What is attack surface management?
Instigate attack surface management to anticipate where cyber attackers might strike and avoid falling prey


Attack surface management (ASM) might sound like something the SAS might get involved in, but this most definitely refers to the world of networks and cyber security.
The attack surface is the sum of all possible entry points that a cyber criminal might use to gain unauthorised access to systems, networks or data. For a typical business, this might include devices, websites, servers, software platforms and even people. Every time the enterprise adds a server, deploys a new application, sets up a virtual private network (VPN) or enrols more users, the surface grows.
That’s where ASM can come in handy. Taking the perspective of the hacker into account, this process involves discovering, analysing and mitigating the vulnerabilities and potential vectors that altogether comprise the attack surface. Proper attack surface management highlights the targets and understands the level of risk associated with the attack vectors in question.
What does attack surface management involve?
Attack vectors are methods that attackers use to gain access, such as phishing, malware, API exploits or zero-day vulnerabilities. The attack surface is the target against which those methods can be deployed. So social engineering is an attack vector; an individual whose trust is exploited is part of the attack surface.
Figuratively speaking, your attack surface generally has three sides. One is the digital attack surface: that’s everything connected to your network, from apps to websites and the ports they connect through. Then there’s the physical attack surface – servers, mobile devices, routers and even printers. Finally, the social attack surface comprises staff, contractors and so forth. You can of course further break down these divisions with greater levels of granularity, but the digital, physical and social aspects broadly cover everything.
What steps can my business take to shrink its attack surface?
This is very much the hard part. Because the attack surface is always changing and evolving, managing it can seem like a Sisyphean task.
1. Minimise complexity
As a business expands, its IT environment tends to accumulate legacy endpoints and applications – prime targets for attackers. Security processes grow in complexity too, creating more potential for exploitable mistakes. Cut out legacy assets wherever you can, and segment your network to limit the potential for intrusions.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
2. Know your vulnerabilities
Static vulnerability scanning is valuable, but real attackers are more cunning and resourceful than any automated test. Schedule regular penetration testing, and include “red team” exercises to obtain a realistic, adversary’s-eye view of your vulnerabilities.
3. Raise awareness
Many compromises start at the social attack surface. Promote awareness of threats, from the shop floor to the boardroom – and support it with upstream security controls. Don’t play the blame game, but embrace zero trust principles to make it as hard as possible for anyone, whether inside the organisation or outside of it, to breach security.
4. Seek out an ASM solution
There are numerous ASM platforms out there, including ASM as a service. Most of these solutions address ASM from four perspectives: asset discovery, classification, risk prioritisation and ongoing monitoring. If you’re familiar with the security mindset you might wonder why there’s no risk remediation step – but that’s the sum of the other parts.
What do ASM services offer, in practical terms?
The asset discovery part is all about making sure you know what you’re working with. You can’t begin to manage the risks to your IT systems unless you’re fully apprised of exactly what and where those systems are. Creating a map of potential entry points can immediately highlight which are the most attractive to a threat actor.
This leads onto classification, where assets are analysed with regard to what they connect to, the attack routes they could enable, and the vulnerabilities they may contain. Once the process is complete, it’s time to prioritise, so that issues that represent the highest risk to the business can be dealt with most urgently. Those classifications, those priorities, will likely be subject to constant change, of course; that’s where the ongoing monitoring comes in, to ensure your organisation remains on top of its ASM game.
What’s the best ASM solution for my company?
As always in cyber security, there’s no one-size-fits-all answer. The best solution for your business won’t be the same as for someone else’s, perhaps for reasons of scalability, integration or cost. We can, however, give you some names to look up: Coalfire, CyCognito, ImmuniWeb, Randori, SearchLight, SpectralOps and UpGuard are all good places to start your ASM research.
Davey is a three-decade veteran technology journalist specialising in cybersecurity and privacy matters and has been a Contributing Editor at PC Pro magazine since the first issue was published in 1994. He's also a Senior Contributor at Forbes, and co-founder of the Forbes Straight Talking Cyber video project that won the ‘Most Educational Content’ category at the 2021 European Cybersecurity Blogger Awards.
Davey has also picked up many other awards over the years, including the Security Serious ‘Cyber Writer of the Year’ title in 2020. As well as being the only three-time winner of the BT Security Journalist of the Year award (2006, 2008, 2010) Davey was also named BT Technology Journalist of the Year in 1996 for a forward-looking feature in PC Pro Magazine called ‘Threats to the Internet.’ In 2011 he was honoured with the Enigma Award for a lifetime contribution to IT security journalism which, thankfully, didn’t end his ongoing contributions - or his life for that matter.
You can follow Davey on Twitter @happygeek, or email him at davey@happygeek.com.
-
 Blackpoint Cyber and NinjaOne partner to bolster MSP cybersecurity
Blackpoint Cyber and NinjaOne partner to bolster MSP cybersecurityNews The collaboration combines Blackpoint Cyber’s MDR expertise with NinjaOne’s automated endpoint management platform
-
 Busting nine myths about file-based threats
Busting nine myths about file-based threatsWhitepaper Distinguish the difference between fact and fiction when it comes to preventing file-based threats
-
 The Total Economic Impact™ of the Intel vPro® Platform as an endpoint standard
The Total Economic Impact™ of the Intel vPro® Platform as an endpoint standardWhitepaper Cost savings and business benefits enabled by the Intel vPro® Platform as an endpotnt standard
-
 The Total Economic Impact™ of IBM Security MaaS360 with Watson
The Total Economic Impact™ of IBM Security MaaS360 with WatsonWhitepaper Cost savings and business benefits enabled by MaaS360
-
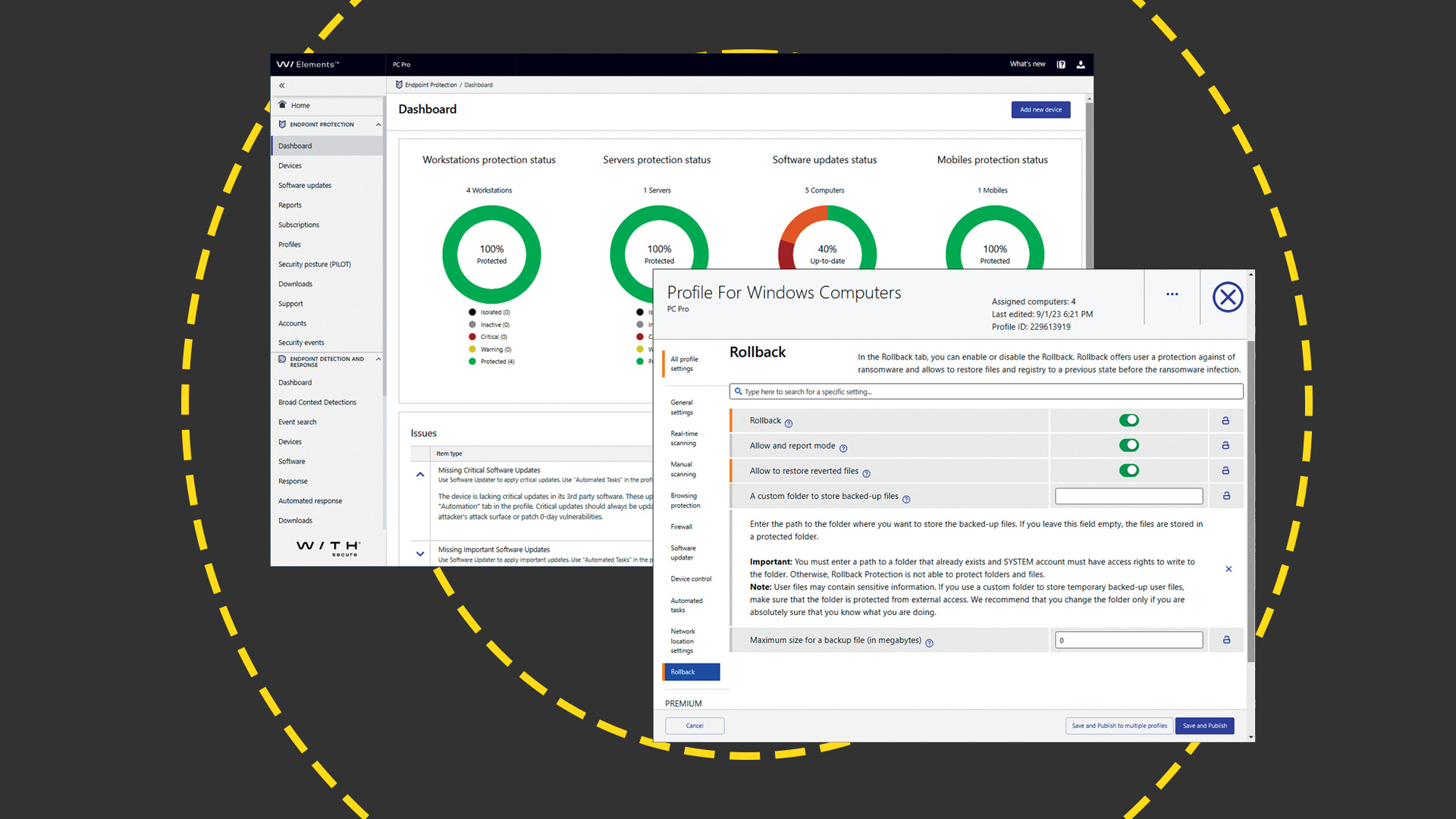 WithSecure Elements EPP and EDR review: Endpoint protection on a plate
WithSecure Elements EPP and EDR review: Endpoint protection on a plateReviews An affordable cloud-managed solution with smart automated remediation services
-
 KuppingerCole leadership compass report - Unified endpoint management (UEM) 2023
KuppingerCole leadership compass report - Unified endpoint management (UEM) 2023Whitepaper Get an updated overview of vendors and their product offerings in the UEM market.
-
 The Total Economic Impact™ of IBM Security MaaS360 with Watson
The Total Economic Impact™ of IBM Security MaaS360 with WatsonWhitepaper Get a framework to evaluate the potential financial impact of the MaaS360 on your organization
-
 Unified endpoint management software vendor assessment
Unified endpoint management software vendor assessmentWhitepaper Make positive steps on your intelligent automation journey


