Why UEM is the key to enterprise IT security
A guide to effective endpoint security


With IDC stating that 70% of data breaches begin with endpoints, enterprises are scrambling to secure and safeguard them - from servers to remote mobile devices - to keep their network safe from cyberattacks and secure the data stored within.
This whitepaper comprehensively explores unified endpoint management (UEM) as a security solution, offering context, implementation challenges, the threat of ransomware, and best practices for effective endpoint security.
Download it now to learn how to effectively secure all your endpoints to keep your data and network safe.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
ITPro is a global business technology website providing the latest news, analysis, and business insight for IT decision-makers. Whether it's cyber security, cloud computing, IT infrastructure, or business strategy, we aim to equip leaders with the data they need to make informed IT investments.
For regular updates delivered to your inbox and social feeds, be sure to sign up to our daily newsletter and follow on us LinkedIn and Twitter.
-
 Developers warned to avoid 'early-access' Google Gemini tools
Developers warned to avoid 'early-access' Google Gemini toolsNews Attackers are tempting would-be users into downloading reverse shell malware
-
 Researchers warn millions of RDP and VNC servers are wide open to exploitation
Researchers warn millions of RDP and VNC servers are wide open to exploitationNews Researchers at Forescout spotted millions of RDP and VNC servers exposed online
-
 Blackpoint Cyber and NinjaOne partner to bolster MSP cybersecurity
Blackpoint Cyber and NinjaOne partner to bolster MSP cybersecurityNews The collaboration combines Blackpoint Cyber’s MDR expertise with NinjaOne’s automated endpoint management platform
-
 Busting nine myths about file-based threats
Busting nine myths about file-based threatsWhitepaper Distinguish the difference between fact and fiction when it comes to preventing file-based threats
-
 The Total Economic Impact™ of the Intel vPro® Platform as an endpoint standard
The Total Economic Impact™ of the Intel vPro® Platform as an endpoint standardWhitepaper Cost savings and business benefits enabled by the Intel vPro® Platform as an endpotnt standard
-
 The Total Economic Impact™ of IBM Security MaaS360 with Watson
The Total Economic Impact™ of IBM Security MaaS360 with WatsonWhitepaper Cost savings and business benefits enabled by MaaS360
-
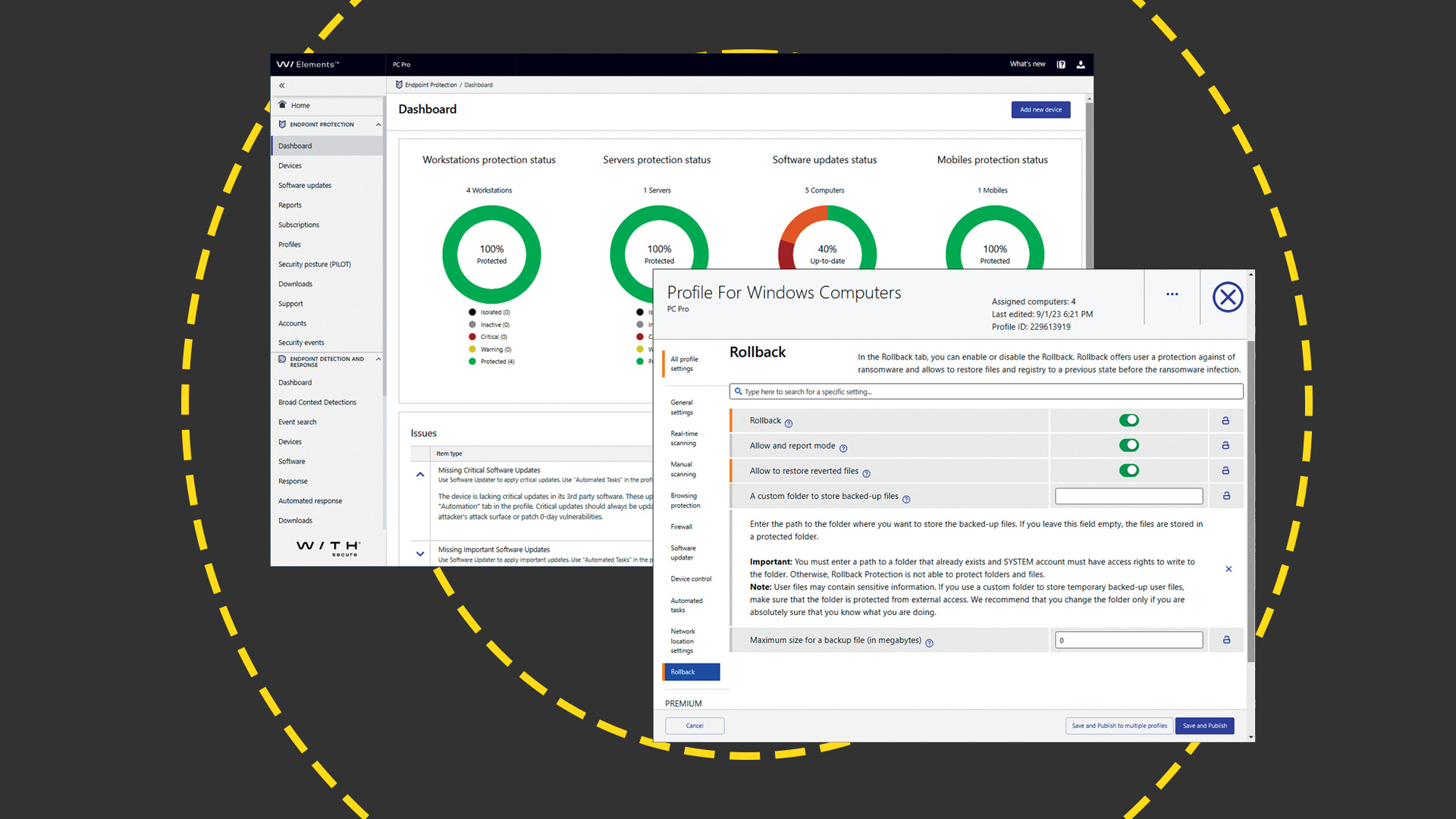 WithSecure Elements EPP and EDR review: Endpoint protection on a plate
WithSecure Elements EPP and EDR review: Endpoint protection on a plateReviews An affordable cloud-managed solution with smart automated remediation services
-
 KuppingerCole leadership compass report - Unified endpoint management (UEM) 2023
KuppingerCole leadership compass report - Unified endpoint management (UEM) 2023Whitepaper Get an updated overview of vendors and their product offerings in the UEM market.
-
 The Total Economic Impact™ of IBM Security MaaS360 with Watson
The Total Economic Impact™ of IBM Security MaaS360 with WatsonWhitepaper Get a framework to evaluate the potential financial impact of the MaaS360 on your organization
-
 Unified endpoint management software vendor assessment
Unified endpoint management software vendor assessmentWhitepaper Make positive steps on your intelligent automation journey
