Ransomware discovered carrying legitimate Windows certificates
Sophos researchers pointed to the sophisticated signatures as a sign of a new, dangerous strategy by a group tied to Cuba


Cyber security company Sophos has issued a warning over antivirus-nullifying malware it discovered bearing legitimate digital certificates, including signatures from Microsoft’s own digital verification service.
The drivers, found paired with a ‘loader’ executable that was used to install the driver, carried the digital signature of Windows Hardware Compatibility Program (WHCP), and appeared to be specially designed to limit the functions of endpoint detection and response (EDR) security programs.
Code signatures are cryptographic certificates that indicate a program has not been altered since its release by its manufacturer. WHCP signatures are only intended to be given to software that Microsoft has checked over and given its personal seal of approval, and therefore seen as trustworthy files to run by Windows systems.
Researchers say that the find shows that threat actors are working harder to move up the 'trust chain', employing increasingly sophisticated methods to sign malware with legitimate cryptographic signatures so that it can be installed on systems without detection.
Sophos made the discovery while responding to a ransomware attack, which revealed the driver and executable. Because it prevented the attack from occurring, it has not been able to definitively identify the ransomware variant that the driver sought to enable and deploy.
However, in a blog post researchers noted that the loader used is likely a variant known as BURNTCIGAR. Use of this variant is characteristic of the Cuba ransomware group, and a search of public repositories for similar drivers revealed an archive that contained both the driver and loader, along with a list of 186 files that are commonly-used in endpoint security and EDR software. Researchers surmised that these were processes intended to be killed by the malware once activated, to allow the ransomware to run without resistance.
In a subsequent search for similar variants on the malicious driver, security researchers found as many as ten, having emerged in the middle of the year and grown in number since then. The earliest of such drivers found by Sophos was uploaded to antivirus aggregation website VirusTotal in July, and carried the signature of Chinese software developer Zhuhai liancheng Technology Co., Ltd.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
This company’s signature is flagged by Sophos as a potential unwanted application (PUA), and the threat actors appear to have moved away from this to less suspicious certificates in subsequent iterations. Indeed, other malicious drivers were signed by Nvidia, in addition to those that carried the WHCP signatures.
Following the discovery, Sophos Rapid Response collaborated with Microsoft to quell the threat, and to release a security update that revokes the affected certificates as well as improving detection for legitimate drivers that have been involved in malicious activity. This was released as a part of Microsoft’s December Patch Tuesday.
“In 2022, we’ve seen ransomware attackers increasingly attempt to bypass EDR products of many, if not most, major vendors,” said Christopher Budd, senior manager of Threat Research at Sophos.
RELATED RESOURCE

Getting board-level buy-in for security strategy
Why cyber security needs to be a board-level issue
“The most common technique is known as ‘bring your own driver,’ which BlackByte recently used, and it involves attackers exploiting an existing vulnerability in a legitimate driver. Creating a malicious driver from scratch and getting it signed by a legitimate authority is far more difficult. However, should they succeed, it’s incredibly effective because the driver can essentially carry out any processes without question.
“In the case of this particular driver, virtually all EDR software is vulnerable; fortunately, Sophos’ additional anti-tampering protections were able to halt the ransomware attack. The security community needs to be aware of this threat so that they can implement additional security measures, such as eyes on glass, where necessary; what’s more, we may see other attackers attempt to emulate this type of attack.”
Earlier in 2022, a similar technique was employed by threat actors who masked malware using Nvidia certificates, following a breach of Nvidia systems by the LAPSU$ hacking group. However, certificates are generally revoked by companies after they have been found to have been stolen, and Sophos’ discovery represents a step up in the methodology of attackers, as the drivers in use were, for all intents and purposes, seen as legitimate.
The Cuba ransomware group has previously claimed an attack on Montenegro’s government, and has been linked to a number of attacks by security researchers. The group’s exact origins are unknown, but some have suggested it could be Russia-backed due to observations of Russian on the group’s dark web site.

Rory Bathgate is Features and Multimedia Editor at ITPro, overseeing all in-depth content and case studies. He can also be found co-hosting the ITPro Podcast with Jane McCallion, swapping a keyboard for a microphone to discuss the latest learnings with thought leaders from across the tech sector.
In his free time, Rory enjoys photography, video editing, and good science fiction. After graduating from the University of Kent with a BA in English and American Literature, Rory undertook an MA in Eighteenth-Century Studies at King’s College London. He joined ITPro in 2022 as a graduate, following four years in student journalism. You can contact Rory at rory.bathgate@futurenet.com or on LinkedIn.
-
 Blackpoint Cyber and NinjaOne partner to bolster MSP cybersecurity
Blackpoint Cyber and NinjaOne partner to bolster MSP cybersecurityNews The collaboration combines Blackpoint Cyber’s MDR expertise with NinjaOne’s automated endpoint management platform
-
 Busting nine myths about file-based threats
Busting nine myths about file-based threatsWhitepaper Distinguish the difference between fact and fiction when it comes to preventing file-based threats
-
 The Total Economic Impact™ of the Intel vPro® Platform as an endpoint standard
The Total Economic Impact™ of the Intel vPro® Platform as an endpoint standardWhitepaper Cost savings and business benefits enabled by the Intel vPro® Platform as an endpotnt standard
-
 The Total Economic Impact™ of IBM Security MaaS360 with Watson
The Total Economic Impact™ of IBM Security MaaS360 with WatsonWhitepaper Cost savings and business benefits enabled by MaaS360
-
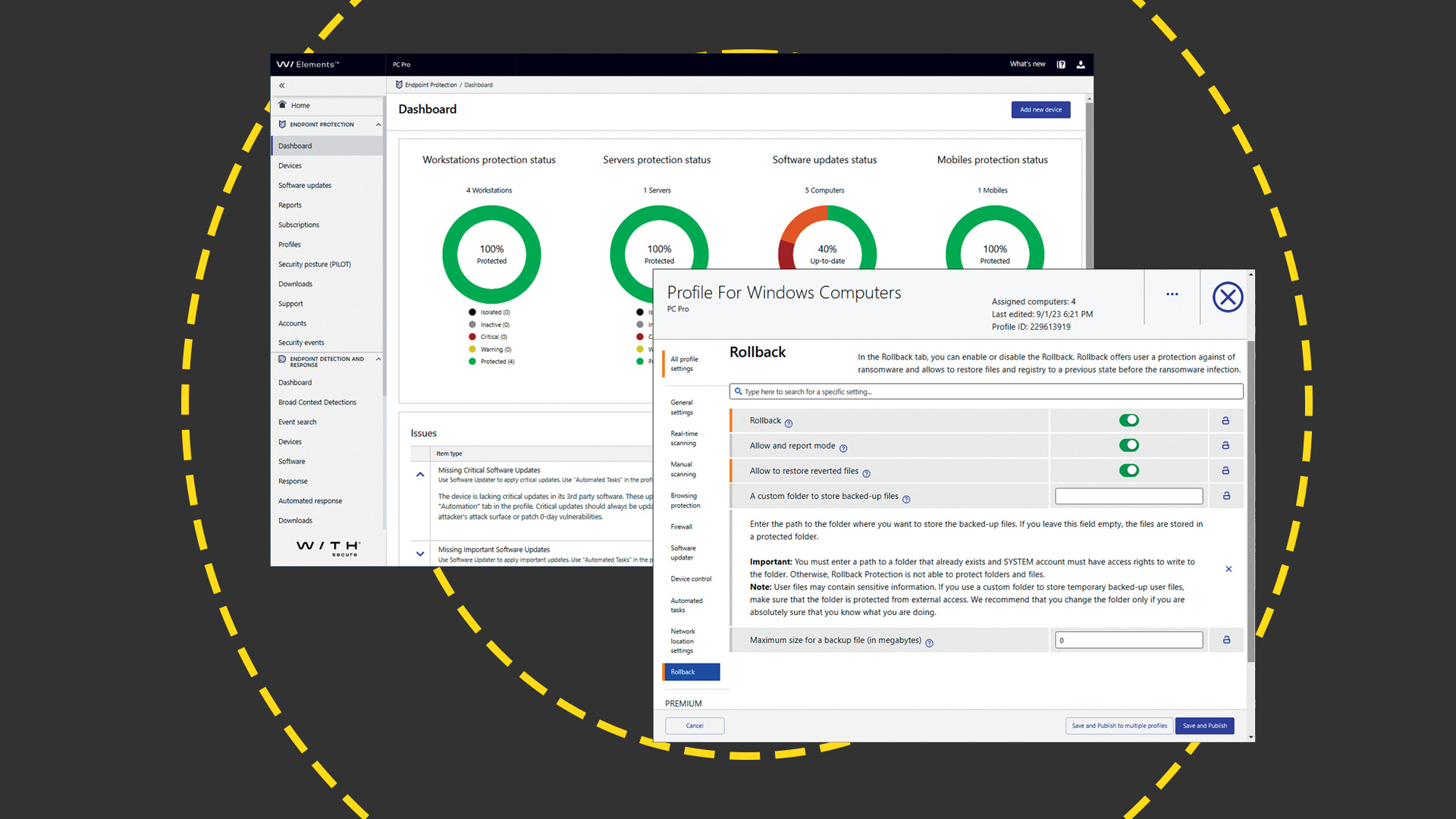 WithSecure Elements EPP and EDR review: Endpoint protection on a plate
WithSecure Elements EPP and EDR review: Endpoint protection on a plateReviews An affordable cloud-managed solution with smart automated remediation services
-
 KuppingerCole leadership compass report - Unified endpoint management (UEM) 2023
KuppingerCole leadership compass report - Unified endpoint management (UEM) 2023Whitepaper Get an updated overview of vendors and their product offerings in the UEM market.
-
 The Total Economic Impact™ of IBM Security MaaS360 with Watson
The Total Economic Impact™ of IBM Security MaaS360 with WatsonWhitepaper Get a framework to evaluate the potential financial impact of the MaaS360 on your organization
-
 Unified endpoint management software vendor assessment
Unified endpoint management software vendor assessmentWhitepaper Make positive steps on your intelligent automation journey


