Skip the three words thing, go straight for the ‘use a password manager, dammit’ jugular
Why you can do so much better than the three-random-word rule that’s still being churned out by the NCSC

Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
You are now subscribed
Your newsletter sign-up was successful
I’m about to so do something I’m sure won’t shock regular readers: pick an argument with the powers that be. The organisation in question, being the National Cyber Security Centre (NCSC) which, by and large, does a splendid job in both public and private sectors in matters of security advice and support. By and large, but not on one occasion recently when it decided the time was right to remind us of some password construction advice it first offered five years ago. It was wrong then and remains so to this day.
Using the perfectly reasonable hashtag of #thinkrandom, that advice was to use three random words as your password. That’s three words, not four, so you can forget about the XKCD comic suggestion of “correct, horse, battery, staple” that’s wedged itself into cyber security folklore. Not that you should use it anyway, as password reuse is obviously verboten if you want to maintain any semblance of a strong security posture.
The top 12 password-cracking techniques used by hackers
While admitting the use of three random words is “not a password panacea”, the latest NCSC posting serves to press home the message that it’s better than using traditional password complexity advice, because the latter relies upon us memorising lots of long and complex strings. Using three random words, we are advised, creates passwords that are “strong enough for many purposes”, and helps get around the reuse problem that it says traditional complex passwords creates.
Random access memories
Let’s deal with the last of these first: password reuse. There is absolutely no bloody difference between trying to remember 97 unique complex and random password strings and doing so with 97 three random word passphrases. You will fail unless you are a memory savant. That is a fact. It’s a fact because as humans we are simply not wired to remember random things.
This brings me to the second problem I have with the advice: the reality of randomness. Most people, most of the time, will choose three words that are far from random when constructing a whole bunch of passphrases. What people will do is, totally subconsciously, adopt patterns in the phrases they come up with. Patterns in both the connections between the words used to make recall easier and patterns between the passphrases themselves to make multiple ones easier to recall.
Humans just don’t do randomness well; that’s why there are computer-me-bobs for creating truly random stuff, and more on that later. There’s a really interesting piece of research from the University of Cambridge Computer Laboratory, admittedly now almost a decade old but still relevant, that explains this very well. Its evidence on multi-word passphrases was pretty damning: “By our metrics, even five-word phrases would be highly insecure against offline attacks,” the researchers found, because people naturally sway towards speech rather than randomness. “Phrases like young man which come up often in speech are proportionately more likely to be chosen than rare phrases like young table” the research concluded. Which is exactly what I would expect.
There’s an app for that
Look, I perfectly understand plenty of security professionals disagree with me here. Their argument generally being along the same lines as the NCSC, that adopting a three random words approach will create stronger passwords than those we often see being used and reused today. This is true, and I’m not suggesting that Password, or P@ssw0rd, or even P@ssw0rd1 is a super-duper credential to be using. What I am suggesting is that, rather than getting people to use three supposedly random words, it would be far better to advise them to use some form of secure password manager instead.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
Skip the whole three words thing, don’t mention it at all, go straight for the “use a password manager dammit” jugular. That way you can create truly random and complex and extremely long passwords, or the application can, and have a unique one for every login.
Of course, the perennial problem of master password creation rears its very ugly head once more. Rather than go over old ground involving muscle memory, encrypted USB sticks (which need yet another password) or a biometric device (JEMpass) and even dice with multiple patterns rolled randomly into a locked box (DiceKeys), let’s approach this from the three random words angle. Or, rather, let’s not. Just three words, no matter how random, would make a spectacularly poor master password if you ask me. Instead, go for five or six, or more if your memory will allow.
These would, of course, need to be random rather than your idea of random. Which is where one password manager, in fact 1Password, comes in. Did you see what I did there? Anyway, it has a password generator that anyone can use – which has the option of generating a passphrase using random words. Just select the “memorable password” dropdown, set the number of words to something you are comfortable with, and you’re away. Other services, of course, are also available, such as Kaspersky's own password generator.
As I say, don’t go for anything too short as this is the key that unlocks all your other passwords. I’d also avoid unchecking the “full words” box as this produces gibberish words that aren’t really easier than a long password to memorise. Practise typing the result over and over to get that muscle memory working, and if you are a 1Password user, be sure to save the “emergency kit” that can be printed out and stored somewhere secure. The reality is that for 99% of use cases a threat actor isn’t going to ransack your house searching for a master password, nor your office for that matter. If you do fall into the 1% then the chances are high that you’ll already be using some kind of security protocol that makes the entire three random words argument moot anyway.
Talking of passwords in the workplace, I can’t wrap up this conversation without mentioning some more research, this time from Beyond Identity. This found that not only did nearly a quarter of employees questioned still have access to accounts from a previous job, but 41% admitted to sharing passwords in the office, and 20% used the same passwords at home as they did for work-related accounts. Just in case you wondered why I bang on about the importance of password hygiene, month after month.
Davey is a three-decade veteran technology journalist specialising in cybersecurity and privacy matters and has been a Contributing Editor at PC Pro magazine since the first issue was published in 1994. He's also a Senior Contributor at Forbes, and co-founder of the Forbes Straight Talking Cyber video project that won the ‘Most Educational Content’ category at the 2021 European Cybersecurity Blogger Awards.
Davey has also picked up many other awards over the years, including the Security Serious ‘Cyber Writer of the Year’ title in 2020. As well as being the only three-time winner of the BT Security Journalist of the Year award (2006, 2008, 2010) Davey was also named BT Technology Journalist of the Year in 1996 for a forward-looking feature in PC Pro Magazine called ‘Threats to the Internet.’ In 2011 he was honoured with the Enigma Award for a lifetime contribution to IT security journalism which, thankfully, didn’t end his ongoing contributions - or his life for that matter.
You can follow Davey on Twitter @happygeek, or email him at davey@happygeek.com.
-
 Can we disrupt the data center designs?
Can we disrupt the data center designs?In-depth Distributed approaches or new power sources could enable data centers to grow with minimal harm to the environment
-
 Surging memory costs are scuppering digital transformation projects
Surging memory costs are scuppering digital transformation projectsNews Most organizations are already affected by memory cost increases, with no light at the end of the tunnel any time soon
-
 Blackpoint Cyber and NinjaOne partner to bolster MSP cybersecurity
Blackpoint Cyber and NinjaOne partner to bolster MSP cybersecurityNews The collaboration combines Blackpoint Cyber’s MDR expertise with NinjaOne’s automated endpoint management platform
-
 Busting nine myths about file-based threats
Busting nine myths about file-based threatsWhitepaper Distinguish the difference between fact and fiction when it comes to preventing file-based threats
-
 The Total Economic Impact™ of the Intel vPro® Platform as an endpoint standard
The Total Economic Impact™ of the Intel vPro® Platform as an endpoint standardWhitepaper Cost savings and business benefits enabled by the Intel vPro® Platform as an endpotnt standard
-
 The Total Economic Impact™ of IBM Security MaaS360 with Watson
The Total Economic Impact™ of IBM Security MaaS360 with WatsonWhitepaper Cost savings and business benefits enabled by MaaS360
-
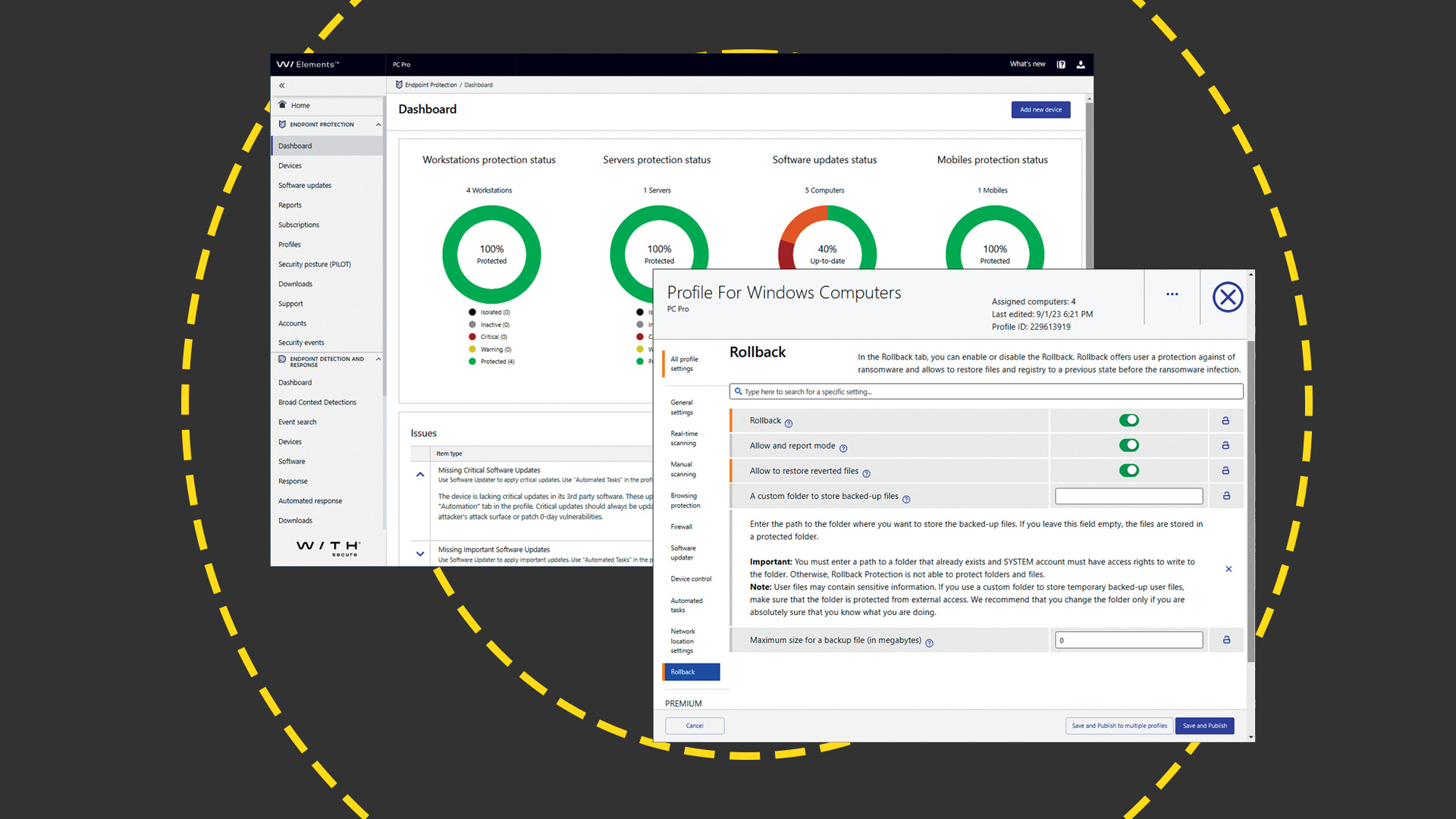 WithSecure Elements EPP and EDR review: Endpoint protection on a plate
WithSecure Elements EPP and EDR review: Endpoint protection on a plateReviews An affordable cloud-managed solution with smart automated remediation services
-
 KuppingerCole leadership compass report - Unified endpoint management (UEM) 2023
KuppingerCole leadership compass report - Unified endpoint management (UEM) 2023Whitepaper Get an updated overview of vendors and their product offerings in the UEM market.
-
 The Total Economic Impact™ of IBM Security MaaS360 with Watson
The Total Economic Impact™ of IBM Security MaaS360 with WatsonWhitepaper Get a framework to evaluate the potential financial impact of the MaaS360 on your organization
-
 Unified endpoint management software vendor assessment
Unified endpoint management software vendor assessmentWhitepaper Make positive steps on your intelligent automation journey
