Meltdown and Spectre: Samsung Galaxy S7 vulnerable to Meltdown hack
The flaw potentially effects tens of millions of users that still own the S7

Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
You are now subscribed
Your newsletter sign-up was successful
12/04/2018:AMD makes Spectre fixes available for PCs and servers
AMD has released a number of updates to help protect systems against the Spectre vulnerability found in its chips months after the flaw was disclosed to the public at the start of the year.
Spectre comprises a series of vulnerabilities that exploit the speculative execution system used in most modern processors to increase performance. The Spectre flaws could open up access to protected parts of the memory, such as passwords and private keys.
Months after the disclosure, AMD today finally signalled that it was ready to release updates.
"Today, AMD is providing updates regarding our recommended mitigations for Google Project Zero (GPZ) Variant 2 (Spectre) for Microsoft Windows users. These mitigations require a combination of processor microcode updates from our OEM and motherboard partners, as well as running the current and fully up-to-date version of Windows," said Mark Papermaster, senior vice president and chief technology officer at AMD in a blog post.
"While we believe it is difficult to exploit Variant 2 on AMD processors, we actively worked with our customers and partners to deploy the above-described combination of operating system patches and microcode updates for AMD processors to further mitigate the risk."
Microsoft is releasing an operating system update containing Spectre Variant 2 Spectre mitigations for AMD users running Windows 10 (version 1709). AMD said that support for these mitigations for AMD processors in Windows Server 2016 is expected to be available following final validation and testing.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
Papermaster added that the updates alongside his firm's recommended mitigations addressing Variant 2 have been released to customers and partners for AMD processors dating back to the first "Bulldozer" core products introduced in 2011. He added that users would be able to install the microcode by downloading BIOS updates provided by PC and server manufacturers and motherboard providers - meaning customers must wait for companies to make the fixes available.
As for the danger posed by Spectre Variant 1, AMD said in January that it could be contained with Microsoft operating system patches, released earlier in the year.
AMD did not disclose any details about fixes for processors older than the Bulldozer line. The processor company is yet to release fixes for Ryzenfall, Masterkey, Fallout, and Chimera vulnerabilities disclosed last month by Isreali firm CTS Labs.
21/02/2018:Intel releases fixes for Kaby Lake, Coffee Lake and Skylake-based platforms
Intel has developed a number ofmicrocode solutions to protect its customers against the Meltdown and Spectre exploits.
The released updates include fixes for its OEM customers and partners for Kaby Lake and Coffee Lake-based platforms, as well as additional Skylake-based platforms, the chip giant said.
These include its sixth, seventh and eight-generation Intel Core product lines as well as the latest Intel Core X-series processor family.
The recently announced Intel Xeon Scalable and Intel Xeon D processors for data centre systems are also covered by the patches.
"This effort has included extensive testing by customers and industry partners to ensure the updated versions are ready for production," Intel'sexecutive vice president and general manager of the Data Center Group,Navin Shenoy,said in a blog post."On behalf of all of Intel, I thank each and every one of our customers and partners for their hard work and partnership throughout this process."
OEM firmware updates will deliver the new microcode, Shenoy said, advising that users should always keep their systems up to date in light of the flaws, which were made public in January.
"There is also a comprehensive schedule and current status for planned microcode updates available online," he added, stating that in some cases, there will be multiple mitigation techniques available that may provide protection against the exploits. This includes 'Retpoline', a Google-developed mitigation technique for Variant 2.
Inte started re-issuing Meltdown and Spectre patches - initially for its Skylake-based Core and Core M processors - earlier this month, after initial attempts to patch the flaws resulted in performance slowdowns and computer reboots.
The vendor has alreadyupped its bug bounty reward programmefrom $100,000 to $250,000 for any security researcher who finds new side-channel vulnerabilities in its processors.
15/02/2018:Researchers find fresh Meltdown, Spectre exploits in modern CPUs
Researchers have discovered new ways to exploit the Meltdown and Spectre flaws that potentially go beyond the proof of concept theories that had companies scrambling to patch Intel and AMD processors last month.
The Meltdown and Spectre flaws were first revealed to be early concepts of what could potentially be exploited by hackers and although there were no instances of the flaws being used in the wild, experts warned exploits could be created based on the original findings.
It now appears that such exploits have been discovered by a team from Princeton University, in collaboration with Nvidia. Dubbed MeltdownPrime and SpectrePrime, the exploits are able to take advantage of modern processor designs that prioritise speed and efficiency over security.
In order for processors to be as efficient as possible, individual instructions are carried out based on what resources are available, rather than in a serial fashion. This means that a process isn't necessarily carried out in a step-by-step order, as this might leave parts of the chip idle while it waits for the first step to be finished.
In the event that a resource does become idle, modern processors are also built to perform speculative executions. For example, if the next instruction in the line tries to access a memory resource using a read operation, it may take some time to determine whether it has permission to access it. In order to avoid a slowdown in the process as the determination is made, the processor can speculatively execute the read instruction, which can either be deleted if permission is rejected, or used to provide a speed boost once it's accepted.
Meltdown and Spectre are referred to as side-channel attacks that exploit this processor architecture. Meltdown in effect breaks the mechanism that allows instructions to access the system memory at random, while Spectre tricks the processor into assigning instructions to predefined memory locations that a hacker can exploit.
"Rather than leveraging cache pollution during speculation, they exploit the ability of one core to invalidate an entry in another core's cache by speculatively requesting write permissions for that address," the paper explained.
In other words, the MeltdownPrime and SpectrePrime exploits are able to figure out what addresses were speculatively accessed by the processor. Once this happens, it can use an illegal process (without permission) as the basis for inducing a second legal process that's capable of leaking cached memory to the hackers something that would otherwise be impossible to do.
The researchers managed to prove their concepts on an Apple MacBook using a 2.4GHz Intel Core i7 processor, although it was using a version of MacOS High Sierra that predates Apple's Spectre patch, meaning it's not a zero-day attack.
The good news is that the researchers believe software patches addressing the original Meltdown and Spectre flaws will be enough to deal with the Prime variants, however hardware manufacturers will need to tweak their designs going forward.
"We believe that any software techniques that mitigate Meltdown and Spectre will also be sufficient to mitigate MeltdownPrime and SpectrePrime," the researchers explained. "On the other hand, we believe that microarchitectural mitigation of our Prime variants will require new considerations."
The news of the discovery coincided with a move by Intel to up its bug bounty reward programme from $100,000 to $250,000 for any security researcher who finds new side-channel vulnerabilities in its processors.
12/02/2018:Meltdown patches lead to high performance overheads
The latest Meltdown patches for Linux machines could impact performance byup to 800% in some circumstances, an assessment by a famous software engineer has revealed.
Netflix engineer andcomputing performance expert, Brendan Gregg - also known as dTrace Daddy -developed a "microbenchmark" to assess the Linux kernel page table isolation (KPTI) patch for the Meltdown CPU design flaw. The benchmark revealed that the patch will significantly increase overheads.
"The patches that workaround Meltdown introduce the largest kernel performance regressions I've ever seen," Gregg said in a blog post.
To understand the KPTI overhead, Gregg said there are at least five factors at play, which start with the syscall rate. When the rate of calls to the system reaches 50,000 per second per processor, the performance overhead hits 2%, and climbs as the syscall rate increases.
Next are context switches - a 'save point' for the current progress state of a process to restart it from that point later. These add similar overheads to the syscall rate, while page fault rates add "a little more" of a performance overhead as well.
Large amounts of 'hot' data - more than 10MB of data that's accessed frequently - create further performance issues due to the amount of time it takes to flush the memory cache, turning a 1% overhead created by syscall cycles into a 7% overhead, Gregg said. "This overhead can be reduced by A) pcid, available in Linux 4.14, and B) Huge pages," he added.
Lastly, certain cache access patterns can add another 10% overhead, he explained.
To explore these variants, Gregg wrote a simple microbenchmark where he could vary the syscall rate and the working set size.
He then analysed performance during the benchmark, and used other benchmarks to confirm findings. He discovered that the variables to watch out for are the syscall numbers, the Linux kernel being used and if it supports process-context identifiers, and the size of the pages being used - using larger pages so you have fewer pages to track.
Gregg also looked into the impact of the patches on the AWS infrastructure used by his employer, Netflix. He said: "Practically, I'm expecting the cloud systems at my employer (Netflix) to experiencebetween 0.1% and 6% overhead with KPTI due to our syscall rates, and I'm expecting we'll take that down to less than 2% with tuning".
The worst case Gregg found was an 800% overhead, saying that people can expect an impact of anywhere between 1% and 800%.
"Where you are on that spectrum depends on your syscall and page fault rates, due to the extra CPU cycle overheads, and your memory working set size, due to TLB flushing on syscalls and context switches," he said, but concluded thatthrough tuning some of the systems, it's possible to "significantly reduce the overheads".
Linux creator Linus Torvalds has previously lambasted Intel's approach to fixing the Meltdown and Spectre flaws.
He criticised Intel's plan to continue shipping affected chips with an optional patch to apply, as well as the performance issues that resulted from some initial Intel patches. Intel last week released fresh patches that it says do not impact performance.
09/02/2018:VMware advises customers how to mitigate the CPU chip vulnerabilities
Cloud giant VMware has advised its customers on how to mitigate the Meltdown and Spectre chip vulnerabilities.
In a security advisory released on Thursday and rated with a severity of "important", the firm states that Meltdown and Spectre can create problems for virtual appliances, but explains that the mitigation tactics will only stop attacks as "a temporary solution".
Permanent fixes will be released as soon as they are available, VMware added.
The temporary patches fix Bounds-Check bypass, Branch Target Injection, and Rogue data cache load issues in several of VMware's products, includingIdentity Manager (vIDM),vCloud Usage Meter, vSphere Integrated Containers,vCenter Server, vSphere Data Protection and vRealize Automation (vRA).
"CPU data cache timing can be abused to efficiently leak information out of mis-speculated CPU execution, leading to (at worst) arbitrary virtual memory read vulnerabilities across local security boundaries in various contexts," the firm said in a security advisory.
"Speculative execution is an automatic and inherent CPU performance optimization used in all modern processors. Successful exploitation may allow for information disclosure."
Users should note that several of the workarounds also require logging on as a privileged user and then typing a couple of commands, while some of the others require a little more skill.
"Please review the patch/release notes for your product and version and verify the checksum of your downloaded file," VMware added.
29/01/2018:Microsoft removes Spectre protection after Intel warning
Microsoft has issued an update that reverses an earlier patch against the Spectre chip flaw.
The rollback looks to repairthe mess madeby Intel's original microcode updates - and the BIOS updates from PC makers and software vendors like Microsoft based on them as they caused performance issues for many users post-installation, from reboots to significant slowdowns.
Installing the freshMicrosoft patch, dubbed KB4078130, will help if you've recently experienced any sluggishness on your Windows 7, 8.1 or Windows 10 PC, or any unexpected reboots. This is because the update disables the mitigation for Spectre variant 2's branch target injection vulnerability, which is widely blamed for causing the performance issues.
Inteleffectively recalled its patches last week, warning users not to install them due to the adverse effects customers were experiencing.
Microsoft's update summary read: "We understand that Intel is continuing to investigate the potential impact of the current microcode version and encourage customers to review their guidance on an ongoing basis to inform their decisions.
"In our testing this update [KB4078130]has been found to prevent the behaviordescribed."
More experienced users can download a version of Microsoft's update that allows them toedit the Windows registry and toggle the Spectre variant 2 mitigation on or off, the idea being that when Intel solves its own patching problem, they can simply re-enable it.
It also mentioned that "there are no known reports" of the Spectre variant 2 flaw being used to attack people's computers.
Anyone with an affected system can download the patch via theMicrosoft Update Catalogue.
It's also come to light in recent days that Intel may have initially told a handful of customers about the processor vulnerabilities, including Chinese tech companies like Alibaba and Lenovo, but not the US government.
Intel couldn't notify everyone - including US officials - in time because the existence of the Meltdown and Spectre exploits were revealed early, according to theWall Street Journal.
Linux creator Linus Torvalds last week slammed Intelfor the fiasco surrounding its Meltdown and Spectre patches, calling the fixes "pure garbage".
In a post on the Linux kernel mailing list, Torvalds said the patches for Intel chips dating back through the last decade "do literally insane things" to the performance of the systems they are installed on. Intel itself found that the patches impact performance by up to 25% on data centre chips, and 3% to 4% on other systems.
26/01/2018:Intel warned OEMs about its processor flaws in November
Intel had quietly warned computer makers about its chips vulnerability to Meltdown and Spectre back in November 2017, according the chip maker's internal documentation.
A memo from inside Intel for the eyes of its OEM customers was seen French technology publication LeMagIT, which reported that Intel had alerted the OEMs to the security bugs in its chips caused be a design flaw on November 29.
The document, title "Technical Advisory" appears to have come a few months after the processor security flaws were first discovered in June 2017 by academic researchers and security specialists from Google's Project Zero team.
While the document does not shed any fresh light on the Meltdown and Spectre flaws, it does demonstrate the secrecy Intel and other major technology firms alongside their OEM customers were operating under to keep the processor flaws secret until they were in a position to fix them.
Meltdown and Spectre came to light January 2, seven days before the flaws were to be revealed to the public on January 9.
The level of secrecy around Meltdown and Spectre appears to have been in place to avoid too much panic over plugging the security holes until fixes were in places, as well as prevent opportunistic hackers from exploiting the flaws once they were revealed.
However, despite keeping quiet about Meltdown and Spectre for around six months, the patching process has not been completely smooth, with Intel's patches causing unexpected reboots for some of its processors, arguably causing more problems than the bugs the patches were designed to fix.
15/01/18: Google patches Meltdown/Spectre 'without performance slowdowns'
Google's patch for Meltdown and Spectre vulnerabilities aims to address the trickiest variant of the Spectre CPU attacks - Variant 2 - which can significantly impact the CPU performance of devices.
Known as Retpoline, the update stops the vulnerabilities harming the performance of the company's cloud services. Before it was released, Google assumed the only way round stalling the performance of its cloud service was to disable thespeculative execution CPU, which is used to enhance performance.
It decided against that and instead developed the patch instead, however, which at first did have a detrimental affect on the running speed of cloud applications. But the version of the patch that has made its way into the real world has not had an impact, Google said.
"With Retpoline, we could protect our infrastructure at compile-time, with no source-code modifications," Google'sBen Treynor Sloss, vice president of24x7, said in a blog post. "Furthermore, testing this feature, particularly when combined with optimizations such as software branch prediction hints, demonstrated that this protection came with almost no performance loss."
He added that the company began deploying the fix across its infrastructure and shared it with other industry partners, also releasing it as an open source compiler to protect users. It did all of this without telling its customers and no one even batted an eyelid, proving that the performance-optimised updates didn't have an effect on workloads at all, he claimed.
"We believe that Retpoline-based protection is the best-performing solution for Variant 2 on current hardware,"Treynor Sloss added. "Retpoline fully protects against Variant 2 without impacting customer performance on all of our platforms. In sharing our research publicly, we hope that this can be universally deployed to improve the cloud experience industry-wide."
12/01/2018:Intel's patches cause reboots on Broadwell and Haswell CPUs
Intel has warned that the patches it has issued to combat the Meltdown flaws in its chips could cause central processor units (CPUs) from the Broadwell and Haswell generations to reboot more often than would be expected.
Such reboots may lead to problems for PCs and servers using the processors, and will likely prompt Intel to work out an additional fix.
"We have received reports from a few customers of highersystem reboots after applying firmware updates. Specifically, these systems are running IntelBroadwell and HaswellCPUs for both client and data centre," said Navin Shenoy, general manager of the Intel's data centre group.
"We are workingquickly with these customers to understand, diagnose and address this reboot issue.If this requires a revised firmware update from Intel, we will distribute that update through the normal channels. We are also working directly with data centre customers to discuss the issue."
Intel has reportedly requested that companies running cloud computing services hold off updating their servers until the chip maker is able to squash bugs in the patches, according to The Wall Street Journal.
Citing a confidential document shared with some customers, the newspaper noted that Intel had identified three issues with its microcode patches for its chips.
09/01/2018: Intel creates security research team in wake of Spectre flaw
Intel is reportedly due to create an internal cyber security research group following the discovery of critical vulnerabilities affecting every one of its processors from the past 10 years.
CEO Brian Krzanich told employees in an internal memo that the company was placing renewed importance on security, and that the changes would effective immediately, according to the Oregonian newspaper.
"It is critical that we continue to work with the industry, to excel at customer satisfaction, to act with uncompromising integrity, and to achieve the highest standards of excellences," said Krzanich in the memo, sent on Monday ahead of his CES 2018 keynote.
"Simply put, I want to ensure we continue to respond appropriately, diligently, and with a customer-first-attitude."
Intel's head of human resources, Leslie Culbertson, who has been with the company since 1979, is set to run the new Intel Product Assurance and Security group, according to the memo. Culbertson had previously served as Intel's director of finance and as general manager for systems manufacturing.
The memo also indicated that Josh Walden, who has only just been appointed head of Intel's technology group, and Steve Smith, VP of Intel's data centre engineering group, will also be reassigned to work as part of Culbertson's team.
IT Pro has contacted Intel to confirm the memo's content.
Intel was clearly caught off-guard by the Meltdown processor flaw, which in theory could have allowed hackers to steal sensitive data, but there have been no reports of the vulnerability being exploited in the wild.
Intel was initially quiet about the flaws and even dismissed initial reports as "inaccurate", however, the company has acknowledged the issues and released updates for more than 90% of its processors released in the past five years, with more coming in the next few weeks.
"I want to take a moment to thank the industry for addressing the recent security findings," said Krzanich, during his CES keynote this week. "The collaboration among so many companies to address this industry-wide issue has been truly remarkable."
Intel previously operated its own security group under Intel Security, created following its acquisition of McAfee in 2011. However, in 2016 Intel sold control of the division off to private equity company TPG, which took a 51% majority stake in the firm, whose name was changed back to McAfee, in a deal thought to have generated $3.1 billion for Intel.
Krzanich reassured investors at the time that security would remain an important part of its chips as the company pushed into new markets.
08/01/2018:Tech industry responds to the CPU vulnerability affecting most computer chips
Every year, the security industry spews out a new vulnerability for us tech folk to worry about, adding to the long list of privacy concerns we've endured over the last decade or so.
Well, 2018 came out of the starting blocks particularly early. And this time, it's a big one.
As we learned on Wednesday, a serious design flaw, which can be exploited using techniques known as Spectre and Meltdown, has been reportedly present in all Intel's CPUs made in the last 10 years, which could potentially leave devices vulnerable to hackers, requiring an operating system (OS) update in order to fix it. If the rumours are true, the bug will allow normal user programs, such as database applications and JavaScript in web browsers, to distinguish some of the layout or contents of protected kernel memory areas of the chips, which could cause a performance hit on some machines.
Reported by The Register, the flaw affects all systems running Intel x86 chips and is present across all popular operating systems, including Windows, Linux, and macOS. However, due to the full details of the vulnerability currently being under embargo, meaning the full details of the bug are yet to be officially announced, it's not yet clear just how serious it is.
The technology industry, however, hasn't restricted its reactions to the news, with key players from different sectors such as cloud providers and device manufacturers, reporting whether they already knew about the flaw, if they've already patched it or what it could mean if it isn't fixed.
Cloud providers' responses
According to the search engine giant, the Google Project Zero security team has already fixed the bug after it discovered the CPU vulnerability last year.
Google's Cloud VP, Ben Treynor Sloss, said in a statement on Wednesday that since this time, the company's engineering teams have been working to protect customers from the flaw "across the entire suite of Google products", including Google Cloud Platform (GCP), G Suite applications, and the Google Chrome and Chrome OS products.
"We also collaborated with hardware and software manufacturers across the industry to help protect their users and the broader web," Sloss explained.
"All G Suite applications have already been updated to prevent all known attack vectors. G Suite customers and users do not need to take any action to be protected from the vulnerability."
Google said this was possible because its Cloud product is architected in a manner that enables the team to update the environment while providing operational continuity for its customers.
"We used our VM Live Migration technology to perform the updates with no user impact, no forced maintenance windows and no required restarts," Sloss added.
However, the firm warned customers who use their own operating systems with GCP services may need to apply additional updates to their images and should refer to the GCP section of the Google Security blog post for additional details.
Amazon
Since the CPU flaw was reported widely by the tech industry on Wednesday, Amazon Web Services (AWS) released a statement to say it too was made aware of the research around the bug, which it referred to as "side-channel analysis of speculative execution on modern computer processors, CVE-2017-5715, CVE-2017-5753, and CVE-2017-5754".
AWS even went as far as saying the vulnerability has existed for more than 20 years in modern processor architectures like Intel, AMD, and ARM across servers, desktops, and mobile devices, and "all but a small single-digit percentage of instances across the Amazon EC2 fleet are already protected".
The cloud giant reassured users that the remaining instances will be completed in the next several hours, with associated instance maintenance notifications.
"While the updates AWS performs protect underlying infrastructure, in order to be fully protected against these issues, customers must also patch their instance operating systems," it warned. "Updates for Amazon Linux have been made available, and instructions for updating existing instances are provided further below along with any other AWS-related guidance relevant to this bulletin."
AWS added that updated EC2 Windows AMIs will also be provided as Microsoft patches become available.
Hardware manufacturers' responses
Apple
According to software developer Alex Ionescu, Apple introduced a fix for the CPU flaw in the release of macOS 10.13.2, and there are additional tweaks set to be introduced in macOS 10.13.3, which is currently in beta testing.
According to AppleInsider, "multiple sources within Apple" have said that updates made in macOS 10.13.2 have mitigated "most" security concerns associated with the CPU vulnerability.
Microsoft
We haven't heard much from Microsoft yet about the flaw, but it's expected to publicly introduce the necessary changes to its Windows operating system in an upcoming Patch Tuesday this month, after seeding them to beta testers running fast-ring Windows Insider builds in November and December.
Security vendors
McAfee
Security giant McAfee released a statement today saying the disclosure of the CPU flaw reveals that the scope of implications extends beyond just PCs to servers, cloud, mobile and IoT platforms, and affects the CPU platform of multiple vendors, not just one as was first thought. Apparently, it can impact both corporate and consumer domains at the same time if left unpatched.
"These methods attack the foundational modern computer building block capability that enforces protection of the OS from applications, and applications from one another," warned the firm's CTO Steve Grobman. "Businesses and consumers should update operating systems and apply patches as soon as they become available."
Dale Walker is a contributor specializing in cybersecurity, data protection, and IT regulations. He was the former managing editor at ITPro, as well as its sibling sites CloudPro and ChannelPro. He spent a number of years reporting for ITPro from numerous domestic and international events, including IBM, Red Hat, Google, and has been a regular reporter for Microsoft's various yearly showcases, including Ignite.
-
 Does your business need cyber insurance?
Does your business need cyber insurance?In-depth As the cyber insurance market matures, do firms actually need it and if so, how should they choose a policy?
-
 Geekom A5 Pro review
Geekom A5 Pro reviewReviews It's not a mini PC for power users or intense graphics work, but as a productivity machine or media server, it will do very nicely
-
 Organizations hit by 90 zero-day vulnerabilities last year
Organizations hit by 90 zero-day vulnerabilities last yearNews Google Threat Intelligence researchers warn that edge devices and security appliances are prime entry points
-
 Blackpoint Cyber and NinjaOne partner to bolster MSP cybersecurity
Blackpoint Cyber and NinjaOne partner to bolster MSP cybersecurityNews The collaboration combines Blackpoint Cyber’s MDR expertise with NinjaOne’s automated endpoint management platform
-
 Busting nine myths about file-based threats
Busting nine myths about file-based threatsWhitepaper Distinguish the difference between fact and fiction when it comes to preventing file-based threats
-
 The threat prevention buyer's guide
The threat prevention buyer's guideWhitepaper Find the best advanced and file-based threat protection solution for you
-
 The Total Economic Impact™ of the Intel vPro® Platform as an endpoint standard
The Total Economic Impact™ of the Intel vPro® Platform as an endpoint standardWhitepaper Cost savings and business benefits enabled by the Intel vPro® Platform as an endpotnt standard
-
 The Total Economic Impact™ of IBM Security MaaS360 with Watson
The Total Economic Impact™ of IBM Security MaaS360 with WatsonWhitepaper Cost savings and business benefits enabled by MaaS360
-
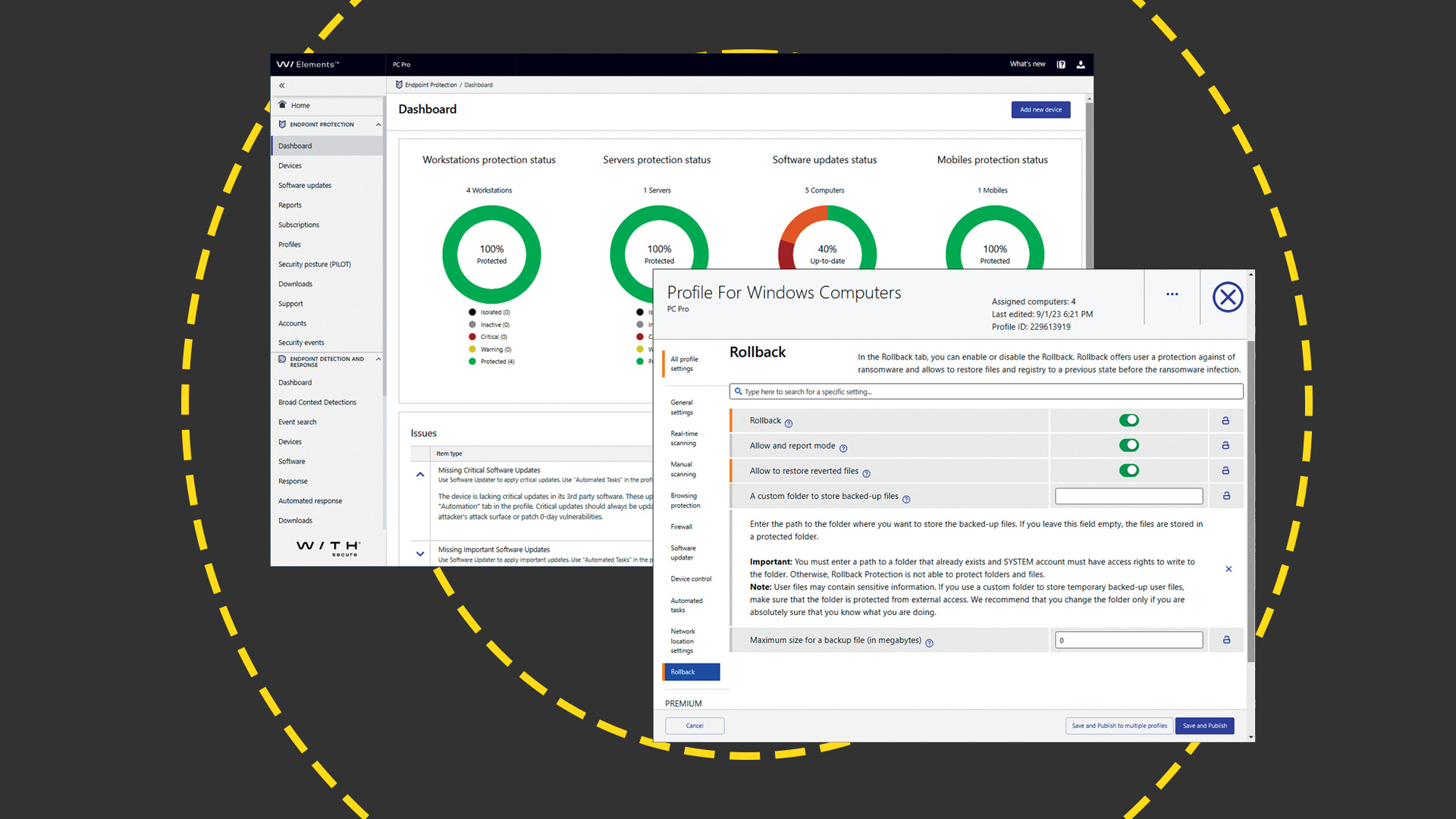 WithSecure Elements EPP and EDR review: Endpoint protection on a plate
WithSecure Elements EPP and EDR review: Endpoint protection on a plateReviews An affordable cloud-managed solution with smart automated remediation services
-
 Supply chain as kill chain
Supply chain as kill chainWhitepaper Security in the era Zero Trust