Cyber criminals are spending longer inside business' networks after the initial breach
Cyber attackers' dwell time is up 36% thanks to initial access brokers and repeat exploitation of Microsoft Exchange vulnerabilities, according to Sophos

Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
You are now subscribed
Your newsletter sign-up was successful
Cyber attackers are spending longer inside business systems after hacking them, a new report has revealed.
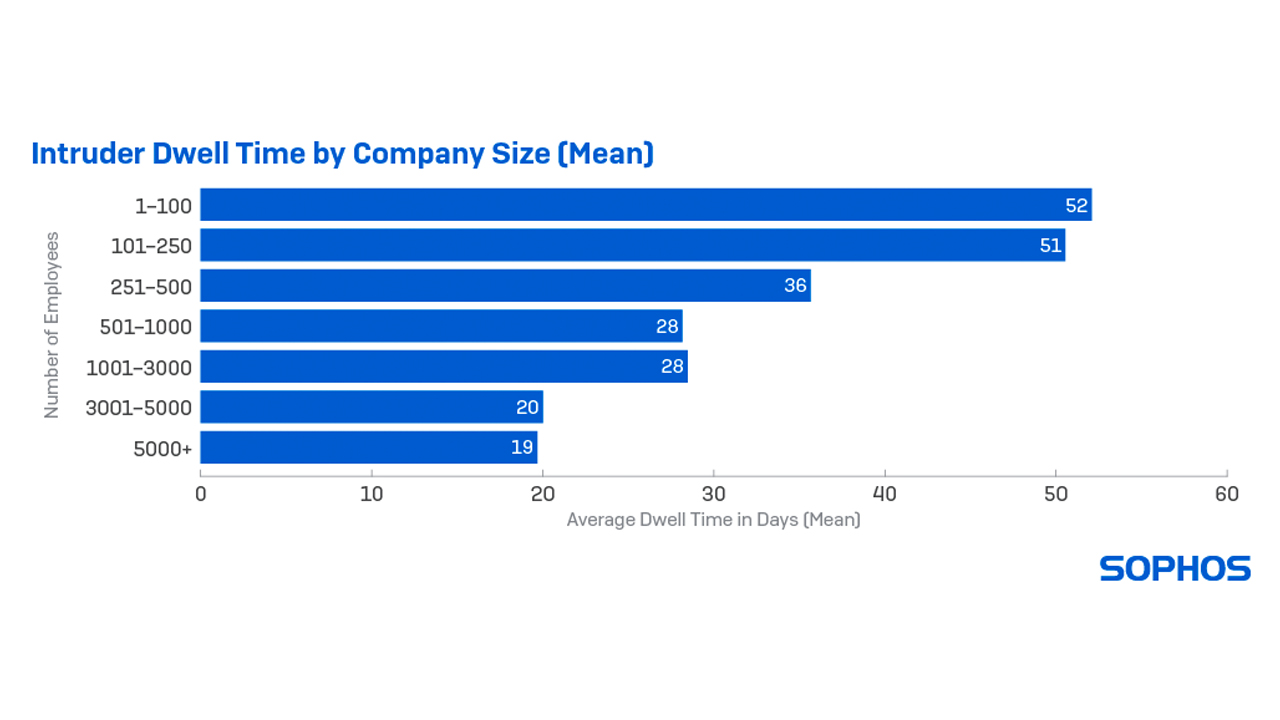
Rogue actors who do not use ransomware are spending the most time inside small businesses with the average dwell time observed to be 51 days in organisations with fewer than 250 employees. Attackers targeting larger (3,000 - 5,000 employees) organisations spend on average just 20 days inside.
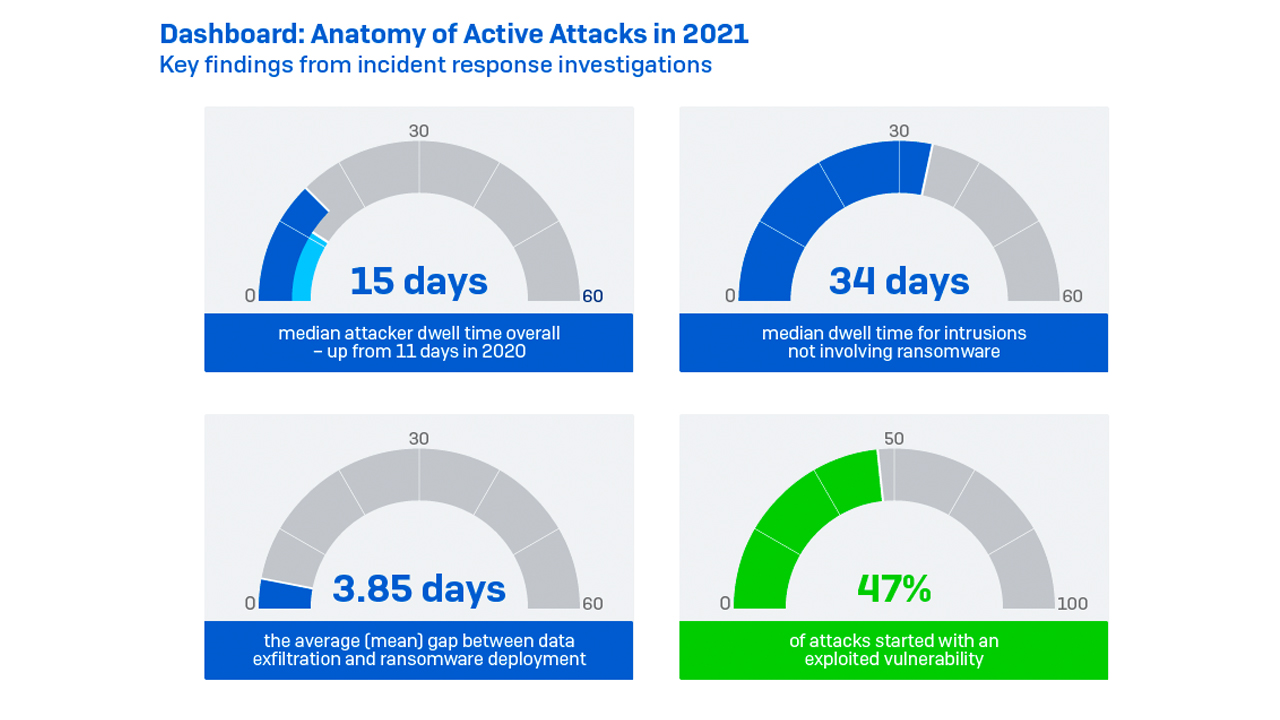
The figures for ransomware criminals are much lower, with the average dwell time inside a business falling to just 15 days.
UK cyber security firm Sophos said these figures, taken from data in 2021, amount to a 36% increase in attacker dwell time compared to the previous year.
Longer dwell times could be indicative of the increasing popularity of initial access brokers (IABs) in the cyber security landscape, the company said.
IABs are online services that are often sold on the deep web selling remote access to companies to prospective hackers and charging them according to the time spent inside the system.
Longer dwell times not only allow attackers to launch more attacks but also open up victims to attacks from multiple threat actors, Sophos said.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
The company’s forensic analyses revealed instances of IABs, cryptominers, and multiple ransomware operators targeting businesses simultaneously.
Sophos said this growing trend of hackers simply paying for access rather than developing their exploits, for example, reflects the growing ‘professionalism’ of cyber attackers and is fuelling a thriving ransomware-as-a-service (RaaS) market.
RELATED RESOURCE
The Total Economic Impact™ of Mimecast
Cost savings and business benefits enabled by using Mimecast with Microsoft 365
FREE DOWNLOAD
“The world of cybercrime has become incredibly diverse and specialised. IABs have developed a cottage cybercrime industry by breaching a target, doing exploratory reconnaissance or installing a backdoor, and then selling the turn-key access to ransomware gangs for their own attacks,” said John Shier, senior security advisor at Sophos.
“In this increasingly dynamic, speciality-based cyberthreat landscape, it can be hard for organisations to keep up with the ever-changing tools and approaches attackers use. It is vital that defenders understand what to look for at every stage of the attack chain, so they can detect and neutralise attacks as fast as possible.”
In addition to the pervasive reliance on IABs, Sophos’ analysis of cyber attacks revealed that the second of the most influential threats was the continued exploitation of the ProxyLogon and ProxyShell vulnerabilities in Microsoft Exchange servers.
Microsoft said this week that it had to delay the development of the next version of Microsoft Exchange by four years due to assigning so many experts to improve the security of the mail and calendaring service in the wake of mass exploitation last year.
Sophos said the bugs led to a significant number of incidents it saw during 2021 and that there are likely to be many related breaches of which businesses are still unaware.
The implantation of web shells and backdoors is likely to go unnoticed and the access they provide may later be sold to willing bidders in the IAB market, it said.
Other wider findings in the company’s Active Adversary Playbook report revealed that data exfiltration was far more common in ransomware incidents than in previous years, with the average time taken for actors to pull data from victims dropping from 4.28 to 1.84 days.
The trend speaks to the growing trend in ransomware of double extortion - a method which sees the victim’s systems corrupted, as well as data stolen with the threat of data leakage if the ransom isn’t paid.

Connor Jones has been at the forefront of global cyber security news coverage for the past few years, breaking developments on major stories such as LockBit’s ransomware attack on Royal Mail International, and many others. He has also made sporadic appearances on the ITPro Podcast discussing topics from home desk setups all the way to hacking systems using prosthetic limbs. He has a master’s degree in Magazine Journalism from the University of Sheffield, and has previously written for the likes of Red Bull Esports and UNILAD tech during his career that started in 2015.
-
 Cohere's Aleph Alpha merger could create a transatlantic sovereign AI powerhouse
Cohere's Aleph Alpha merger could create a transatlantic sovereign AI powerhouseAnalysis The merger between Cohere and Aleph Alpha aims to capitalize on the burgeoning sovereign AI market
-
 Everything you need to know about OpenAI's new workspace agents
Everything you need to know about OpenAI's new workspace agentsNews New ‘workspace agents’ from OpenAI will automate tasks for workers and can be customized for specific roles
-
 Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitation
Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitationNews A dip in ransomware volumes points to a more targeted approach focused on vulnerability exploitation
-
 Security leaders overconfident about ransomware recovery
Security leaders overconfident about ransomware recoveryNews Few manage to recover all their data, and many experience business disruption
-
 German authorities want your help finding the hackers behind GandCrab and REvil
German authorities want your help finding the hackers behind GandCrab and REvilNews Daniil Maksimovich Shchukin and Anatoly Sergeevitsch Kravchuk are believed to have made millions from ransomware as a service schemes
-
 The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in life
The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in lifeNews With family responsibilities and mortgages to pay, it's not teenagers dishing out malware or carrying out cyber extortion
-
 Ransomware gangs are using employee monitoring software as a springboard for cyber attacks
Ransomware gangs are using employee monitoring software as a springboard for cyber attacksNews Two attempted attacks aimed to exploit Net Monitor for Employees Professional and SimpleHelp
-
 Ransomware gangs are sharing virtual machines to wage cyber attacks on the cheap – but it could be their undoing
Ransomware gangs are sharing virtual machines to wage cyber attacks on the cheap – but it could be their undoingNews Thousands of attacker servers all had the same autogenerated Windows hostnames, according to Sophos
-
 Google issues warning over ShinyHunters-branded vishing campaigns
Google issues warning over ShinyHunters-branded vishing campaignsNews Related groups are stealing data through voice phishing and fake credential harvesting websites
-
 The FBI has seized the RAMP hacking forum, but will the takedown stick? History tells us otherwise
The FBI has seized the RAMP hacking forum, but will the takedown stick? History tells us otherwiseNews Billing itself as the “only place ransomware allowed", RAMP catered mainly for Russian-speaking cyber criminals