IoT security measures 'need teeth' to counter the spread of hackable devices
Tech industry reacts to Whitehall review's IoT security recommendations

The UK government's publication of guidelines to make connected devices more secure has been welcomed by industry experts, who nevertheless say Whitehall's review could have done more to set a higher standard for IoT security.
The 13 recommendations made by the Department for Digital, Culture, Media and Sport yesterday sets out to encourage IoT vendors to make security part of the design process rather than bolting it on as an afterthought.
Measures the government has urged manufacturers to include cover regular software updates to devices to prevent hackers exploiting code-level flaws, getting rid of default passwords, and warning customers when they become aware of a vulnerability in a product.
However, the report's guidelines are not compulsory, and some experts have pointed out where they believe the review could have gone further.
'No teeth'
David Emm, who is the principal security researcher at Kaspersky Lab, feels that the guidelines lack bite, and on their own will not solve the problem of unsecured, hackable devices falling into the hands of unwitting consumers.
He believes developers need to take more responsibility when it comes to protecting devices, by including safety certificates to show their products meet the government's voluntary standards.
"If the government allows manufacturers who comply with the standards to display a clearly-visible mark like the British Standards Institute kitemark, it would provide an easy way for consumers to tell if something is safe, putting manufacturers who don't comply at a disadvantage."
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
He added: "One government's guidelines, unless they have teeth, won't solve the problem entirely."
Telemetry data collection risks users' privacy
In a more detailed assessment, Bill Evans, senior director at security vendor One Identity, expressed concerns regarding the 10th recommendation for monitoring system telemetry data and what it is specifically used for.
Calling the review as a whole "a great step forward", Evans warned that this specific recommendation creates potential for an invasion of privacy.
The recommendation states that "if collected, all telemetry such as usage and measurement data from IoT devices and services should be monitored for security anomalies within it".
But Evans called for more clarity "to ensure limitations on abuse", by allowing users to turn off telemetry data collection, or defining what data that encompasses.
"The risk here is that the device manufacturers and service providers begin collecting lots of the data 'in the name of security' that really is usage data that can conveniently also be used for marketing or other purposes," he argued. "By scoping this recommendation, the framers of this guidance could eliminate this concern once and for all."
Hackers see connected devices as 'entry points' to personal data
The variety of internet-connected devices on the market provides countless opportunities for hackers to access individual and corporate data, from IoT toys that let hackers talk to children to webcams used to spy on people caught unawares.
Emily Orton, co-founder at Darktrace, feels there is still much more to be done to protect ourselves when it comes to IoT devices.
"We're now seeing hackers taking a variety of different pieces of information with a considerable amount coming from corporate targets. So, for example, we have recently seen a fish tank used to take out sensitive corporate data from a casino." The tank was connected to a PC that enabled hackers to get onto the casino's network.
"So, you may think 'why would anyone want to hack my fitness tracking device or my baby monitor?'," she added, "but they may be used as gateways to more interesting things. We need to think about where these devices are travelling and which servers and devices they may be acting as a stepping stone to, to get other information."
Taking the security burden off consumers
The government's review highlighted the need for more clarity for consumers on the need to use secure IoT devices, and to remove the burden from them of securing these devices in the first place.
Mark James, security specialist at antivirus firm ESET, welcomed this point, and emphasised that users unaware of the existence of security threats mean vendors must take on the burden of building in security themselves.
"One of the biggest issues for the consumer is knowing they need protecting and just as important, understanding what they need protecting from," James pointed out. "It's not always easy to get this across, so, if we can implement measures from the ground up to take some of the decisions away from the user and have them 'auto' or 'default', then achieving that security will certainly be much easier."
Highlighting the threats of default passwords and an absence of firmware updates to protect against hacking, he added: "The end user often does not understand the need to close these massive fissures in IoT security, so if given the choice will often go for price over security."
This likelihood means James fears that, with the review's measures currently acting only as recommendations, this uneasy tension between security and cost could prove a stumbling block in making IoT devices safer.
"Ensuring something is easy to install, reasonably priced and secure at the same time may not be as simple as it sounds," he said.
Bobby Hellard is ITPro's Reviews Editor and has worked on CloudPro and ChannelPro since 2018. In his time at ITPro, Bobby has covered stories for all the major technology companies, such as Apple, Microsoft, Amazon and Facebook, and regularly attends industry-leading events such as AWS Re:Invent and Google Cloud Next.
Bobby mainly covers hardware reviews, but you will also recognize him as the face of many of our video reviews of laptops and smartphones.
-
 Enterprises are slacking on MySQL database security, and it could come back to haunt them
Enterprises are slacking on MySQL database security, and it could come back to haunt themNews Poor database security practices are leaving organizations at huge risk of compromise
-
 OpenAI ramps up enterprise AI push with new consultancy launch
OpenAI ramps up enterprise AI push with new consultancy launchNews The launch of the OpenAI Deployment Company comes with £4bn investment to help speed up enterprise Ai adoption
-
 Blackpoint Cyber and NinjaOne partner to bolster MSP cybersecurity
Blackpoint Cyber and NinjaOne partner to bolster MSP cybersecurityNews The collaboration combines Blackpoint Cyber’s MDR expertise with NinjaOne’s automated endpoint management platform
-
 Busting nine myths about file-based threats
Busting nine myths about file-based threatsWhitepaper Distinguish the difference between fact and fiction when it comes to preventing file-based threats
-
 The Total Economic Impact™ of the Intel vPro® Platform as an endpoint standard
The Total Economic Impact™ of the Intel vPro® Platform as an endpoint standardWhitepaper Cost savings and business benefits enabled by the Intel vPro® Platform as an endpotnt standard
-
 The Total Economic Impact™ of IBM Security MaaS360 with Watson
The Total Economic Impact™ of IBM Security MaaS360 with WatsonWhitepaper Cost savings and business benefits enabled by MaaS360
-
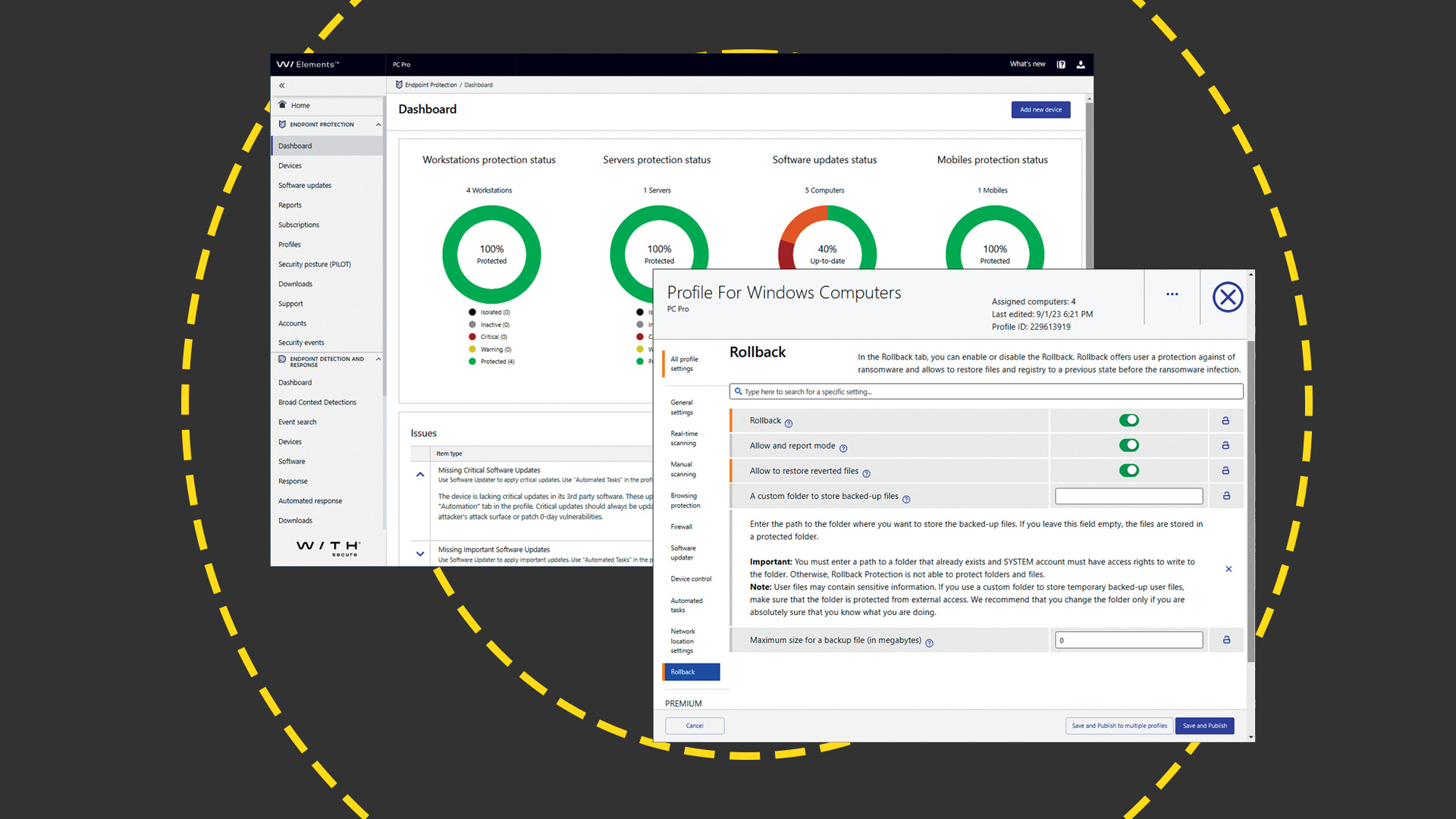 WithSecure Elements EPP and EDR review: Endpoint protection on a plate
WithSecure Elements EPP and EDR review: Endpoint protection on a plateReviews An affordable cloud-managed solution with smart automated remediation services
-
 KuppingerCole leadership compass report - Unified endpoint management (UEM) 2023
KuppingerCole leadership compass report - Unified endpoint management (UEM) 2023Whitepaper Get an updated overview of vendors and their product offerings in the UEM market.
-
 The Total Economic Impact™ of IBM Security MaaS360 with Watson
The Total Economic Impact™ of IBM Security MaaS360 with WatsonWhitepaper Get a framework to evaluate the potential financial impact of the MaaS360 on your organization
-
 Unified endpoint management software vendor assessment
Unified endpoint management software vendor assessmentWhitepaper Make positive steps on your intelligent automation journey

