Flipper Zero Review: Ubiquity in a small form factor
Tamagotchi meets communications wizardry in this cute little hackers' tool
-
+
Extensible
-
+
Easy to get started
-
+
Handy mobile apps
-
-
Pricey
-
-
Advanced features need expertise
- -
- -

Remember Tamagotchi, the nineties-era digital pet that delighted teens around the world? It was a simulator running on a small device that you'd carry around and digitally feed. If you didn't, it would eventually die. It was an experiment in anthropomorphic tech, showing the power of attributing personality to a simple software algorithm, but the program itself didn't do much more than act cute and demand to be fed.

Fast forward almost 30 years, and we have more powerful miniature electronics, along with small, powerful antennae. This led engineers Alex Kulagin and Pavel Zhovner to create a Tamagotchi-style device that geeks would actually find useful.
The Flipper Zero is a universal remote that scans, clones, and manipulates everything from infrared controls to NFC cards. It's a small package of powerful sensors and transmitters, governed by a smart collection of open-source applications. This has spawned a community of application and firmware developers. The product is designed with expandability in mind, containing GPIO pin-outs that have also inspired a collection of hardware add-ons.
Flipper Zero review: Getting started
The Flipper Zero arrives with a cute little sticker, a cursory getting started guide, and a cable to charge and update the device through its USB-C port. It won't do much until you insert a micro SD card to house the device's database and apps.
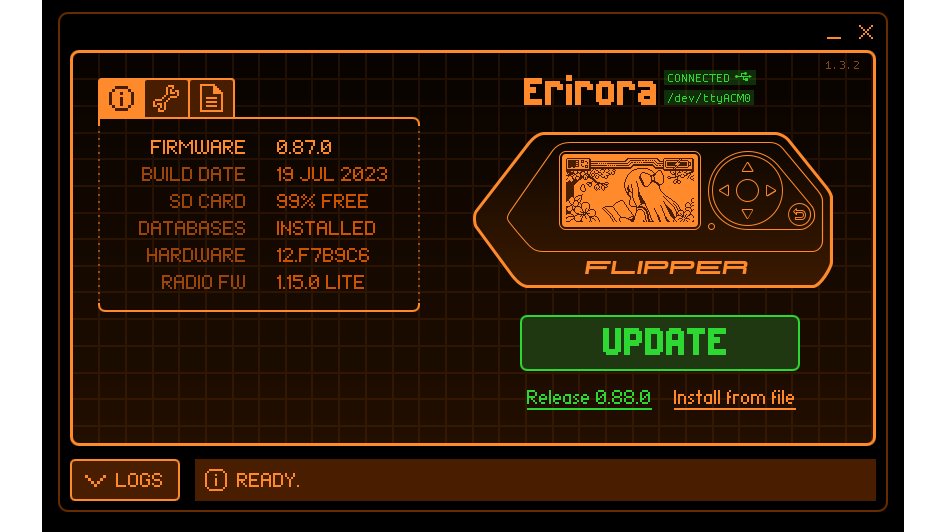
The first thing that users should do after inserting their card is update the firmware to the latest version. You'll need to connect with another device to manage the firmware download and installation. Flipper Zero offers two ways to do this. The first is to connect via a mobile app, which is available for iOS or Android. This uses Bluetooth to communicate with the device.
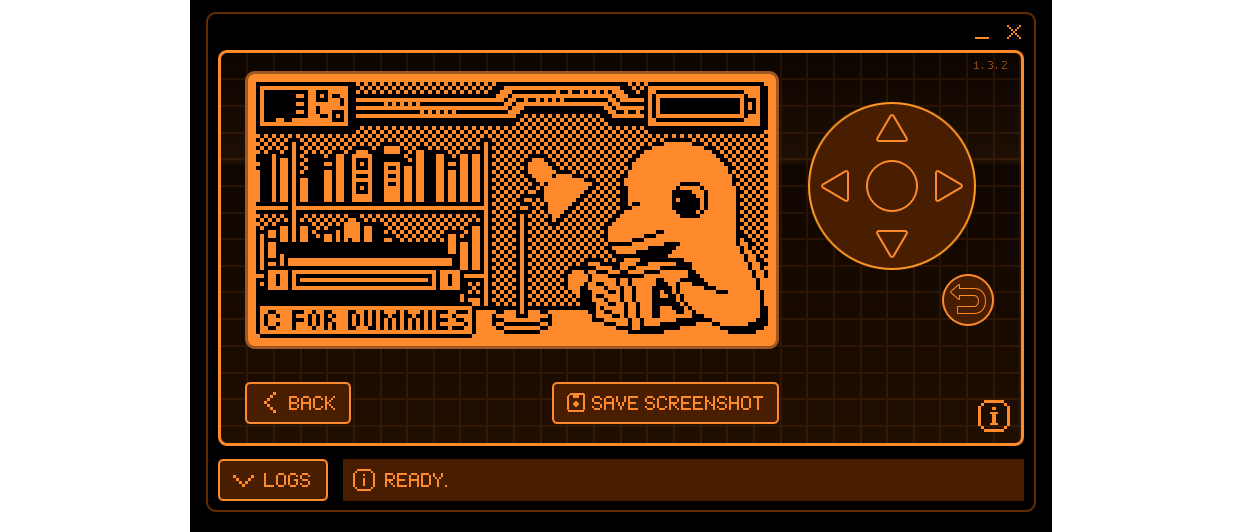
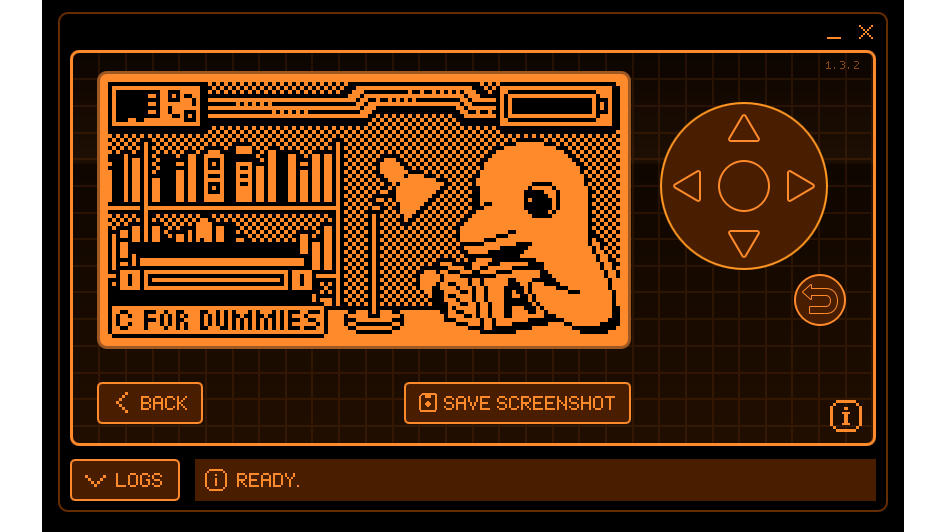
The alternative is qFlipper, which is a desktop app for controlling a USB-connected Flipper Zero. This is available for Windows, macOS, and Linux. It not only lets you update or repair firmware, but also presents a desktop version of the Flipper Zero's on-board interface that you can control remotely.
When you're controlling this on-board interface directly from the Flipper Zero, you manage it using the provided buttons, which support four-directional menu movements, a selection button, and a back button. Kulagin and Zhovner designed the device's interface well, packing a navigable system into an old-school LCD with a 128 x 64-pixel resolution.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
Flipper Zero review: Functions
So, what can you do with the Flipper Zero? The first thing most folks will try is the infrared transmitter. This lets you control a range of devices, from TVs to air conditioners. A universal remote will let you automatically cycle through basic signals like power buttons, trying all known combinations. This lets people with nothing better to do turn off other peoples' TVs automatically, much to the annoyance of bar owners and electronics store managers everywhere.
Cycling through hundreds of TV power signals takes a minute or two. For better performance the Flipper Zero can learn how to emulate your specific remote by placing it into learn mode, pointing the remote at it, and following the instructions. Alternatively, an iRDB GitHub provides hundreds of codes for dozens of device categories that you can download to your PC and then transfer to the Flipper Zero.
The Flipper Zero includes more advanced uses, including the reading, emulation, and cloning of NFC cards. It reads cards based on sub-specifications of the MIFARE standard. These include MIFARE Classic, which uses a cryptography standard called Crypto-1 that researchers cracked in 2008.
Even though there are now guides and keys available for MIFARE Classic cards, they are still among the most popular. There are millions of them, providing access to everything from gyms to hotel rooms. The Flipper Zero uses a dictionary attack based on known encryption keys to try and read sectors of a MIFARE Classic card. We read one, which turned out to be a MIFARE Classic Mini, and got four out of five sectors.

Even if you don't have all the card's sectors, you might still be able to authenticate with a reader in a poorly-secured system using just the card's UID. However, if the security system designers were more competent and the reader requires access to the card's sectors, the Flipper Zero can use another attack to try and fill in the gaps. This involves communicating with the reader directly and exploiting flaws in Crypto-1 to grab more keys.
The card can also read other frequencies, including 125Khz RFID chips, such as those found in key fobs and wristbands. You can also read the microchips that vets use to identify animals. There is a special option for these, as these chips operate outside the 125KHz band. This worked well on my rather confused dog once we found the chip.
The Flipper Zero can also read sub-GHz frequencies ranging from 300-928 MHz, commonly used to control gates, barriers, wireless doorbells, and your garage door. You'd typically want to add a Sub-1GHz remote that you already own using the Add Manually feature, which references a list of known protocols. This would create a virtual remote for on the Flipper Zero that you can then pair with your Sub-1GHz reader. There are also applications that can help those looking for mischief to brute force device keys.
The Flipper Zero also has built-in contact readers for iButton, a technology used for applications like building and security guard access. The Flipper Zero team developed its own custom contact pad for this. You can either read a key directly using this device, or enter its ID manually if you know it.
Once you tire of turning on the telly and trying to replicate your hotel room key with your Flipper Zero, you can use it as a security key for online access. Many websites use two-factor authentication, enabling you to specify another authentication factor alongside your password. This second factor is often a code sent to your phone that you then type into the website. This means only someone with your phone can log into the site.
Some sites lamentably still use SMS to send this code to your phone as the second factor, even though a spate of SIM jacking attacks prompted NIST to deprecate SMS as a second factor. Others use a more secure authenticator app on their phone, which still requires you to type in a one-time code. That's more secure but still inconvenient.
RELATED RESOURCE

Learn how endpoint management and endpoint security are converging, and what's influencing security strategies moving forward.
Security keys are the next step. Universal Second Factor (U2F) is a standard created by the FIDO Alliance. Instead of requiring you to type in a code, it stores asymmetric encryption key data that you can use to authenticate yourself on sites and browsers that support the standard.
When you register a security key with a site, logging in with your password will prompt a U2F authentication challenge. Pressing a button on the security key typically attached via a USB port – causes it to authenticate. It's another layer of security on an internet plagued with account takeovers.
The Flipper Zero comes with a U2F app that allows you to use it as a key. It takes just seconds to access U2F security options in your web service of choice (we used Google) and register the device, following instructions on its screen and pressing its button for confirmation. It worked like a charm when we came to log in using a different browser in which we didn't have a current OAUTH session for the site.
There's a caveat to this, though; the Flipper Zero is not a certified hardware-based device. That means that your keys are managed in software, not by a protected hardware layer. Flipper Zero's makers explicitly warn against using it for highly sensitive services like financial sites.
It's a shame that Flipper Zero didn't see fit to make the U2F function NFC-compatible, given the device's radio wizardry. U2F over NFC is a thing, and very useful for smartphone connections where you can't easily plug in a key via a USB port.
Still, on the upside the benefit of using the Flipper Zero as a USB-based U2F key is that you'll be encouraged to always plug it in when at your desk. That means it'll always be charged, although battery life won't typically be a problem with this device. It's designed to be left on (it even has a clock app) and a quick test saw it running for several days with plenty of battery life left. The default firmware shows the battery charge on the main animation screen.
There's another function that, like the card reader and emulator apps, could be used for good purposes or bad. BadUSB allows a connected Flipper Zero to act as a human interface device, like a keyboard. It then runs commands written in a scripting language called DuckyScript and saved as a file on the device. This means you can plug the Flipper Zero into a PC and have it do anything you like, as long as you have the appropriate credentials.
You can use this for all the nefarious purposes you'd expect, but you can also use it for good. While many people would be likely to use PowerShell, Python, or bash scripts to automate, one online user described how they used the device to automate large numbers of new machine setups. Neat.
Flipper Zero review: Expansion
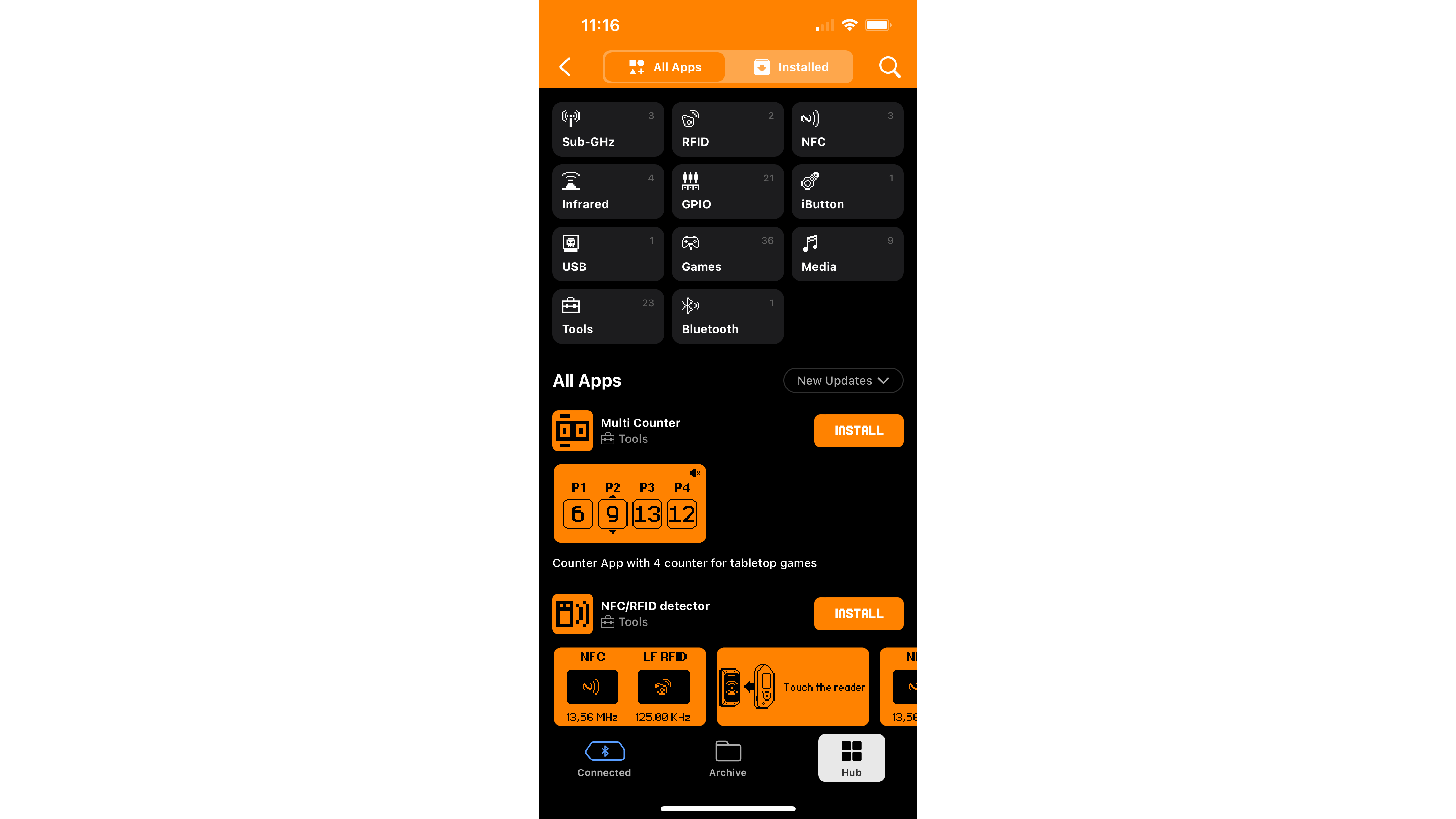
Perhaps the best part of the Flipper Zero is its extensibility. Aside from the GitHub repositories offering custom firmware, device datasets, and applications, the Flipper Zero mobile app now has an app store, enabling users to install a range of apps onto the device via Bluetooth. You can find everything from RFID fuzzers to Pomodoro timers and even card games, and installing them is a snap.
The GPIO pin-outs on the device also provide attractive hardware expansions, enabling third-party developers to create devices that bring new functionality. These include everything from magstripe emulators to Wi-Fi dev boards that enable you to run wireless network hacking tools. This can drastically increase the utility of an already impressive device.
Flipper Zero review: Conclusion
You might worry that the Flipper Zero could be used for crime, and you'd be right. A stalker that gets access to the iButton key for their target's building or apartment could be dangerous.
The Flipper Zero team specifically designed the firmware not to support rolling codes. Modern automobile fobs use these in sync with the vehicle as a form of a one-time pad, changing the access code each time. However, there is now at least one unofficial firmware version that has introduced support for rolling codes.
There are more hacking tools that offer more functionality than the Flipper Zero in specific areas like NFC hacking, but the appeal of this device is ubiquity in a small form factor. It can do so many things while remaining portable. However, you'll need to invest time and research to truly take advantage of this highly versatile little gem.
There will be three types of Flipper Zero users. The first will download a few cheeky apps and use it for pranks like opening the charging ports on random Teslas until it gets old. Then they'll leave it to sit on a shelf unused. The second will stall after accessing the basic features but will end up using it as a universal remote for stuff around the house, and perhaps as a U2F key.
The third kind of user will dive deeper into its functionality, using it as the basis for electronics projects by taking full advantage of its expandability. Expensive tools give you as much value as the effort you put into them, so if you're going to drop over a hundred bucks on one of these, make sure you're at least in the second category, and preferably the third.
Danny Bradbury has been a print journalist specialising in technology since 1989 and a freelance writer since 1994. He has written for national publications on both sides of the Atlantic and has won awards for his investigative cybersecurity journalism work and his arts and culture writing.
Danny writes about many different technology issues for audiences ranging from consumers through to software developers and CIOs. He also ghostwrites articles for many C-suite business executives in the technology sector and has worked as a presenter for multiple webinars and podcasts.
-
 ‘The inbox is no longer the only frontline’: Phishing attacks are evolving as cyber criminals ramp up ‘multi-channel’ campaigns over email and Microsoft Teams
‘The inbox is no longer the only frontline’: Phishing attacks are evolving as cyber criminals ramp up ‘multi-channel’ campaigns over email and Microsoft TeamsNews New research shows threat actors are ramping up “multi-channel” phishing attacks by combining lures via email and Microsoft Teams
By Ross Kelly Published
-
 Anthropic targets vulnerability detection gains with Claude Security public beta — here's what users can expect
Anthropic targets vulnerability detection gains with Claude Security public beta — here's what users can expectNews The Claude Mythos developer is aiming for a more limited approach to cyber tooling for public consumption
By Rory Bathgate Published
-
 AWS CEO Matt Garman is bullish on the future of SaaS — Amazon Quick shows there’s a ‘great business opportunity’ with AI-powered software
AWS CEO Matt Garman is bullish on the future of SaaS — Amazon Quick shows there’s a ‘great business opportunity’ with AI-powered softwareNews Matt Garman said fears over the ‘SaaSpocalypse’ were overblown in February, now AWS is making big moves in the SaaS space
By Ross Kelly Published
