Qualcomm and Mediatek flaws left millions of Android users at risk
An open source audio codec used by chipset firms is believed to have put two-thirds of Android users' private calls and files at risk

Qualcomm and MediaTek, two of the biggest chipmakers in the world, have been found to have used vulnerable technology in smartphones that could have led to privacy violations of Android users.
Check Point Research (CPR) discovered a number of vulnerabilities in the Apple Lossless Audio Codec (ALAC), a component responsible for compressing audio data, that could have led to users’ calls and stored images being accessed by cyber attackers.
The researchers believe that more than two-thirds of the world’s Android smartphones were vulnerable to the attacks at some point.
The vulnerabilities were found in the ALAC code which Apple made open source in 2011; the ALAC has since been installed in a wide variety of non-Apple audio playback devices and programmes - not just Android smartphones, CPR said.
Apple has since updated the code since it went open source, but the code in question had not been updated since 2011 and both Qualcomm and MediaTek ported the vulnerable ALAC code into their audio decoders.
Attackers could have used the vulnerabilities to conduct a remote code execution (RCE) attack on smartphones by sending victims a malformed audio file, the researchers said, but will not unveil full details of how the vulnerabilities can be exploited until they are presented at the CanSecWest conference in May.
RELATED RESOURCE

“We've discovered a set of vulnerabilities that could be used for remote execution and privilege escalation on two-thirds of the world's mobile devices,” said Slava Makkaveev, reverse engineering and security research, at CPR. “The vulnerabilities were easily exploitable. A threat actor could have sent a song (media file) and when played by a potential victim, it could have injected code in the privileged media service.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
“The threat actor could have seen what the mobile phone user sees on their phone. In our proof of concept, we were able to steal the phone's camera stream. What is the most sensitive information on your phone? I think it's your media: audio and videos. An attacker could have stolen that through these vulnerabilities. The vulnerable decoder is based on the code shared by Apple 11 years ago.”
MediaTek tracks both vulnerabilities as CVE-2021-0674 and CVE-2021-0675, scoring 5.5 and 7.8 out of ten on the CVSSv3 threat severity scale, and were patched by the company in December 2021.
Qualcomm tracks the security vulnerability as CVE-2021-30351, scoring 9.8, a critical rating, and affected a score of Snapdragon products. Qualcomm patched the issue in December 2021 and CPR waited until this week to publish details to allow users time to patch.
CPR recommends all Android users regularly patch their phones to the latest version that Google issues on a monthly basis.

Connor Jones has been at the forefront of global cyber security news coverage for the past few years, breaking developments on major stories such as LockBit’s ransomware attack on Royal Mail International, and many others. He has also made sporadic appearances on the ITPro Podcast discussing topics from home desk setups all the way to hacking systems using prosthetic limbs. He has a master’s degree in Magazine Journalism from the University of Sheffield, and has previously written for the likes of Red Bull Esports and UNILAD tech during his career that started in 2015.
-
 2026 in IoT attacks: the biggest threats so far and what businesses can do
2026 in IoT attacks: the biggest threats so far and what businesses can doIn-depth Internet of Things devices are more useful than ever – but security is still playing catch-up
-
 Anthropic is increasing Claude Code usage limits — here’s everything you need to know
Anthropic is increasing Claude Code usage limits — here’s everything you need to knowNews The new deal will help Anthropic increase Claude Code usage limits, and API rate limits for Claude Opus models
-
 Mobile app security is a huge blind spot for developer teams – 93% are confident their applications are secure, but 62% reported breaches last year
Mobile app security is a huge blind spot for developer teams – 93% are confident their applications are secure, but 62% reported breaches last yearNews Organizations are overconfident about their mobile app security practices, according to new research, and it’s putting enterprises and consumers alike at risk.
-
 GPU memory vulnerability could allow hackers to access LLM responses - and Apple, Qualcomm, and AMD products were all at risk
GPU memory vulnerability could allow hackers to access LLM responses - and Apple, Qualcomm, and AMD products were all at riskNews The GPU memory vulnerability could've left large language models wide open to exploitation by threat actors
-
 APIs: Understanding the business benefits and risks
APIs: Understanding the business benefits and riskswhitepaper What you need to know about potential data exposure from APIs
-
 Apple patches actively exploited iPhone, iPad zero-day and 18 other security flaws
Apple patches actively exploited iPhone, iPad zero-day and 18 other security flawsNews The out-of-bounds write error is the eighth actively exploited zero-day impacting Apple hardware this year and could facilitate kernel-level code execution
-
 Businesses on alert as mobile malware surges 500%
Businesses on alert as mobile malware surges 500%News Researchers say hackers are deploying new tactics that put Android and iOS at equal risk
-
 Apple fixes array of iOS, macOS zero-days and code execution security flaws
Apple fixes array of iOS, macOS zero-days and code execution security flawsNews The first wave of security updates for Apple products in 2022 follows a year in which a wide variety of security flaws plagued its portfolio of devices
-
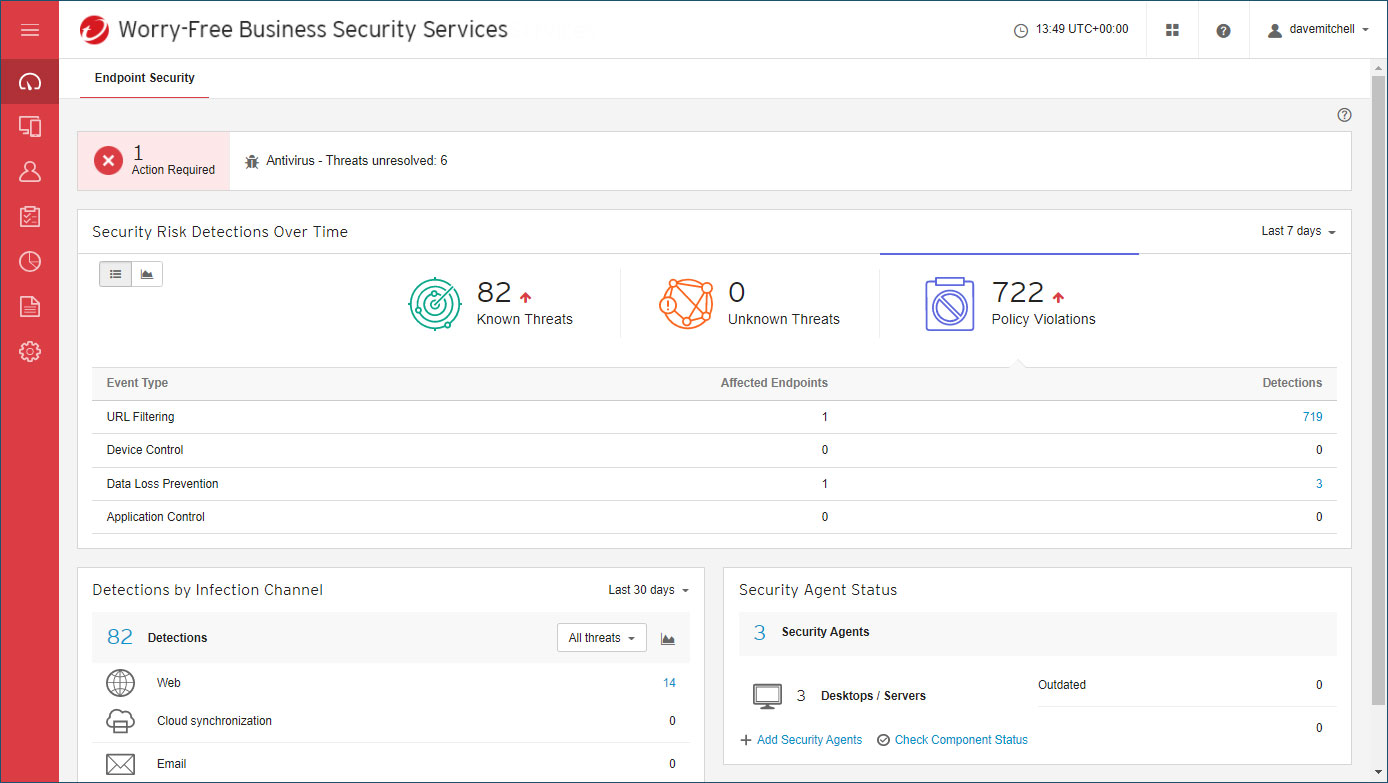 Trend Micro Worry-Free Business Security review: Great cloud-managed malware protection
Trend Micro Worry-Free Business Security review: Great cloud-managed malware protectionReviews A reassuringly simple endpoint-protection solution – although mobile support is basic
-
 Over 300,000 Android users downloaded banking trojan malware
Over 300,000 Android users downloaded banking trojan malwareNews Hackers defeated Google Play restrictions by using smaller droppers in apps and eliminating permissions needed
