Kaspersky traces spyware attack on staff iOS devices back to 2019
It's currently unclear who is behind the spyware attack on the Russian-based cyber security firm


Russian cyber security firm Kaspersky Lab has discovered covert spyware on its staff’s iPhones that dates back to at least 2019.
The advanced persistent threat (APT) campaign, which Kaspersky has dubbed Operation Triangulation, involves the infection of iOS devices through the iMessage app in order to steal user data.
Researchers said they discovered evidence of the campaign targeting its own staff dating as far back as 2019, and that it, at the time of writing, remains an ongoing threat.
Kaspersky believes the intention of the attack was to place spyware on devices belonging to senior employees at the cyber security company.
The attack is thought to begin with a hidden iMessage being sent to victims, which contains a malicious attachment. This initial payload is then triggered on a device without user knowledge through a zero-click vulnerability.
RELATED RESOURCE

ThreatLabz 2023 Phishing Report
Helping you realize the tactics used in phishing attacks, in order to prevent costly data breaches
Once active, the package connects to the attackers’ command and control (C2) server to download a much larger payload. This exfiltrates personal data, microphone recordings, geolocation information, and photos sent on messaging apps.
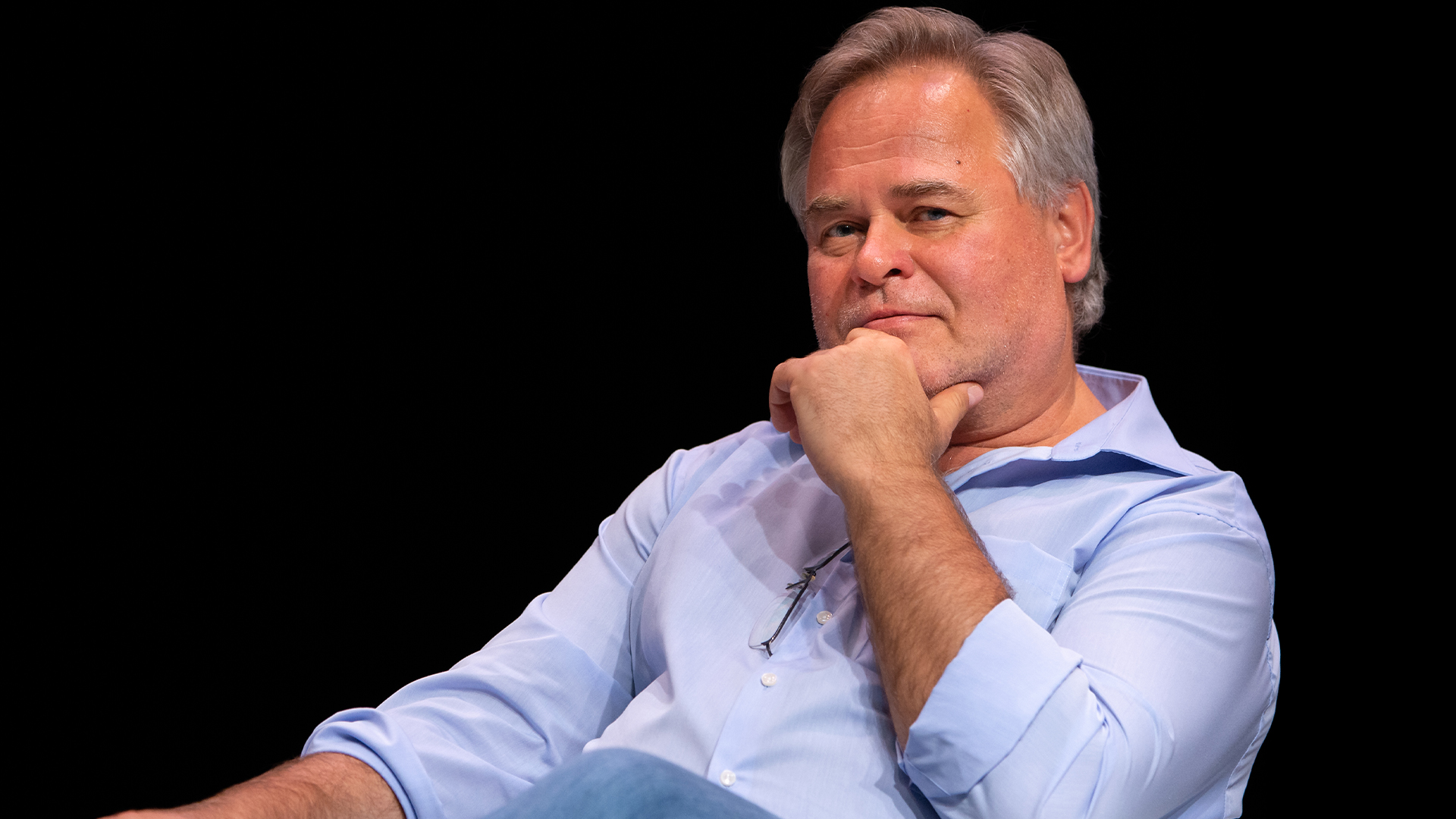
“Our experts have discovered an extremely complex, professional targeted cyberattack that uses Apple’s mobile devices,” wrote Kaspersky Lab CEO Eugene Kaspersky.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
“The purpose of the attack is the inconspicuous placing of spyware into the iPhones of employees of at least our company – both middle and top management.”
Although the closed nature of iOS has impeded efforts to analyze the Triangulation payload, initial research showed that it exploits iOS flaws to perform privilege escalation.
This allows it to run code with root privileges, in which the malware effectively gains total control over a system with the power to amend or remove even core system files.
Kaspersky Lab discovered Operation Triangulation while conducting a scan of its Wi-Fi network traffic.
Malicious activity can be identified in network traffic including network interaction between iMessage and the domain ‘*.ess.apple.com’, connections to a series of known C2 domains, or the download of an encrypted, 242 Kb iMessage attachment.
Another indicator of compromise for Operation Triangulation that has already been found is the appearance of a process titled ‘BackupAgent’ in a device’s data usage lines. Infected devices are also unable to update to the latest version of iOS.
Researchers are confident that the firm is not the main target of Operation Triangulation, but stopped short of speculation over who may be. Further investigation will look at the international spread of the campaign.
Eugene Kaspersky noted that this is not the first time his company has fallen victim to a targeted malware campaign.
He cited Duqu 2.0 as one example, an APT which was discovered on Kaspersky Lab systems in 2015. This sophisticated worm exploited zero-day vulnerabilities in Windows to steal data without detection and did so for three months before being rooted out.
The threat actors behind the sophisticated attack have not yet been identified.
Reuters reported that Russia’s Federal Security Service (FSB) accused the US National Security Agency (NSA) of committing the attacks in collaboration with Apple, without evidence.
Some have compared the activity of the spyware to NSO Group’s Pegasus, the spyware that authoritarian governments used to target high-profile business and media figures through covert observation and data theft.
However, in a Twitter thread Eugene Kaspersky reported that the activity of Operation Triangulation does not overlap with that of known iOS malware such as Pegasus.
Important: The activity observed in Operation Triangulation does not overlap with already known iOS campaigns, such as Pegasus, Predator or Reign.June 1, 2023
Kaspersky researcher Georgy Kucherin also tweeted that the spyware does not persist, and that attackers “have to reinfect the device when it reboots”.
This could raise hopes that regular phone reboots would work as a measure against prolonged device infection.
Evidence of the attack chain suggests that disabling iMessage would protect iOS devices from Operation Triangulation but that once infected, devices have to undergo a factory reset and manual reinstallation of iOS and the user environment.
As infected devices cannot update, a reboot does nothing to make a device less vulnerable to subsequent reinfection.
Eugene Kaspersky speculated in a tweet that the iOS Lockdown Mode security feature could protect against initial infection, but this has not yet been proven.

Rory Bathgate is Features and Multimedia Editor at ITPro, overseeing all in-depth content and case studies. He can also be found co-hosting the ITPro Podcast with Jane McCallion, swapping a keyboard for a microphone to discuss the latest learnings with thought leaders from across the tech sector.
In his free time, Rory enjoys photography, video editing, and good science fiction. After graduating from the University of Kent with a BA in English and American Literature, Rory undertook an MA in Eighteenth-Century Studies at King’s College London. He joined ITPro in 2022 as a graduate, following four years in student journalism. You can contact Rory at rory.bathgate@futurenet.com or on LinkedIn.
-
 Developers warned to avoid 'early-access' Google Gemini tools
Developers warned to avoid 'early-access' Google Gemini toolsNews Attackers are tempting would-be users into downloading reverse shell malware
-
 Researchers warn millions of RDP and VNC servers are wide open to exploitation
Researchers warn millions of RDP and VNC servers are wide open to exploitationNews Researchers at Forescout spotted millions of RDP and VNC servers exposed online
-
 Hackers are disguising malware as ChatGPT, Microsoft Office, and Google Drive to dupe workers
Hackers are disguising malware as ChatGPT, Microsoft Office, and Google Drive to dupe workersNews Beware of downloading applications like ChatGPT, Microsoft Office applications, and Google Drive through search engines
-
 Almost half of US organizations still using Kaspersky, researchers claim
Almost half of US organizations still using Kaspersky, researchers claimNews A ban was introduced due to Kaspersky’s supposed links to the Russian government
-
 Enterprises are struggling to fill senior cybersecurity roles — and it's causing staff burnout to skyrocket
Enterprises are struggling to fill senior cybersecurity roles — and it's causing staff burnout to skyrocketNews Many senior roles take months to fill, creating cumbersome workloads for mid-level staff and increased burnout
-
 Kaspersky to shut down US division ahead of sales ban
Kaspersky to shut down US division ahead of sales banNews The Russian security company will exit the US and cut staff ahead of a government-imposed sales ban
-
 Botnets are being sold on the dark web for as little as $99
Botnets are being sold on the dark web for as little as $99News More than 20 offers for botnets for hire or sale have been discovered on dark web forums and Telegram channels this year
-
 Small businesses face continued security threats as trojan attacks surge
Small businesses face continued security threats as trojan attacks surgeNews Cyber attacks on small businesses are still growing at a steady pace
-
 Most passwords take a matter of minutes to crack – here’s how you can create strong, hacker-resistant credentials
Most passwords take a matter of minutes to crack – here’s how you can create strong, hacker-resistant credentialsNews Passwords are still criminally insecure and can be cracked or guessed by hackers with ease, but what precautions can you take to avoid getting breached?
-
 Kaspersky hits back at US software ban, citing political motivations and “theoretical concerns”
Kaspersky hits back at US software ban, citing political motivations and “theoretical concerns”News Kaspersky said it has “repeatedly demonstrated" its independence from any government interference