The scariest cyber security horror stories of 2022
Lapsus$ group, Log4Shell, new Microsoft Exchange vulnerabilities, and the Russia-Ukraine war dominated cyber security headlines in 2022


Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
You are now subscribed
Your newsletter sign-up was successful
In a year of upheavals that saw the death of Queen Elizabeth II, three changes of UK prime minister, and Russia’s invasion of Ukraine, one thing that has remained unfortunately consistent is cyber criminals ramping up attacks.
Some trends prevail: Ransomware remains popular, fuelled by the sheer volume of revenue available to the gangs and criminals involved in the lucrative market. The Lapsus$ group has been particularly active in 2022, allegedly breaching the likes of Microsoft, Uber, and Nvidia.
The supply chain is still a common vector of attack, with the Okta breach at the beginning of the year showing the damage that can be done to a firm’s reputation if it fails to act quickly in disclosing an incident.
Cyber criminals have also started to broaden their horizons to focus on digital currencies, with cryptocurrency exchanges, platforms, and personal wallets increasingly targeted over the course of the year.
We’ve rounded up the scariest security horror stories of 2022.
Log4Shell vulnerability wreaks havoc throughout 2022
The Log4Shell vulnerability continues to wreak havoc on businesses a year after it first sent shockwaves through the security industry. Discovered in December 2021, the zero-day remote code execution (RCE) flaw in Java logger Log4j was so impactful because of the sheer number of applications and services it powers: Log4j is used by millions of computers across many organisations and underpins multiple internet services and applications, including Twitter, Microsoft, and Amazon.
With a 10/10 critical rating, the Log4Shell flaw – which has the NIST National Vulnerability Database designation CVE-2021-44228 – is relatively easy to exploit, because it doesn’t require privileged access to be used in attacks. It’s therefore no surprise that just 24 hours after it was disclosed, researchers at security firm Checkpoint recorded almost 200,000 attempts to exploit the issue. A week after Log4Shell went public, cyber criminals and other malicious actors had used the flaw as part of over 1.2 million attacks globally.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
The Log4Shell issue persisted well into 2022. In February, the flaw was used by Iranian state sponsored attackers targeting the US government. Even as late as October 2022, it was reported that a China government-linked group had used the vulnerability to target multiple entities in the Middle East.
In November, security firm Tenable found that despite patching and mitigating the issue, as many as 72% of firms remain vulnerable to Log4Shell.
Massive hack on Uber claimed by the infamous Lapsus$
Uber found itself caught up in one of the biggest security breaches of the year when malicious adversaries were able to gain access to systems after fooling an employee into handing over details.
News of the breach was first reported by the New York Times in September, with the attacker themself informing the publication of the incident. Shortly afterwards, the company pointed the finger at the Lapsus$ hacking group, which has targeted other technology firms including Microsoft and Nvidia, as the originators of the attack.
Seven people were subsequently arrested in March by City of London Police, which is leading the international investigation into Lapsus$, with two teenagers appearing in court in April.
RELATED RESOURCE

Getting board-level buy-in for security strategy
Why cyber security needs to be a board-level issue
Uber said the adversary managed to gain access to a contractor’s account by spamming multi-factor authentication prompts. Uber suspects the contractor’s device was infected with malware, allowing attackers to steal credentials and sell them online.
Using the stolen credentials, the attackers were able to gain access to some of Uber’s internal systems, including Slack messages, a finance tool for invoices and a dashboard where security researchers report vulnerabilities.
Uber said customer data was not compromised, but the firm quickly embarked on a hiring spree to shore up its security defences.
Ransomware continues to hit organisations across the globe

Ransomware continued to ravage organisations across the world in 2022, with two attacks in particular standing out.
The first was a double whammy affecting Costa Rica, which suffered a series of attacks during the year. In April, the country was hit by a cyber assault targeting critical civil infrastructure allegedly perpetrated by Russian group Conti. Among the services disrupted were international trade and tax collection, with affected organisations forced to rely on pen and paper to get things done and the government ultimately declaring a national state of emergency.
The following month, just as it was getting back on its feet, the country was hit by a new ransomware attack, this time targeting the Costa Rican Social Security Fund (CCSS), which runs its public healthcare. Over 30,000 medical appointments had to be rescheduled after the Hive ransomware group – which is thought to have some links with the original attackers – took out IT systems across the country’s hospitals and clinics
Overall, the attacks cost organisations operating in Costa Rica hundreds-of-millions of US dollars.
The second big ransomware incident of the year took place in October, when Australian health insurance firm Medibank was hit by a ransomware group linked to Russian-speaking REvil. When the company refused to pay the ransom, the gang published sensitive medical records including customers’ names, passport numbers, dates of birth and claim information. The attackers even separated the stolen customer data into “naughty” and “good” lists, depending on whether diagnosis was linked to factors such as drug addiction or alcohol abuse.
Because it’s such a lucrative business model with a growing number of “as a service” offerings to outsource to, ransomware isn’t going to go away any time soon and will continue to threaten businesses well into 2023 and beyond.
Bitcoin heists hit on cryptocurrency exchanges, platforms, and personal wallets
Cyber attackers will always follow the money, and cryptocurrency is no exception. What’s more, crypto trades aren’t linked to people’s identities, making them an attractive prospect for criminals.
In October, it was reported that investors have lost over $3 billion (£2.46 billion) to attackers across 125 hacks in 2022 so far. This is likely to surpass 2021 as the biggest year for hacking on record, according to blockchain analytics company Chainalysis.
Among the big incidents in 2022, the start of the year saw Matt Damon-backed cryptocurrency exchange Crypto.com hacked, impacting 483 users. The site admitted attackers were able to make off with $35 million (£28.7 million) of unauthorised withdrawals of Bitcoin and Ether as a result of the heist.
Then in February, attackers stole $320 million (£262 million) from the Wormhole protocol – a bridge that links the Ethereum and Solana cryptocurrency blockchains. The following month, the Ronin Network lost over $620 million (£509 million) after an attacker compromised private keys and organised fake withdrawals. Then in April, Beanstalk Farms – a network to balance out supply and demand of cryptocurrencies – was attacked and $182 million (£149 million) of digital currency stolen.
In August, attackers were able to breach Nomad, a programme allowing users to exchange tokens from one blockchain to another, stealing around $190 million (£156 million) in Bitcoin.
Russia-Ukraine war raises cyber attack fears

Cyber security experts began to warn about the risk of widespread cyber attacks originating from Russia as soon as it invaded Ukraine in February 2022. Fears were rife that Russian hackers would attempt to compromise critical infrastructure such as electric grids and that these attacks could also target Ukraine’s allies, including the UK and the US.
In March, US President Joe Biden warned businesses in critical sectors to be on alert amid the growing Russian cyber threat. The National Cyber Security Centre (NCSC) also warned that HermeticWiper malware was in use against Ukrainian organisations and said it could impact other countries.
But in general, attacks have been limited and simple in their scope, at least partly because the US and Europe provided significant cyber expertise to Ukraine and other Eastern European nations prior to the war.
That’s not to say there have been no ill effects and some attacks caused disruption in the early days of the conflict, especially to communications services. One of the first cyber assaults on broadband company Viasat on 24 February began approximately one hour before Russia launched its invasion of Ukraine. The NCSC said Russia was “almost certainly responsible for the attack”, which impacted personal and commercial internet users, wind farms in central Europe, and the Ukrainian military, which is assumed to have been its original intended target.
In March, Ukraine’s biggest fixed-line telecommunications company, Ukrtelecom was hit by a severe cyber attack which took the company’s services across the country down.
ProxyNotShell Microsoft Exchange vulnerabilities plague admins
In 2021, the ProxyShell and ProxyLogon vulnerabilities in Microsoft Exchange dominated headlines, partly because they were so easy to exploit. One year later, a new pair of vulnerabilities affecting Exchange Server has emerged, collectively known as ProxyNotShell.
Discovered in September by security researchers at Vietnam-based company GTSC, the two zero-days received a number of attempted fixes before Microsoft issued a patch in November. GTSC said in its report that it had noticed in-the-wild exploitation of both vulnerabilities for at least a month before publishing its findings, and Microsoft later confirmed the flaws were being used in attacks.
Tracked as CVE-2022-41040 and CVE-2022-41082, the already-exploited flaws are used one after the other to elevate privileges via a server side request forgery (SSRF) to gain access to Microsoft Exchange’s PowerShell backend, then carry out a remote code execution on a vulnerable server.
Both issues affect Microsoft Exchange versions 2013, 2016, and 2019, and are rated as having a high severity with a CVSSv3 score of 8.8/10.
Even now, the flaws are sending shivers down Exchange Server admins’ spines because while an attacker does need to be authenticated, they are very easy to exploit.
Okta hack highlights the PR side of incident response
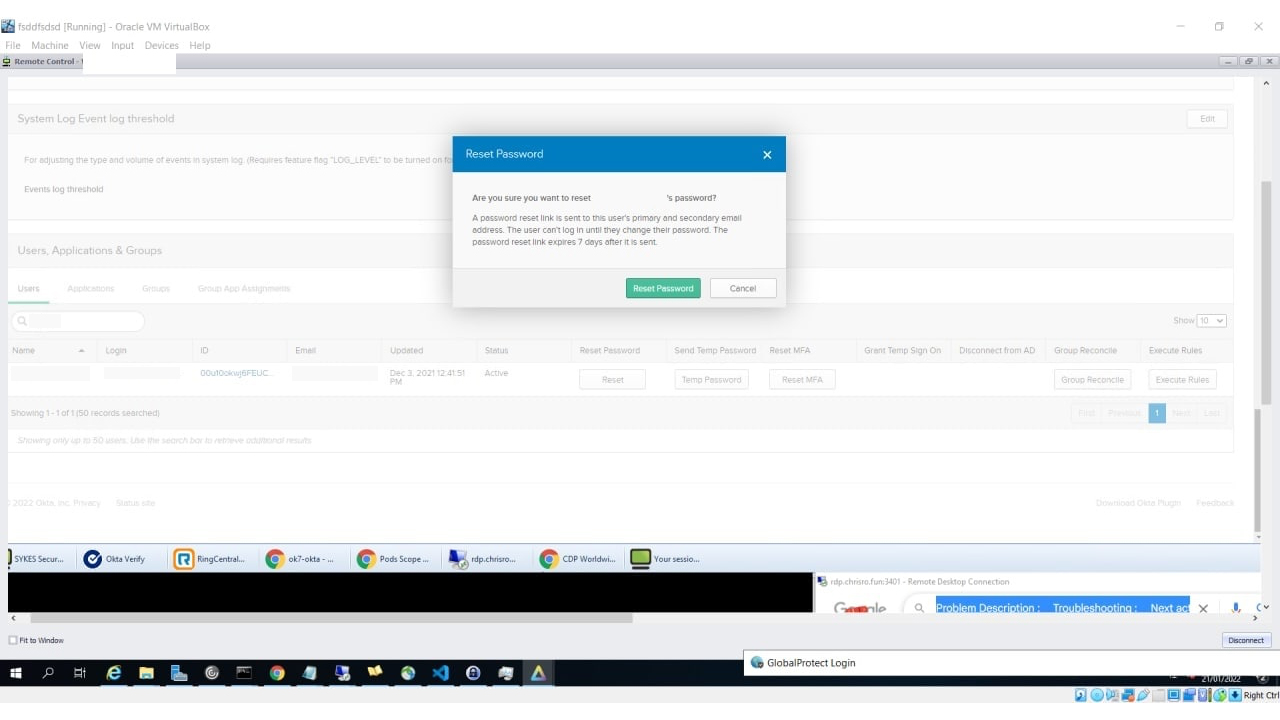
When Okta was breached in January 2022, hundreds of its clients were affected. Yet the company, which provides “single sign on” software and manages logins for over 100 million customers, only admitted it had been hacked via a third-party customer support provider two months later, in March. The admission came after the Lapsus$ group claimed it had breached the firm, posting screenshots.
RELATED RESOURCE

Getting board-level buy-in for security strategy
Why cyber security needs to be a board-level issue
Okta initially released a statement saying the breach “was investigated and contained” but admitted the screenshots shared online are “connected to this January event”. It also said there is “no evidence of ongoing malicious activity beyond the activity detected in January”.
However, as concern about the incident mounted, the firm released a number of blogs. In one, Okta chief security officer David Bradbury said hackers had accessed the computer of a customer support engineer employed by Sykes, part of the Sitel Group, over a five-day period. He said the incident was "analogous to walking away from your computer at a coffee shop, whereby a stranger has – virtually, in this case – sat down at your machine and is using the mouse and keyboard".
He emphasised that access was limited and Okta itself had not been breached, however.
Okta admitted later that it “made a mistake” delaying disclosure of the breach. “In January, we did not know the extent of the Sitel issue – only that we detected and prevented an account takeover attempt and that Sitel had retained a third-party forensic firm to investigate,” the company said. “At that time, we didn’t recognise that there was a risk to Okta and our customers. We should have more actively and forcefully compelled information from Sitel.”
As well as highlighting the importance of supply chain security, the Okta breach demonstrates the need for transparency and clarity in the event of an incident. In an age of increasing cyber attacks, customers understand that breaches happen, but they also expect a quick and clear response.
Kate O'Flaherty is a freelance journalist with well over a decade's experience covering cyber security and privacy for publications including Wired, Forbes, the Guardian, the Observer, Infosecurity Magazine and the Times. Within cyber security and privacy, her specialist areas include critical national infrastructure security, cyber warfare, application security and regulation in the UK and the US amid increasing data collection by big tech firms such as Facebook and Google. You can follow Kate on Twitter.
-
 Cohere's Aleph Alpha merger could create a transatlantic sovereign AI powerhouse
Cohere's Aleph Alpha merger could create a transatlantic sovereign AI powerhouseAnalysis The merger between Cohere and Aleph Alpha aims to capitalize on the burgeoning sovereign AI market
-
 Everything you need to know about OpenAI's new workspace agents
Everything you need to know about OpenAI's new workspace agentsNews New ‘workspace agents’ from OpenAI will automate tasks for workers and can be customized for specific roles
-
 Uber to offer electric vehicles to London customers
Uber to offer electric vehicles to London customersNews The ride-sharing platform won't charge customers extra for using Uber Green, but journeys need to start in 'Zone 1'
-
 Driverless Cars: Uber car involved in fatal crash had software flaws
Driverless Cars: Uber car involved in fatal crash had software flawsNews However, US investigators still haven't determined the probable cause for the accident
-
 UberEats struggles to meet demand on launch day
UberEats struggles to meet demand on launch dayNews Users complain of late or cancelled deliveries on service's first day
-
 Google, Ford, Uber and Lyft form driverless cars coalition
Google, Ford, Uber and Lyft form driverless cars coalitionNews Self- Driving Coalition for Safer Streets hopes to speed up delivery of cars on the road
-
 Uber hails TfL’s move to scrap “bonkers” London cab proposals
Uber hails TfL’s move to scrap “bonkers” London cab proposalsNews TfL abandons plans to stop apps showing where the nearest taxi is
-
 Uber acquires mapping assets from Microsoft Bing
Uber acquires mapping assets from Microsoft BingNews Uber has announced it will buy parts of Microsoft Bing's mapping technology, along with around 100 engineers
-
 Uber ‘bids $3bn for Nokia mapping service’
Uber ‘bids $3bn for Nokia mapping service’News Forrester says taxi-hailing app would own customers' mobile data
