QNAP warns of ransomware targeting internet-facing NAS products
The manufacturer has provided a guide to securing vulnerable products amid ongoing attacks


QNAP customers have been advised that cyber attackers are targeting its network-attached storage (NAS) products with ransomware and have been encouraged to secure their devices at the earliest opportunity.
Ransomware and brute-force cyber attacks have been "widely targeting" QNAP's internet-facing NAS products, according to the manufacturer which published a products security statement on Friday.
Best NAS drives 2023: Which network storage appliance is right for you? 12 wonderful uses for a NAS Can you put an SSD in a NAS?
NAS drives that are exposed to the internet without any protection are particularly vulnerable to the attacks and users are advised to revisit their security settings to ensure devices are adequately protected.
The scale of attacks is currently unclear and QNAP also didn't specify what strain of ransomware the attackers are using, or where the attackers are based. IT Pro has contacted QNAP for additional comment.
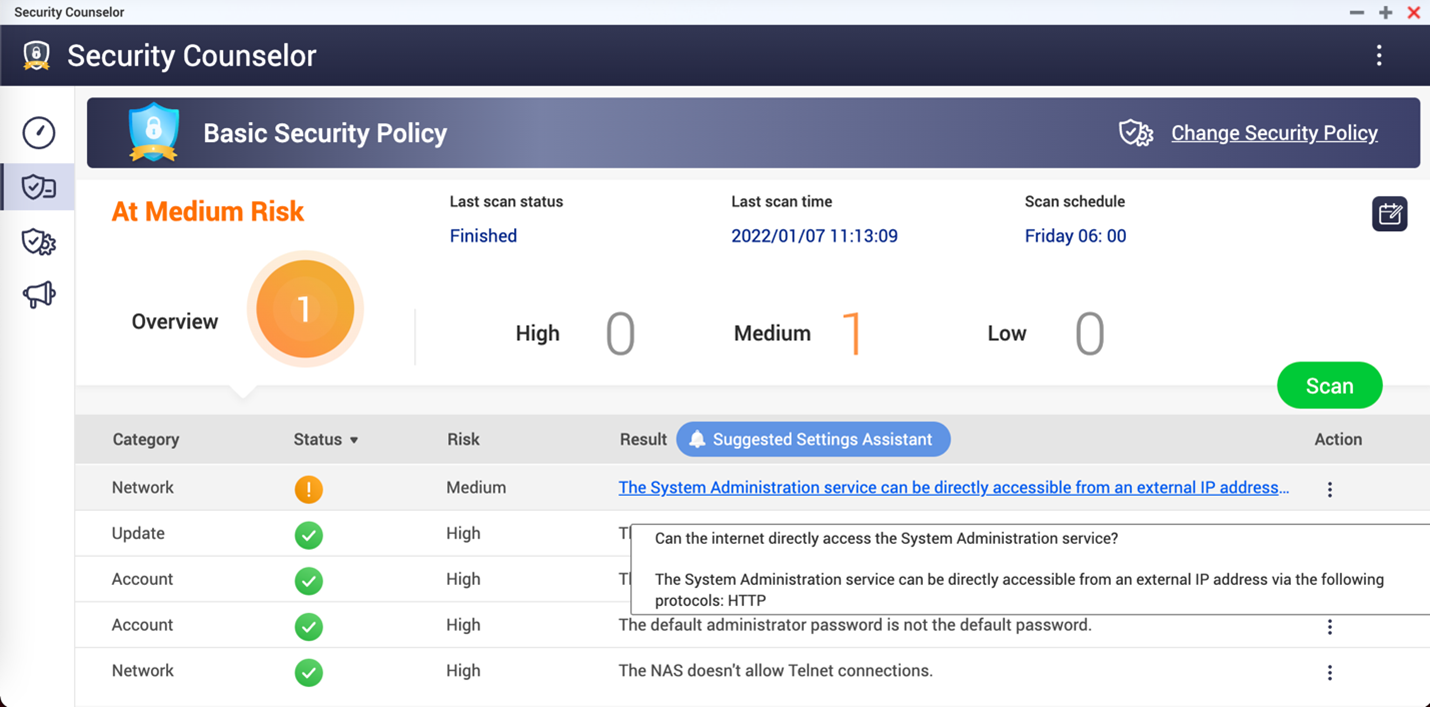
To check if a NAS drive is vulnerable to the attacks QNAP has observed, users should open the QNAP Security Counselor on their NAS products. The NAS is at high risk if there is an artefact that reads: 'The System Administration service can be directly accessible from an external IP address via the following protocols: HTTP' on the dashboard. QNAP also has a guide for users on how to check which ports on a router are exposed to the internet.
Securing the NAS
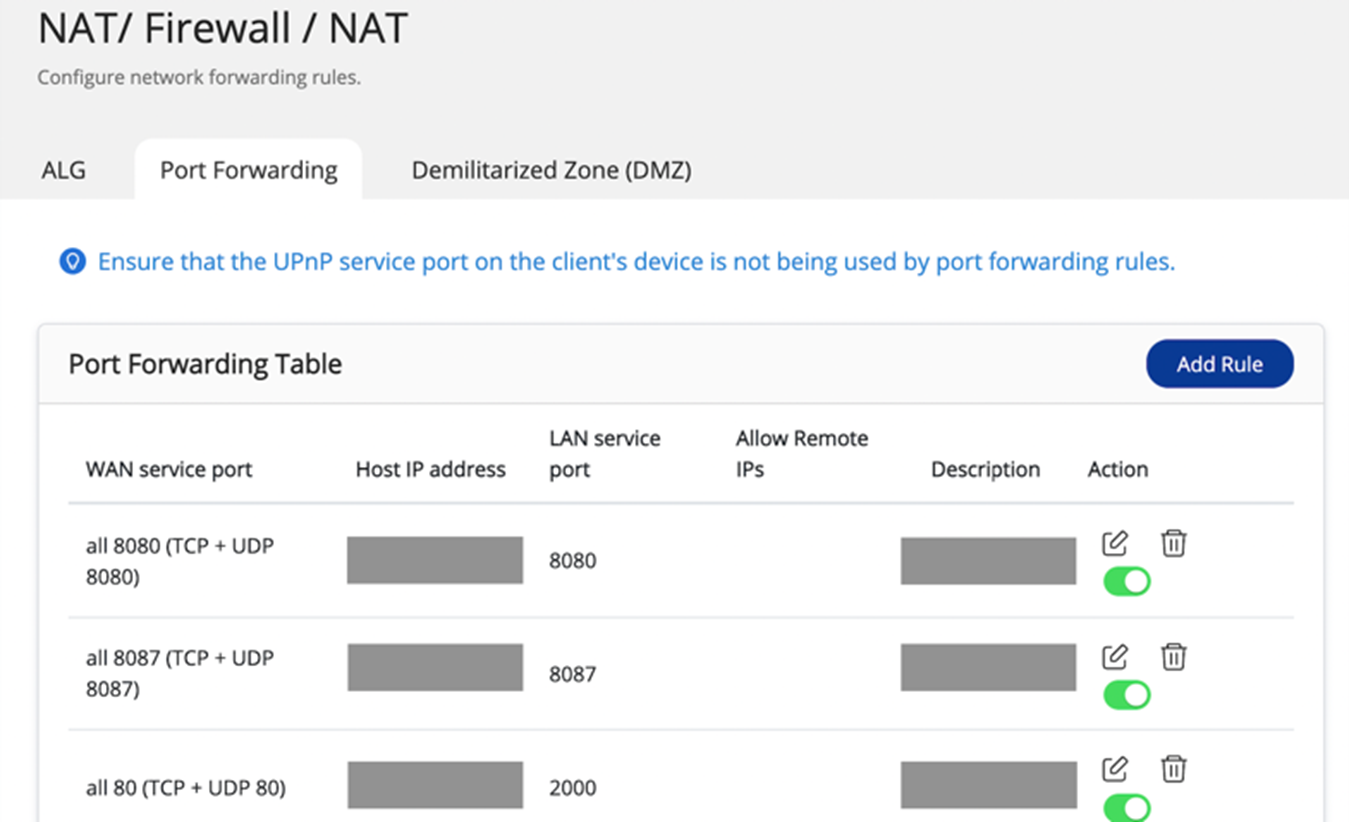
The first step to fully protect vulnerable products from the ongoing attacks is to disable the port forwarding function of the router. This can be completed via the management interface of a user's router. Users should check their settings and disable the port forwarding setting of NAS management service port which is set at port 8080 and 433 by default.
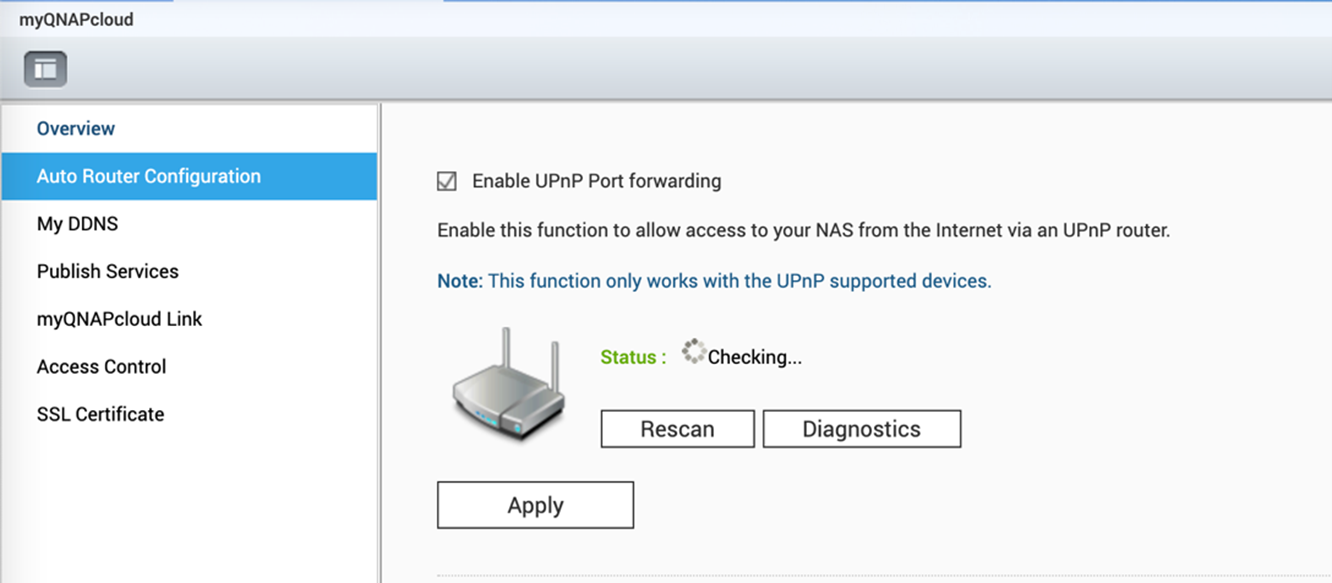
Users should finally disable the universal plug and play (UPnP) function of their QNAP NAS product in the QTS menu in myQNAPcloud. To do this, users can navigate to the 'Auto Route Configuration' tab in the QTS menu and unselect 'Enable UPnP Port forwarding'.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives

Connor Jones has been at the forefront of global cyber security news coverage for the past few years, breaking developments on major stories such as LockBit’s ransomware attack on Royal Mail International, and many others. He has also made sporadic appearances on the ITPro Podcast discussing topics from home desk setups all the way to hacking systems using prosthetic limbs. He has a master’s degree in Magazine Journalism from the University of Sheffield, and has previously written for the likes of Red Bull Esports and UNILAD tech during his career that started in 2015.
-
 European Commission opens public consultation on draft for high-risk AI guidelines
European Commission opens public consultation on draft for high-risk AI guidelinesNews Guidance aims to help organizations and regulators decide whether their AI products and deployments need to conform to tougher rules
-
 Microsoft reveals Surface Pro and Surface Laptop for Business
Microsoft reveals Surface Pro and Surface Laptop for BusinessNews New 13in Pro and Laptop claim big performance improvements and vast AI capabilities
-
 Instructure chose to a pay ransom following the Canvas cyber attack – research shows more than half of security leaders would follow suit
Instructure chose to a pay ransom following the Canvas cyber attack – research shows more than half of security leaders would follow suitAnalysis Opting to pay ransoms creates huge risks for enterprises – you’re relying on the word of criminals
-
 Ransomware negotiator sentenced for role in major cyber crime group
Ransomware negotiator sentenced for role in major cyber crime groupNews Deniss Zolotarjovs was a key player in a group associated with Conti
-
 Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitation
Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitationNews A dip in ransomware volumes points to a more targeted approach focused on vulnerability exploitation
-
 Security leaders overconfident about ransomware recovery
Security leaders overconfident about ransomware recoveryNews Few manage to recover all their data, and many experience business disruption
-
 German authorities want your help finding the hackers behind GandCrab and REvil
German authorities want your help finding the hackers behind GandCrab and REvilNews Daniil Maksimovich Shchukin and Anatoly Sergeevitsch Kravchuk are believed to have made millions from ransomware as a service schemes
-
 The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in life
The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in lifeNews With family responsibilities and mortgages to pay, it's not teenagers dishing out malware or carrying out cyber extortion
-
 Ransomware gangs are using employee monitoring software as a springboard for cyber attacks
Ransomware gangs are using employee monitoring software as a springboard for cyber attacksNews Two attempted attacks aimed to exploit Net Monitor for Employees Professional and SimpleHelp
-
 Ransomware gangs are sharing virtual machines to wage cyber attacks on the cheap – but it could be their undoing
Ransomware gangs are sharing virtual machines to wage cyber attacks on the cheap – but it could be their undoingNews Thousands of attacker servers all had the same autogenerated Windows hostnames, according to Sophos
