Microsoft launches Secured-core servers to combat ransomware
Previously debuting on Windows PCs in 2019, the Secured-core initiative has reached servers in a bid to better protect infrastructure from cyber attacks like ransomware


Microsoft has expanded its Secured-core PC initiative to its server products in a bid to combat ransomware attacks on infrastructure.
Secured-core will now be expanded to reach Windows Server, Microsoft Azure Stack HCI, and Azure-certified IoT devices.
Businesses can search for Secured-core servers in the Azure Stack HCI and Windows Server online catalogues. There are currently four all-HPE products that run Azure Stack HCI and 42 options from a variety of vendors that meet the Windows Server spec.
All servers come “fully equipped with industry-leading security mitigations built into the hardware, firmware, and the operating system to help thwart some of the most advanced attack vectors,” Microsoft said.
Secured-core servers are built around three distinct security pillars:
- To protect the server infrastructure with a hardware-based root of trust
- To defend sensitive workloads against firmware-level attacks
- To prevent access and the execution of unverified code on the systems
“Partnering with leading original equipment manufacturers (OEMs) and silicon vendors, Secured-core servers use industry-standard hardware-based root of trust coupled with security capabilities built into today’s modern central processing units (CPUs),” said Microsoft in a blog post.
“Secured-core servers use the Trusted Platform Module 2.0 and Secure boot to ensure that only trusted components load in the boot path.”
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
It’s thought the new hardware will help tackle specific parts of ransomware attacks and help detect intrusions earlier, with the hope that attacks can be mitigated before any real damage is done.
Microsoft used a typical REvil ransomware kill chain as an example. REvil was one of the most prolific ransomware gangs of 2021 before it shuttered following a string of arrests of alleged REvil associates.
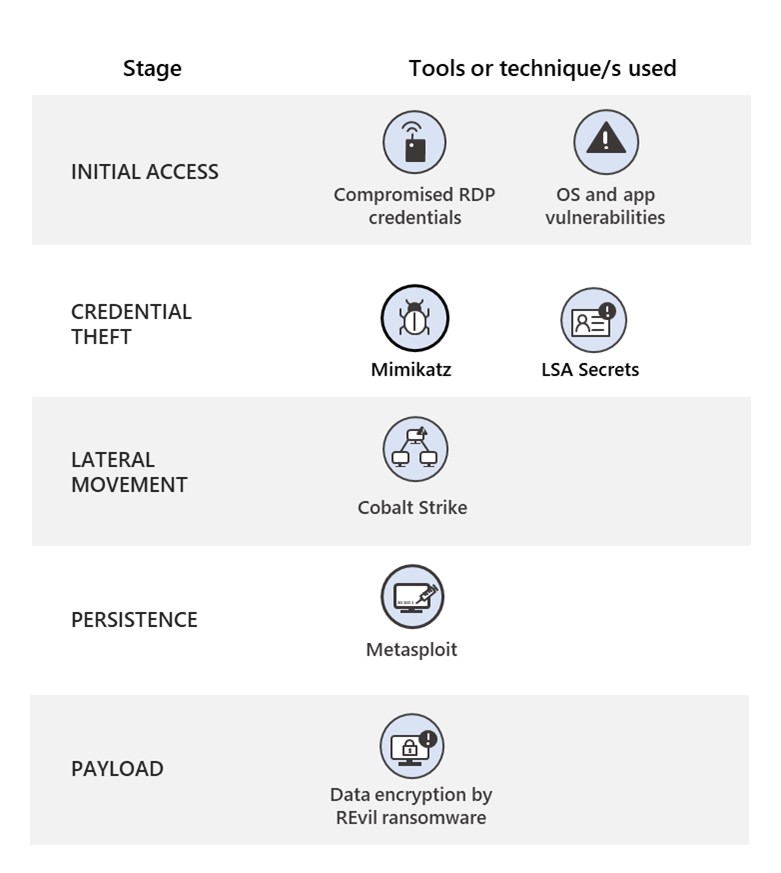
Using the kill chain used by REvil on Kaseya earlier this year, Microsoft explained that certain features in Secured-core servers like Hypervisor-protected Code Integrity (HVCI) can block drivers that tamper with the kernel, like with Mimikatz, via a code integrity security policy.
By preventing credential theft, an early stage of the ransomware kill chain, Microsoft said Secured-core server can make it very difficult for attackers to move laterally around a potential victim’s network.
RELATED RESOURCE
How to reduce the risk of phishing and ransomware
Top security concerns and tips for mitigation
“Continuing to raise the security bar for critical infrastructure against attackers makes it easier for organisations to meet that higher bar, which is an important priority for both customers and Microsoft,” said Microsoft.
“Successfully protecting systems requires a holistic approach that builds security from the chip to the cloud across hardware, firmware, and the operating system.”
Microsoft debuted the Secured-core initiative in 2019 on Windows PCs which saw computers ship with enhanced security measures at the hardware level.
The machines were designed for business use, with the financial services and healthcare industries targeted specifically, as well as anyone working in a high-value-data role such as in government.

Connor Jones has been at the forefront of global cyber security news coverage for the past few years, breaking developments on major stories such as LockBit’s ransomware attack on Royal Mail International, and many others. He has also made sporadic appearances on the ITPro Podcast discussing topics from home desk setups all the way to hacking systems using prosthetic limbs. He has a master’s degree in Magazine Journalism from the University of Sheffield, and has previously written for the likes of Red Bull Esports and UNILAD tech during his career that started in 2015.
-
 Changes to EU AI Act implementation deadlines welcomed by industry
Changes to EU AI Act implementation deadlines welcomed by industryNews New implementation deadlines for the EU AI Act could help remove “genuine friction” for European companies
-
 What businesses need to know about the update to Cyber Essentials
What businesses need to know about the update to Cyber EssentialsIn-depth Cyber Essentials was updated this April – what are the key changes?
-
 Ransomware negotiator sentenced for role in major cyber crime group
Ransomware negotiator sentenced for role in major cyber crime groupNews Deniss Zolotarjovs was a key player in a group associated with Conti
-
 Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitation
Threat actors ditch ‘spray and pray’ attacks in shift to targeted exploitationNews A dip in ransomware volumes points to a more targeted approach focused on vulnerability exploitation
-
 Security leaders overconfident about ransomware recovery
Security leaders overconfident about ransomware recoveryNews Few manage to recover all their data, and many experience business disruption
-
 German authorities want your help finding the hackers behind GandCrab and REvil
German authorities want your help finding the hackers behind GandCrab and REvilNews Daniil Maksimovich Shchukin and Anatoly Sergeevitsch Kravchuk are believed to have made millions from ransomware as a service schemes
-
 The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in life
The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in lifeNews With family responsibilities and mortgages to pay, it's not teenagers dishing out malware or carrying out cyber extortion
-
 Ransomware gangs are using employee monitoring software as a springboard for cyber attacks
Ransomware gangs are using employee monitoring software as a springboard for cyber attacksNews Two attempted attacks aimed to exploit Net Monitor for Employees Professional and SimpleHelp
-
 Ransomware gangs are sharing virtual machines to wage cyber attacks on the cheap – but it could be their undoing
Ransomware gangs are sharing virtual machines to wage cyber attacks on the cheap – but it could be their undoingNews Thousands of attacker servers all had the same autogenerated Windows hostnames, according to Sophos
-
 Google issues warning over ShinyHunters-branded vishing campaigns
Google issues warning over ShinyHunters-branded vishing campaignsNews Related groups are stealing data through voice phishing and fake credential harvesting websites
