Microsoft Defender “obliterating” users with false password alerts
Windows 11 devices have been affected by the Defender for Endpoint error, which flags SSO domains as problematic


Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
You are now subscribed
Your newsletter sign-up was successful
System administrators have reported an abudance of alerts from Microsoft Defender for Endpoint, with multiple sites falsely flagged as having reused passwords.
A number of admins complained that they are receiving alerts that read “Password reuse activity was detected by Microsoft Defender for Endpoint” with no clear explanation from the software.
Users denied having reused passwords on the sites flagged by the system, while others have stated that multiple subdomains of software as a service (SaaS) platforms have been flagged as containing password reuse.
Many admins indicated that the problem could have arisen from Defender for Endpoint incorrectly flagging single sign-on (SSO) domains as needing attention.
“We now have 17 alerts today for Password Reuse. Everyone I have looked at is a false positive,” one user wrote.
They also noted that some alerts come with “about:blank” as the supposed domain containing password reuse, and that in one case a user was accused of “password reuse over three services, listing three subdomains of the same SaaS”.
The warning message itself is seemingly absent from Microsoft documentation.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
"We determined these are false positive results and we have resolved this," a Microsoft spokesperson told ITPro.
"No customer action is needed."
RELATED RESOURCE

According to accounts from multiple commenters, the alerts appear to only be coming from Windows 11 devices and almost all relate to supposed password reuse on Microsoft domains.
“Yup same here, we are getting obliterated with alerts. The alerts are only coming from Win 11 devices,” wrote another.
Dozens of new commenters have appeared in a six-month-old thread covering the same issue, seeking help with inexplicable alerts that they too have received.
In a Twitter exchange on the issue, one user suggested that the problem could be linked to enhanced phishing protection brought in by Microsoft in September 2022.
This is intended to warn users against reusing passwords.
All this is related to SSO and OAuth and the only URI being flagged is https://t.co/oZk8RKMK00 (with various URLs)But yeah, fun trying to explain the user is not even entering a password 😬April 20, 2023
Microsoft Defender has incorrectly inundated users with warnings on multiple prior occasions.
In September 2022, the app caused confusion after flagging software as ransomware, including popular browsers and productivity apps such as Chrome, Slack, and Microsoft Edge.
Further false positives were addressed by Microsoft in January 2023, after a faulty update deleted shortcuts that had been incorrectly identified as malware.
Microsoft released scripts to fix the issue, though some administrators stated that these were imperfect and failed to fully rectify matters.
A recent update for Microsoft Defender Antivirus also led to confusion among devs, who upon updating received a warning stating that Local Security Authority (LSA) Protection - a process used to authenticate and oversee user logins - had been disabled.
Microsoft released a workaround for the issue, though a subsequent update appears to have disabled LSA altogether on Windows 11 systems in favor of a new process titled ‘Kernel-mode Hardware-enforced Stack Protection’.
This article has been updated to include a statement from Microsoft.

Rory Bathgate is Features and Multimedia Editor at ITPro, overseeing all in-depth content and case studies. He can also be found co-hosting the ITPro Podcast with Jane McCallion, swapping a keyboard for a microphone to discuss the latest learnings with thought leaders from across the tech sector.
In his free time, Rory enjoys photography, video editing, and good science fiction. After graduating from the University of Kent with a BA in English and American Literature, Rory undertook an MA in Eighteenth-Century Studies at King’s College London. He joined ITPro in 2022 as a graduate, following four years in student journalism. You can contact Rory at rory.bathgate@futurenet.com or on LinkedIn.
-
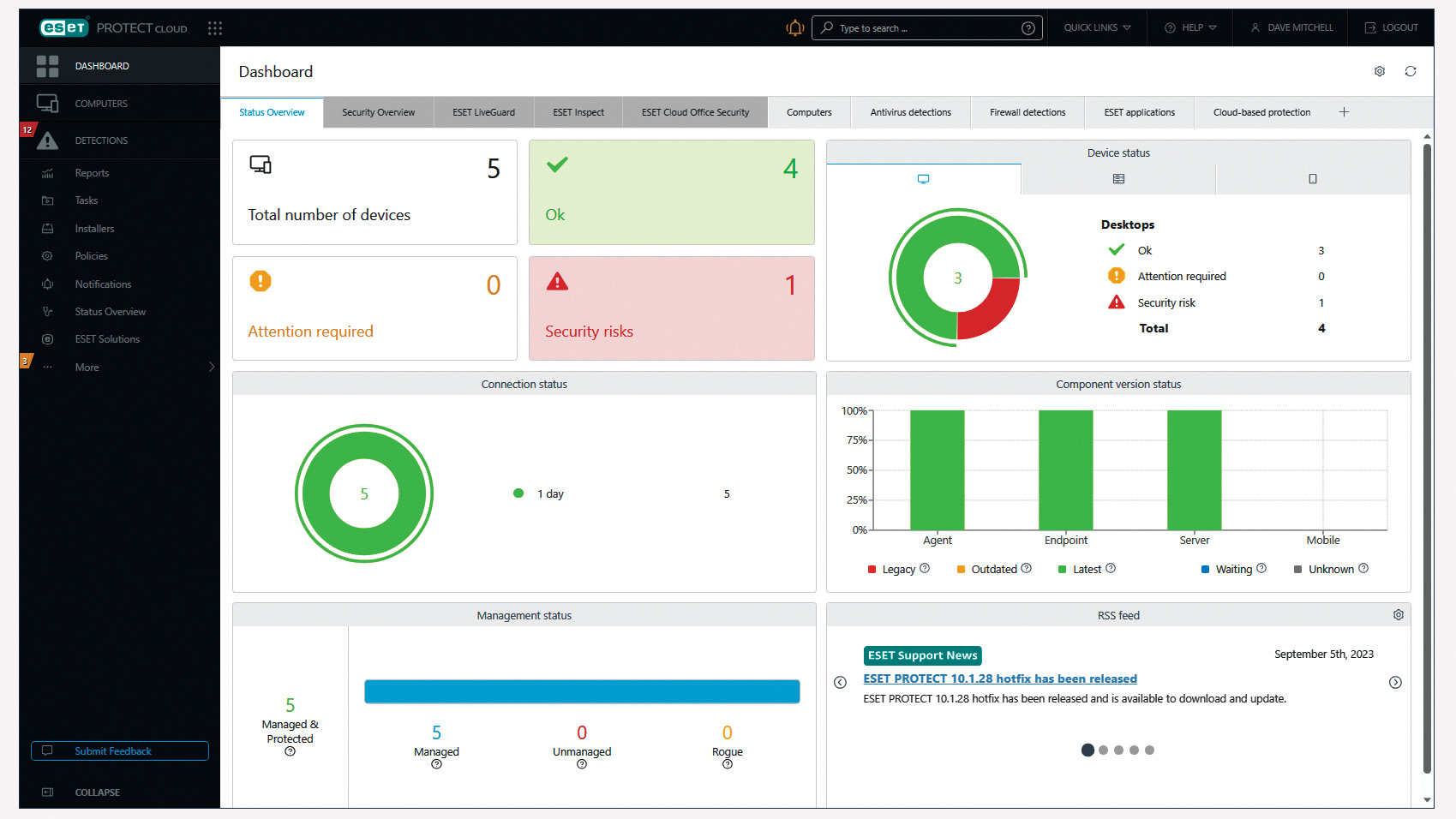 Eset Protect Cloud Advanced review: An impressive arsenal of endpoint protection features
Eset Protect Cloud Advanced review: An impressive arsenal of endpoint protection featuresReviews Policy management is complex, but Eset offers an affordable and flexible cloud-hosted solution
-
 Microsoft angers admins as April Patch Tuesday delivers password feature without migration guidance
Microsoft angers admins as April Patch Tuesday delivers password feature without migration guidanceNews Security fixes include a zero day exploited by a ransomware group and seven critical flaws
-
 A roadmap to Zero Trust with Cloudflare and CrowdStrike
A roadmap to Zero Trust with Cloudflare and CrowdStrikeWhitepaper Achieve end-to-end protection across endpoints, networks, and applications
-
 Microsoft's Windows Autopatch brings automated updates for IT admins
Microsoft's Windows Autopatch brings automated updates for IT adminsNews Endpoint Manager updates also include targeted IT messages for organisations and more security controls
-
 Microsoft unveils Defender for Business at Ignite 2021
Microsoft unveils Defender for Business at Ignite 2021News The new security suite is aimed at SMBs struggling to protect themselves in today's cyber security landscape
-
 Microsoft launches new layered group policy feature
Microsoft launches new layered group policy featureNews Layered feature makes it easier to selectively block USB devices in Windows
-
 Manufacturers shed light on Windows 11 compatibility
Manufacturers shed light on Windows 11 compatibilityNews Gigabyte, MSI and others specify which devices can natively support the operating system
-
 Microsoft rolls out Windows 10X-inspired May 2021 Update
Microsoft rolls out Windows 10X-inspired May 2021 UpdateNews Features such as containerising threats and a better voice typing experience make their way into the flagship OS

