinelOne said the proliferation of malicious Google ads now represents a “serious threat not just to average users, but network and cloud administrators".
“The ease with which these attacks can be launched, combined with the large and diverse audience that Google ads can reach, makes them a particularly potent threat,” the firm said.

Ross Kelly is ITPro's News & Analysis Editor, responsible for leading the brand's news output and in-depth reporting on the latest stories from across the business technology landscape. Ross was previously a Staff Writer, during which time he developed a keen interest in cyber security, business leadership, and emerging technologies.
He graduated from Edinburgh Napier University in 2016 with a BA (Hons) in Journalism, and joined ITPro in 2022 after four years working in technology conference research.
For news pitches, you can contact Ross at ross.kelly@futurenet.com, or on Twitter and LinkedIn.


