Google removes 17 apps infected with evasive ‘Joker’ malware
Researchers identify three variations in the way the 'fleeceware' strain infects victims' Android devices


Google has removed a further 17 apps embedded with Joker malware after security experts warned of the fleeceware's continued rise in prominence.
The billing-fraud strain of malware was found in six apps marketing themselves as legitimate in early September, accounting for 200,000 installs. Google has now removed a further 17 apps infected with the malware from the Play Store after researchers with Zscaler alerted the company to their presence.
The malware simulates clicks and intercepts SMS messages to trick users into subscribing to unwanted premium services. These strains of malware, known as fleeceware, are generally difficult to detect because they use minimal code.
The 17 Android apps removed from the Play Store, downloaded around 120,000 times in total, includes All Good PDF Scanner, Mint Leaf Message, Unique Keyboard - Fancy Fonts & Free Emoticons, and Tangram App Lock, among others. These malicious apps also included a host of other messaging platforms, scanners and PDF converters, as well as photo editing tools.
Upon identifying these apps, Zscaler decided to establish the variations in payload deployment, as well as how and why Joker remains so evasive.
In a host of Joker variants, the final payload was delivered using a direct URL received from the command and control (C&C) server. The app, in these cases, had the C&C address hidden in the code with string obfuscation.
The infected app would contact the C&C server once the app was installed, which would then respond with the URL of a final payload. The JSON file also contained information related to the class name required to be executed from the final payload. The app, on receiving the JSON configuration, downloads the payload and executes it.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
Some apps, alternatively, operated under a one-stage download mechanism, in which the app used an encrypted stager payload URL encoded in the code itself. When infecting a device, the app downloads the stager payload rather than a final payload, which is then tasked with retrieving the final payload and executing it.
RELATED RESOURCE
Why IT leaders should consider a zero trust network access strategy
Enabling business while staying secure
The third method observed by researchers involves a complex two-stage download prior to retrieving the payload from the C&C server. This essentially adds an additional step to the previous one-stage download method.
Through all the variations of the method, the Joker payload remained the same throughout, executing functions that ranged from SMS harvesting to wireless application protocol (WAP) billing fraud.
To prevent the chances of any seemingly legitimate apps compromising users’ privacy and security, Zscaler has recommended ensuring that application permissions for accessing SMS messages, call logs, and contacts are restricted. Reading comments or reviews for many apps may also help to prevent inadvertently downloading malicious software.

Keumars Afifi-Sabet is a writer and editor that specialises in public sector, cyber security, and cloud computing. He first joined ITPro as a staff writer in April 2018 and eventually became its Features Editor. Although a regular contributor to other tech sites in the past, these days you will find Keumars on LiveScience, where he runs its Technology section.
-
 Blackpoint Cyber and NinjaOne partner to bolster MSP cybersecurity
Blackpoint Cyber and NinjaOne partner to bolster MSP cybersecurityNews The collaboration combines Blackpoint Cyber’s MDR expertise with NinjaOne’s automated endpoint management platform
-
 Busting nine myths about file-based threats
Busting nine myths about file-based threatsWhitepaper Distinguish the difference between fact and fiction when it comes to preventing file-based threats
-
 The Total Economic Impact™ of the Intel vPro® Platform as an endpoint standard
The Total Economic Impact™ of the Intel vPro® Platform as an endpoint standardWhitepaper Cost savings and business benefits enabled by the Intel vPro® Platform as an endpotnt standard
-
 The Total Economic Impact™ of IBM Security MaaS360 with Watson
The Total Economic Impact™ of IBM Security MaaS360 with WatsonWhitepaper Cost savings and business benefits enabled by MaaS360
-
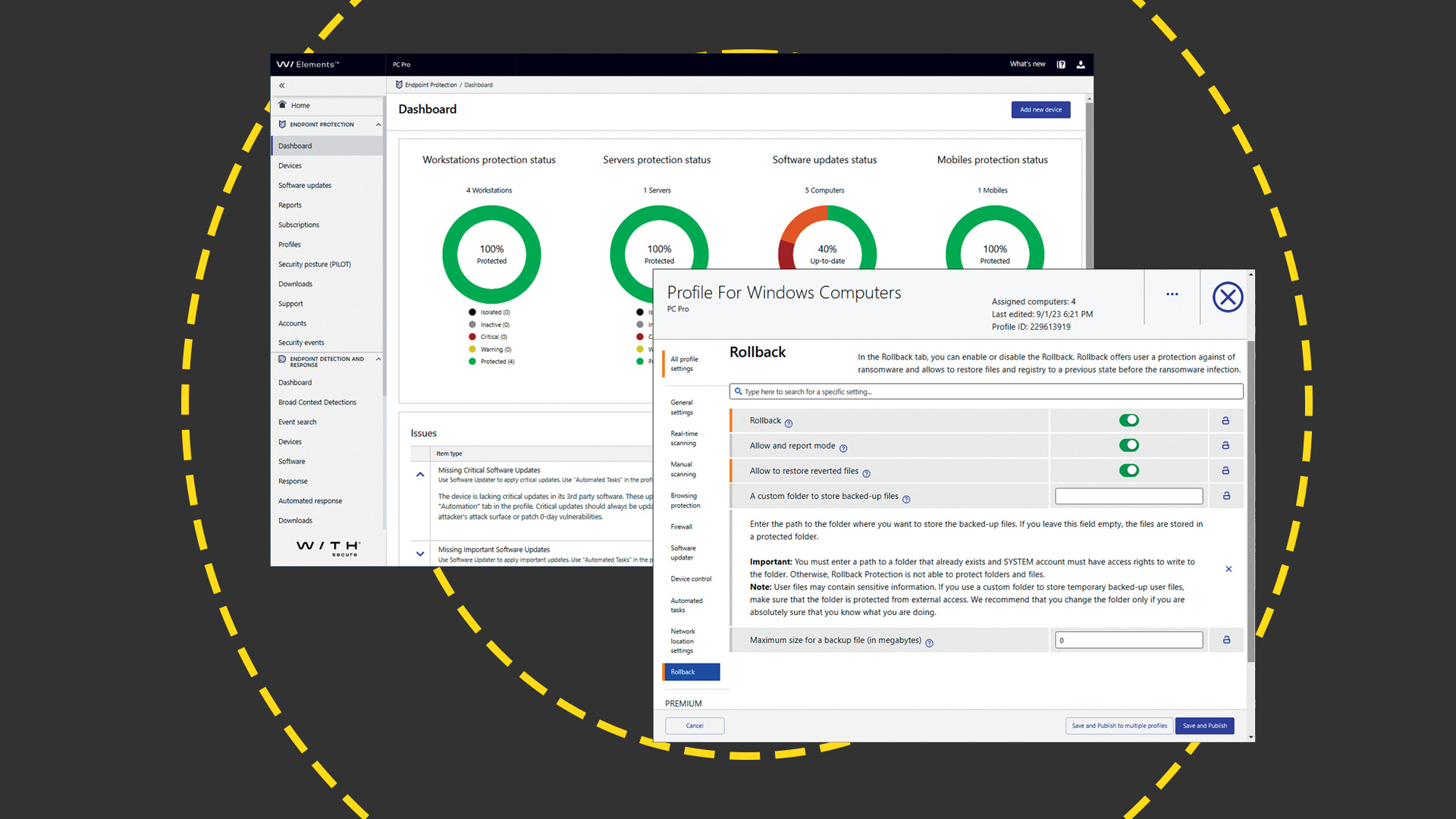 WithSecure Elements EPP and EDR review: Endpoint protection on a plate
WithSecure Elements EPP and EDR review: Endpoint protection on a plateReviews An affordable cloud-managed solution with smart automated remediation services
-
 KuppingerCole leadership compass report - Unified endpoint management (UEM) 2023
KuppingerCole leadership compass report - Unified endpoint management (UEM) 2023Whitepaper Get an updated overview of vendors and their product offerings in the UEM market.
-
 The Total Economic Impact™ of IBM Security MaaS360 with Watson
The Total Economic Impact™ of IBM Security MaaS360 with WatsonWhitepaper Get a framework to evaluate the potential financial impact of the MaaS360 on your organization
-
 Unified endpoint management software vendor assessment
Unified endpoint management software vendor assessmentWhitepaper Make positive steps on your intelligent automation journey

